Cisco Source Code and Data Leak Allegedly Claimed by ShinyHunters
Basically, hackers stole a lot of sensitive data from Cisco, including personal information.
ShinyHunters claims responsibility for a major breach at Cisco, exposing over 3 million records. This incident raises serious concerns about data security. Organizations must act quickly to safeguard their information.
What Happened
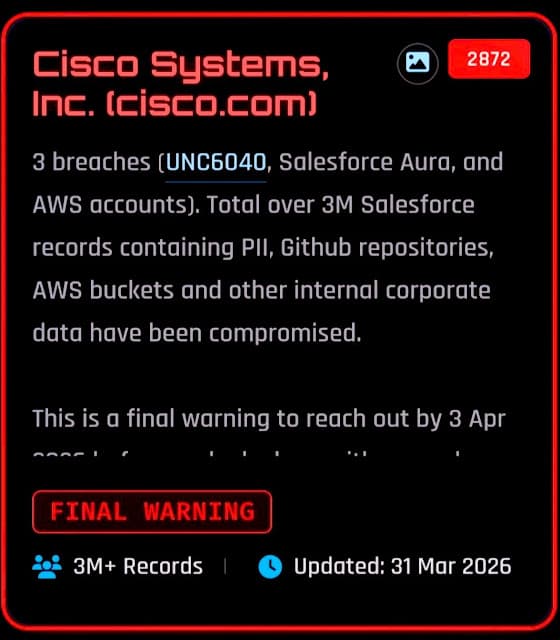
The notorious cybercriminal group ShinyHunters has allegedly claimed responsibility for three significant data breaches targeting Cisco Systems, Inc.. They assert that over 3 million Salesforce records have been compromised, including sensitive personal identifiable information (PII), GitHub repositories, and AWS S3 buckets. Security researcher Dominic Alvieri reported that ShinyHunters issued a 'FINAL WARNING' to Cisco, demanding a response by April 3, 2026, or they would publicly expose the stolen data.
The breaches reportedly stem from three distinct vectors: the Salesforce CRM, Salesforce Aura (Experience Cloud), and AWS account environments. ShinyHunters, which has been active since around 2019, is known for its aggressive data theft and extortion tactics, previously breaching numerous organizations by exploiting misconfigured Salesforce access controls.
Who's Affected
The compromised data includes records of Cisco customers and employees, with alarming ties to personnel from high-profile organizations such as the FBI, DHS, DISA, IRS, and NASA. Additionally, records linked to the Australian Ministry of Defense and several Indian government agencies were also reportedly affected. This data is particularly valuable for adversaries planning targeted phishing or social engineering attacks, as it provides insights into Cisco's operational and client relationships.
ShinyHunters has a history of executing vishing campaigns, tricking employees into granting OAuth token access to malicious Salesforce applications. This method allows attackers to bypass traditional security measures like MFA and password resets, posing a significant risk to organizations.
What Data Was Exposed
The dataset allegedly stolen from Cisco is believed to originate from its Salesforce environment. It contains sensitive information that could be weaponized for various malicious purposes, including supply chain attacks. ShinyHunters is known for its systematic approach to exploiting Salesforce vulnerabilities, having previously breached organizations like Snowflake, Okta, and Google.
The implications of this breach extend beyond just Cisco. The exposed data can facilitate targeted attacks against individuals and organizations, making it crucial for affected entities to take immediate action to mitigate risks.
What You Should Do
Organizations should take proactive measures to protect themselves from similar breaches. Key recommendations include:
- Audit Salesforce OAuth-connected apps to identify any unauthorized access.
- Enforce Salesforce API Access Control to limit exposure.
- Revoke unrecognized tokens and monitor for unauthorized Salesforce Data Loader activity.
Cisco has yet to release an official statement regarding the ShinyHunters extortion claim. As the situation develops, organizations must remain vigilant and prepared for potential fallout from this significant data breach.