🎯Basically, a virus is using a flaw in old routers to take control of them.
What Happened
The Mirai botnet is once again making headlines as it exploits a serious command injection vulnerability, tracked as CVE-2025-29635, in outdated D-Link routers. This vulnerability allows attackers to send specially crafted POST requests that can execute arbitrary commands on the affected devices. Akamai's Security Intelligence and Response Team (SIRT) has reported active exploitation of this flaw, which affects the D-Link DIR-823X series routers, specifically firmware versions 240126 and 24082.
How It Works
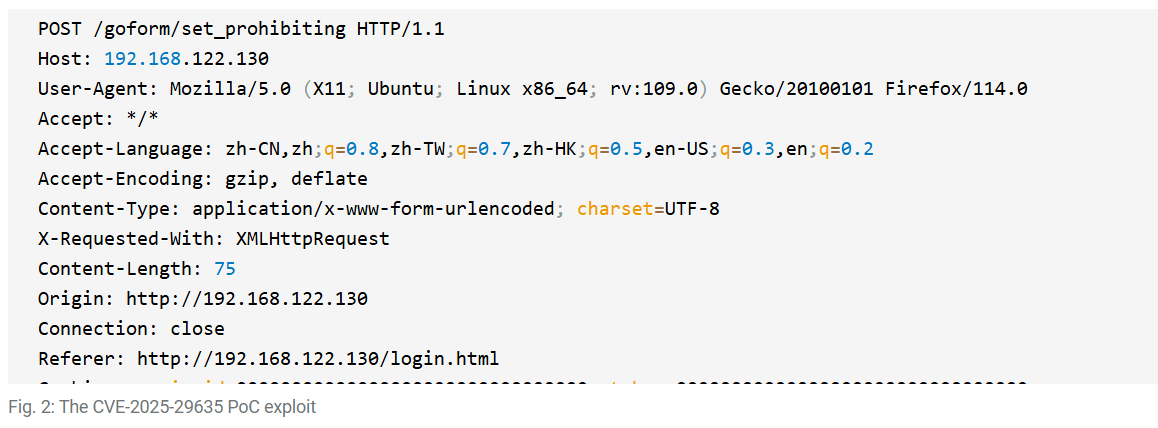
The vulnerability arises from an attacker-controlled value being copied into a command buffer without proper validation. This flaw enables remote execution of commands through a crafted POST request to the router's endpoint /goform/set_prohibiting. Security researchers have noted that exploitation began about a year after the public disclosure of the vulnerability, following the release of a proof of concept (PoC).
Who's Being Targeted
The primary targets are users of the discontinued D-Link DIR-823X routers. Despite these devices being retired in 2025, they remain in use, making them ripe for exploitation. The threat actors are leveraging this vulnerability to deploy variants of the Mirai botnet, which is notorious for creating large networks of compromised devices for malicious purposes.
Signs of Infection
Indicators of compromise include unusual outbound traffic from the routers, particularly connections to known malicious IP addresses. The Mirai variant being used, identified as tuxnokill, has been observed fetching and executing malware from external servers. If users notice unexpected behavior from their routers, such as slow performance or strange network activity, they should investigate further.
How to Protect Yourself
To safeguard against this threat, users should:
Detection
- 1.Update Firmware: Regularly check for and apply firmware updates from D-Link, though many of these devices may no longer receive support.
- 2.Change Default Credentials: Ensure that the default login credentials are changed to strong, unique passwords.
Removal
- 3.Network Monitoring: Implement network monitoring solutions to detect unusual traffic patterns.
- 4.Device Retirement: Consider replacing outdated devices with newer models that receive regular security updates.
Conclusion
The resurgence of the Mirai botnet exploiting CVE-2025-29635 highlights the risks associated with using outdated technology. Organizations and individuals must remain vigilant, regularly monitoring for vulnerabilities and ensuring their devices are secured against potential threats. As attackers continue to target older vulnerabilities, proactive measures are essential to maintain operational security.
🔒 Pro insight: The exploitation of CVE-2025-29635 underscores the persistent threat posed by legacy devices in the IoT landscape.





