🎯Hackers broke into a hospital's computer system and stole a lot of personal information from patients. Now, the hospital is telling those affected and offering help to protect their identities.
What Happened
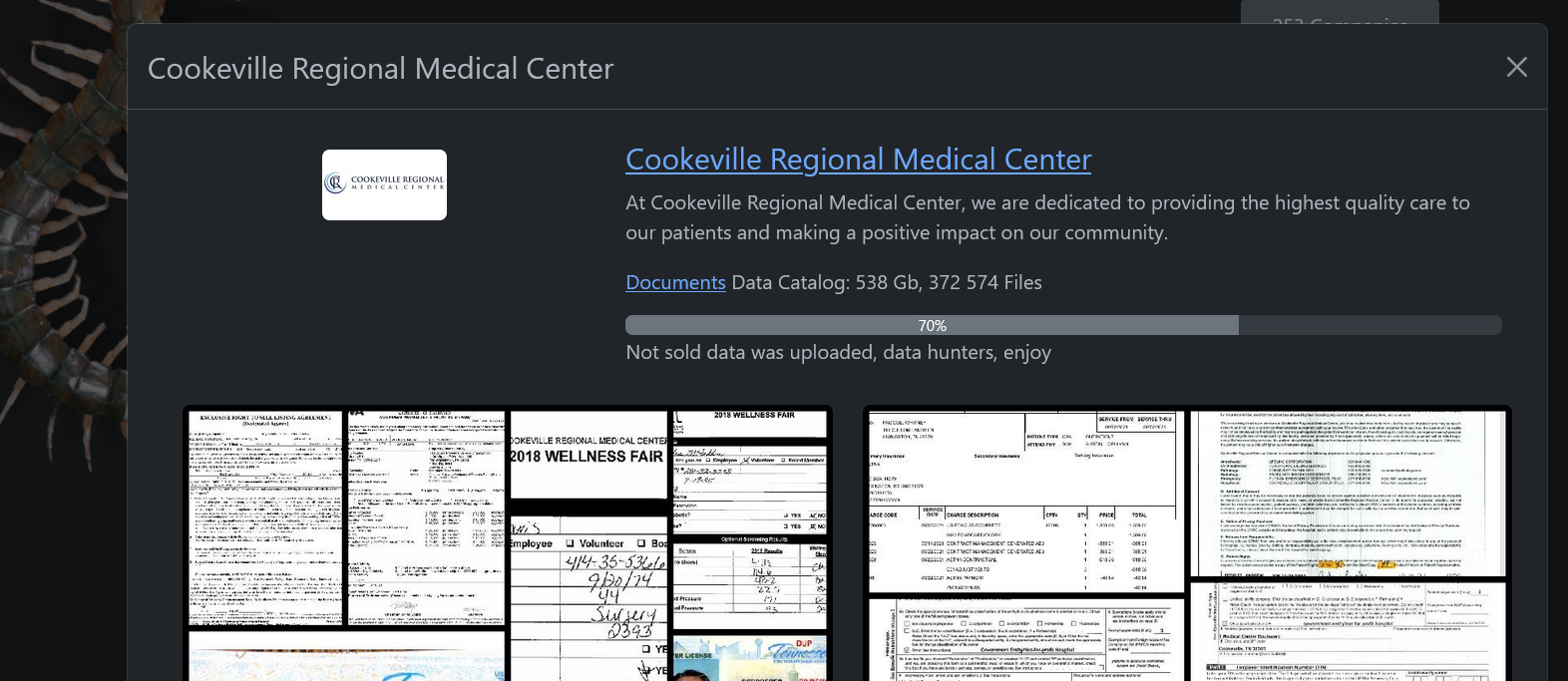
A ransomware attack on Cookeville Regional Medical Center (CRMC) in Tennessee has led to a significant data breach affecting 337,917 individuals. The attack, attributed to the Rhysida ransomware group, occurred between July 11 and July 14, 2025, when hackers infiltrated the hospital's systems and stole approximately 500GB of sensitive information. The breach was confirmed by CRMC in a filing with the Maine Attorney General's Office, and notification letters to affected patients began on April 14, 2026, nearly nine months after the incident was detected.
Who's Affected
The breach has impacted a total of 337,917 patients, including individuals from the Upper Cumberland region, where CRMC serves around 250,000 patients annually across 14 counties. The hospital is offering 12 months of free identity theft protection services through Experian to those affected.
What Data Was Exposed
The compromised data includes a wide range of personal and medical information, such as: This extensive exposure raises significant concerns regarding identity theft and fraud.
Names
Addresses
Dates of birth
Social Security numbers
Driver's license numbers
Financial account details
Medical record numbers
Treatment information
Health insurance data
Additional Context
The Rhysida group, which has been active since May 2023 and is believed to have links to Russia, demanded a ransom of 10 Bitcoin, valued at approximately $1.15 million at the time of the attack. It is currently unclear whether CRMC paid the ransom. The group has also targeted other healthcare organizations, including MedStar Health and Heart South Cardiovascular Group, indicating a troubling trend in ransomware attacks against healthcare providers.
Rebecca Moody, head of data research at Comparitech, noted that the lengthy investigation process reflects the scale of forensic work necessary after such breaches. She emphasized the importance of timely notifications to mitigate the risk of identity theft and phishing campaigns.
What You Should Do
CRMC advises affected individuals to monitor their accounts and credit reports closely, report any suspicious activity, and contact authorities if fraud is suspected. The hospital has implemented additional security measures following the incident to enhance its defenses against future attacks. Patients are encouraged to follow the guidance provided in their notification letters to protect themselves effectively.
The Cookeville breach highlights the growing trend of ransomware attacks targeting healthcare providers, emphasizing the need for robust cybersecurity measures in the sector.



