Breach Monitoring - Why Simple Solutions Fail Against Infostealers
Significant risk — action recommended within 24-48 hours
Basically, infostealers are stealing passwords and cookies, and basic security checks aren't enough to stop them.
Infostealers are increasingly bypassing traditional defenses, making basic breach monitoring inadequate. Organizations face significant risks from credential theft, costing millions. A strategic shift is essential for effective protection.
What Happened
In 2026, the threat of stolen credentials has escalated dramatically. Infostealers are harvesting sensitive information like passwords and session cookies, effectively bypassing traditional security measures. A recent survey by Lunar revealed that while 85% of organizations view stolen credentials as a significant risk, many still rely on outdated, checkbox-style solutions for protection.
Who's Affected
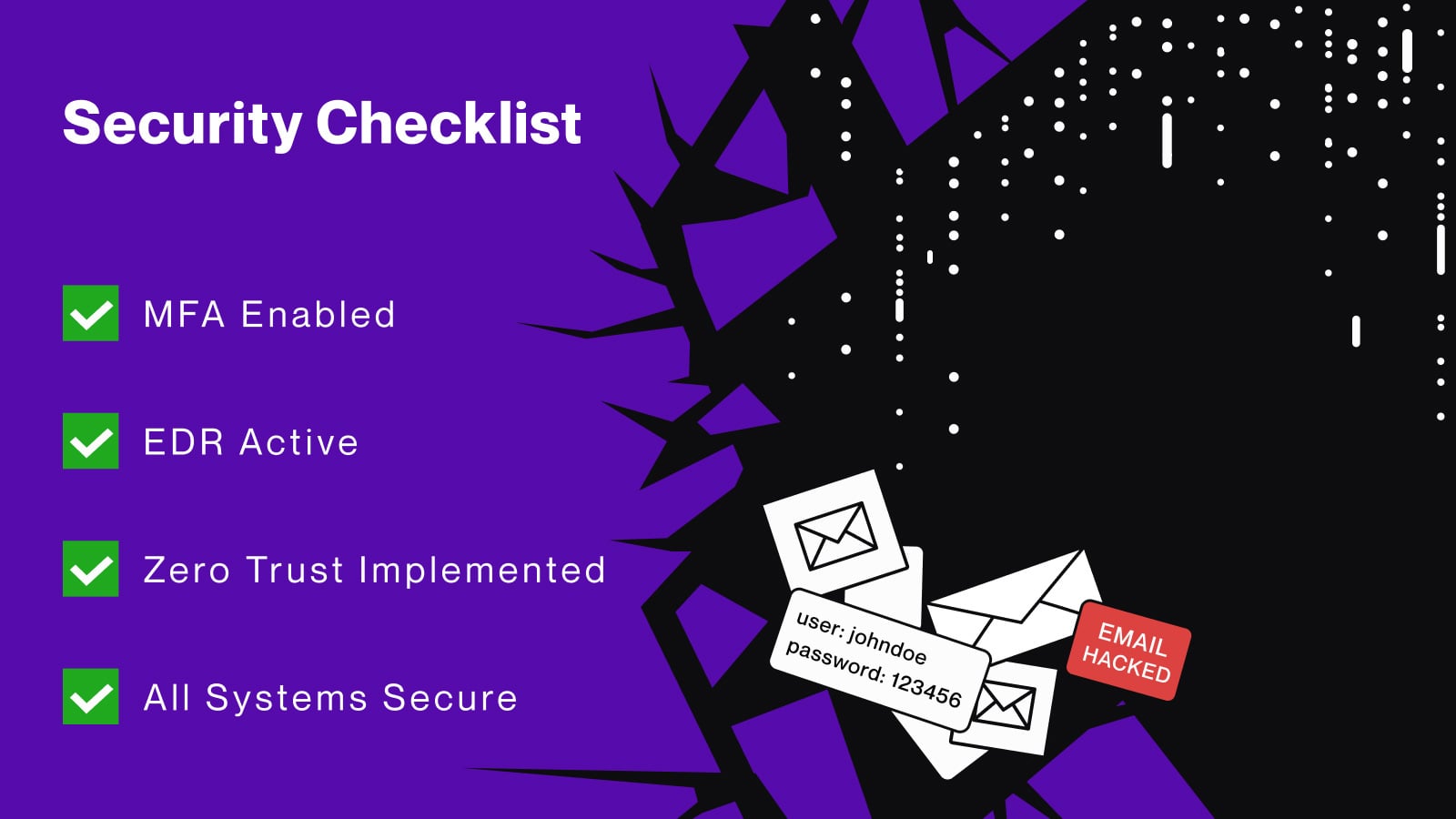
Organizations across various sectors are at risk. The survey found that 62% of respondents ranked credential theft among their top three security priorities. However, many companies mistakenly believe that tools like Multi-Factor Authentication (MFA) and Endpoint Detection and Response (EDR) provide sufficient protection, not realizing their limitations when employees access critical services from unmanaged devices.
What Data Was Exposed
The data at risk includes not just usernames and passwords but also session tokens and cookies. In 2025 alone, Lunar identified 4.17 billion compromised credentials. The implications of these breaches can be severe, with IBM estimating that a breach involving compromised credentials costs organizations between $4.81 million and $4.88 million.
What You Should Do
To effectively combat the infostealer threat, organizations must shift from basic monitoring to a more comprehensive strategy. Here are a few steps to consider:
- Implement Continuous Monitoring: Regular checks are no longer sufficient. Continuous monitoring of breach data and infostealer logs is essential.
- Automate Responses: Utilize automation to reduce false positives and ensure security teams focus on critical threats.
- Integrate Tools: Ensure that monitoring tools integrate with existing security frameworks to enable quick responses to detected threats.
The Infostealer Threat is Much Bigger Than Enterprises Think
Many organizations underestimate the scale of the infostealer threat. Infostealers like LummaC2 and Vidar have been able to bypass enterprise defenses, even in environments that consider themselves secure. The attack process often involves:
- Infection: The victim's device is compromised through various means, including zero-day exploits and malicious software.
- Exfiltration: The infostealer extracts sensitive data from the victim's browser.
- Sale of Data: Stolen credentials are sold on underground markets.
- Network Access: Attackers use valid session tokens to access enterprise networks.
Developing a Mature Breach Monitoring Program
Organizations need to evolve their breach monitoring programs. A mature program includes:
- Continuous Monitoring: A clear view of exposure from various sources.
- Targeted Automation: Reducing noise and focusing on significant threats.
- Integration with Security Stacks: Allowing for swift actions when breaches are detected.
Redefining Breach Monitoring in 2026
As infostealers become more sophisticated, organizations must recognize that traditional monitoring solutions are inadequate. Treating breach monitoring as an ongoing necessity rather than a one-time task will provide the visibility and context needed to respond effectively to credential theft. By adopting a proactive approach, organizations can better protect themselves against the growing threat of infostealers.
🔒 Pro insight: Organizations must transition from reactive to proactive breach monitoring to combat the evolving infostealer threat effectively.