🎯Basically, a company almost lost everything because their VPN was hacked, but experts saved the day.
What Happened
A small construction manufacturing company found itself on the brink of disaster due to a ransomware attack that exploited a vulnerable VPN. This attack highlighted a common issue: many businesses, especially smaller ones, often neglect basic security measures like multi-factor authentication (MFA). The attackers gained access through the VPN, initiating a sequence of actions that could have led to severe consequences for the company and its local economy.
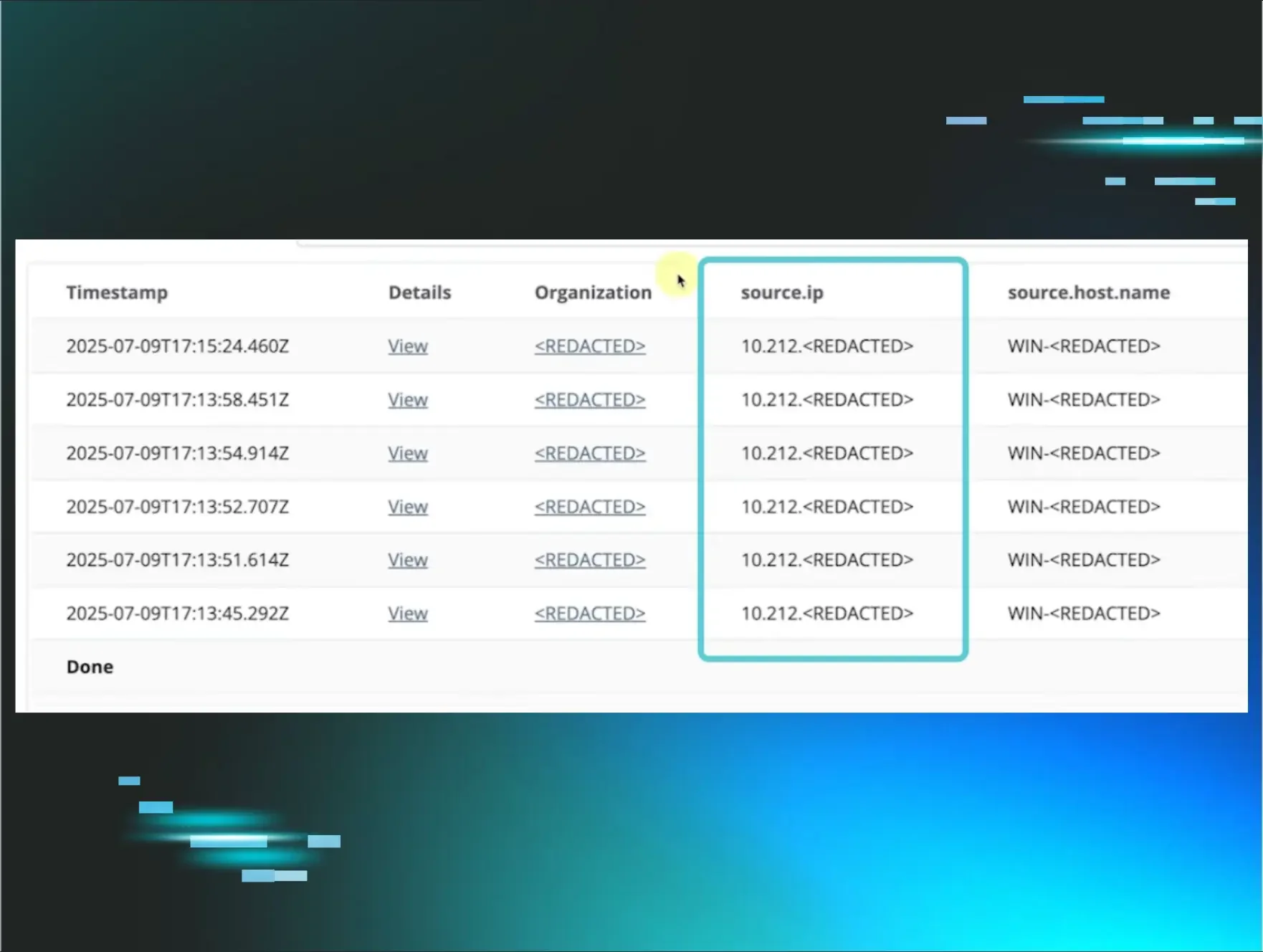
The Huntress Security Operations Center (SOC) detected suspicious activity through their Managed Endpoint Detection and Response (EDR). This prompted a swift investigation, revealing that the attackers had logged in via the VPN, moved laterally within the network, and attempted to disable security tools. The situation was dire, but the response was immediate.
Who's Being Targeted
Small businesses are increasingly becoming prime targets for ransomware attacks. Unlike large corporations, these companies often lack the robust security measures that can deter attackers. In this case, the construction manufacturer played a vital role in its local supply chain, meaning its shutdown could have far-reaching implications for the community. The attackers exploited a single weak point—the unsecured VPN. With nearly half of the environments monitored by Huntress lacking 2FA on their VPNs, the door was wide open for malicious actors. This incident serves as a critical reminder that no business is too small to be targeted.
Signs of Infection
The initial signs of infection came from alerts generated by the EDR, indicating unusual activity. The attackers began with reconnaissance, using Remote Desktop Protocol (RDP) to explore the network for administrator credentials. Once they secured admin access, they attempted to disable critical security tools, but their efforts were thwarted by the vigilance of the Huntress SOC analysts.
The SOC's proactive monitoring and human analysis were key in identifying the threat and isolating the network before significant damage could occur. The attackers were locked out, preventing a potential ransomware deployment that could have crippled the business.
How to Protect Yourself
To safeguard against similar attacks, businesses must prioritize cybersecurity measures. Here are some essential steps: By taking these proactive steps, businesses can bolster their defenses against ransomware and other cyber threats, ensuring they remain resilient in the face of evolving risks.
Detection
- 1.Implement Multi-Factor Authentication (MFA): Ensure that all remote access points, especially VPNs, require MFA to add an extra layer of security.
- 2.Regularly Review Security Protocols: Conduct routine audits of your network to identify vulnerabilities, such as exposed RDP.
Removal
- 3.Develop a Response Plan: Have a clear, rehearsed plan for responding to cyber incidents, ensuring that all team members know their roles.
- 4.Invest in Monitoring Services: Utilize services like Managed EDR to detect and respond to threats in real time.
🔒 Pro insight: This incident underscores the necessity of MFA on VPNs, as attackers increasingly exploit such vulnerabilities for ransomware attacks.





