🎯Basically, identity technology helps businesses manage who can access what information securely.
What Changed
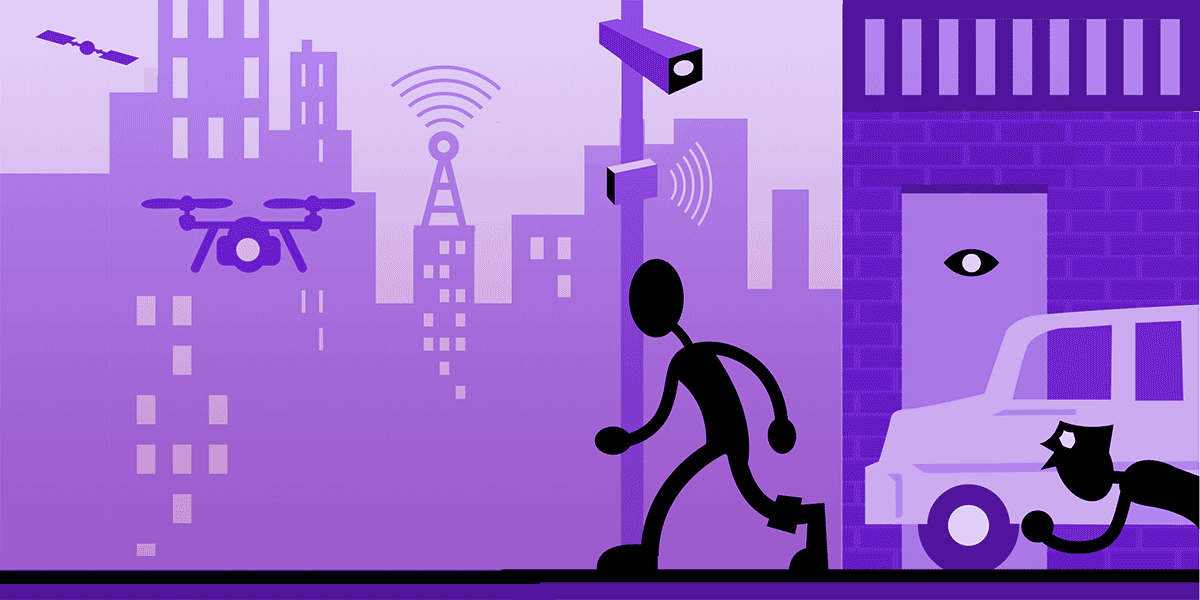
Identity-centric technologies have transformed significantly in recent years. No longer is identity management merely about logging in and out of systems. Today, it serves as the backbone of digital enterprises, acting as the ‘invisible engine’ that powers security and operational efficiency.
How This Affects Your Data
The shift towards identity as the new security boundary means that traditional methods of securing systems are becoming obsolete. With employees working remotely and systems hosted in the cloud, identity verification has replaced location-based trust. This change enhances security by ensuring that access is granted based on verified identity rather than physical presence.
Who's Responsible
Organizations must adopt modern identity frameworks that manage user access efficiently. These frameworks control who can access what, how, and when, thereby reducing errors and increasing accountability. They also help in tracking resource access, which is crucial for maintaining security and compliance.
How to Protect Your Privacy
To leverage identity technologies effectively, businesses should:
Assessment
- 1.Implement real-time identity updates to ensure accurate access control.
- 2.Ensure easy integration with existing systems for seamless operation.
Compliance
The Importance of Identity in Customer Personalization
Identity management is not just about securing employee access; it also plays a vital role in enhancing customer experiences. By managing customer profiles and preferences, businesses can offer personalized services, improving customer satisfaction and loyalty. This holistic approach to identity management enables organizations to build trust and comply with data protection laws, ultimately leading to better business outcomes.
🔒 Pro insight: As identity becomes the new security perimeter, organizations must prioritize real-time identity management to mitigate risks effectively.