BEC - Understanding the Identity Crisis in Cybersecurity
Significant risk — action recommended within 24-48 hours
Basically, BEC attacks are tricking people by using fake identities in Google Workspace.
Modern BEC attacks are exploiting Google Workspace identities, creating new risks for organizations. This shift in tactics requires enhanced security measures. Learn how to protect your business.
What Happened
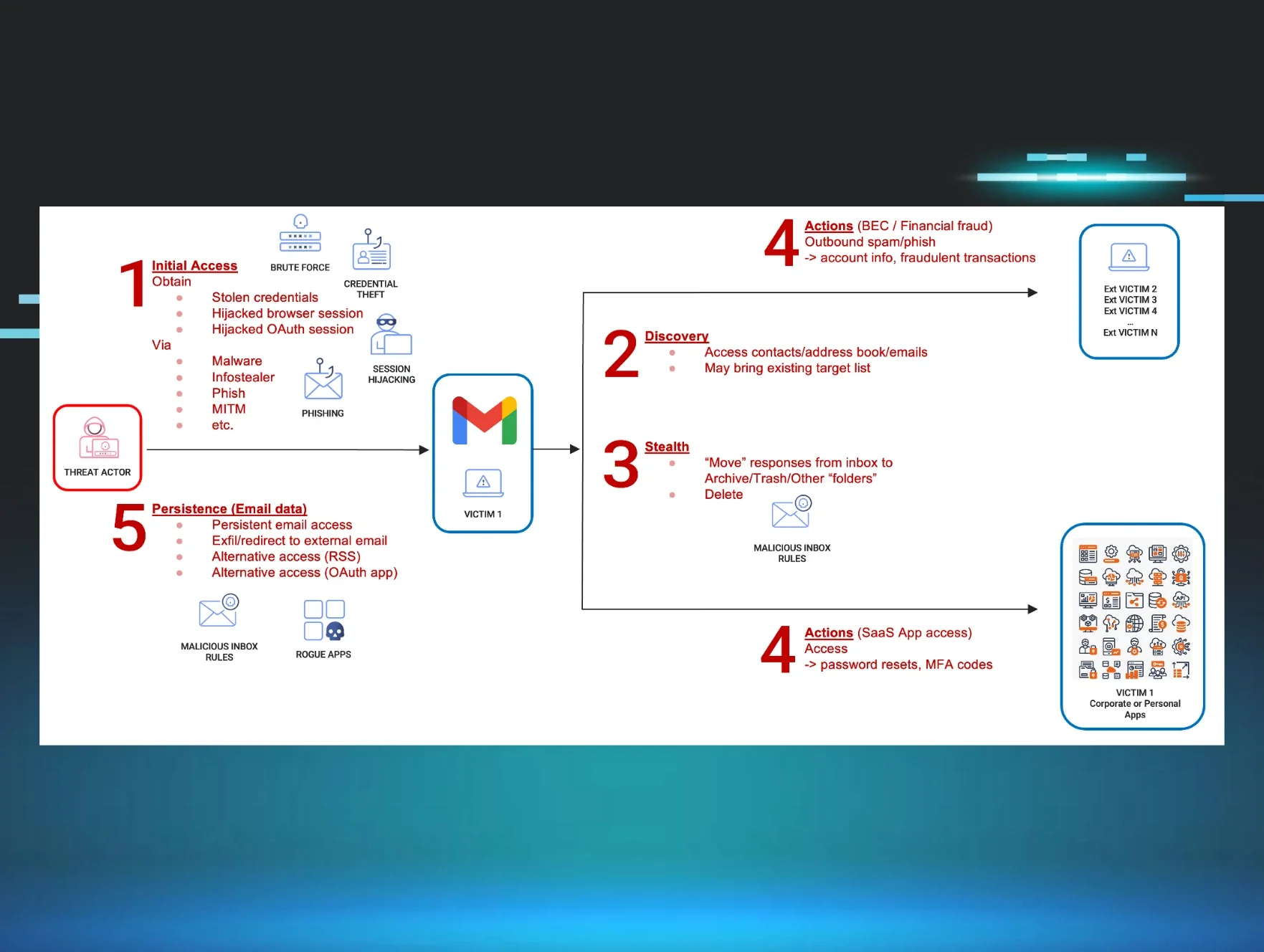
Business Email Compromise (BEC) has become a significant threat in the cybersecurity landscape. Modern attackers are increasingly exploiting Google Workspace identities to carry out their schemes. This evolution highlights a critical shift in how these attacks are conducted, making them more sophisticated and harder to detect.
Why It Matters
The use of legitimate identities from Google Workspace allows attackers to bypass traditional security measures. When an attacker impersonates a trusted employee, they can manipulate others into sharing sensitive information or transferring funds. This not only leads to financial losses but also damages the reputation of the affected organizations.
How BEC Works
BEC attacks typically involve social engineering tactics. Attackers research their targets, often using social media and other online resources, to gather information about employees and their roles. Once they have enough information, they craft convincing emails that appear to come from legitimate sources.
Signs of BEC Attacks
Organizations should be vigilant for several warning signs:
- Unusual requests for sensitive information or funds.
- Emails with slight variations in sender addresses.
- Urgent language that pressures the recipient to act quickly.
How to Protect Yourself
To safeguard against BEC attacks, organizations should implement the following measures:
- Multi-Factor Authentication (MFA): Enforce MFA for all Google Workspace accounts to add an extra layer of security.
- Employee Training: Regularly educate employees about the risks of BEC and how to recognize suspicious emails.
- Email Filtering: Use advanced email filtering solutions to detect and block phishing attempts.
- Verification Procedures: Establish procedures for verifying requests for sensitive actions, especially those involving financial transactions.
By understanding the evolving nature of BEC attacks and implementing robust security measures, organizations can better protect themselves against these identity-driven threats.
🔍 How to Check If You're Affected
- 1.Check for unusual email requests from known contacts.
- 2.Verify sender addresses for discrepancies.
- 3.Monitor financial transactions for unauthorized requests.
🗺️ MITRE ATT&CK Techniques
🔒 Pro insight: The shift to identity-based BEC attacks necessitates a reevaluation of existing security protocols, particularly in cloud environments.