NightSpire Ransomware - Analyzing Evolving IOCs and TTPs
Significant risk — action recommended within 24-48 hours
Basically, NightSpire ransomware shows how different hackers can change their methods, making it harder to track them.
A recent NightSpire ransomware incident shows how evolving tactics complicate detection and recovery. Organizations must adapt to these changes to protect their data.
What Happened
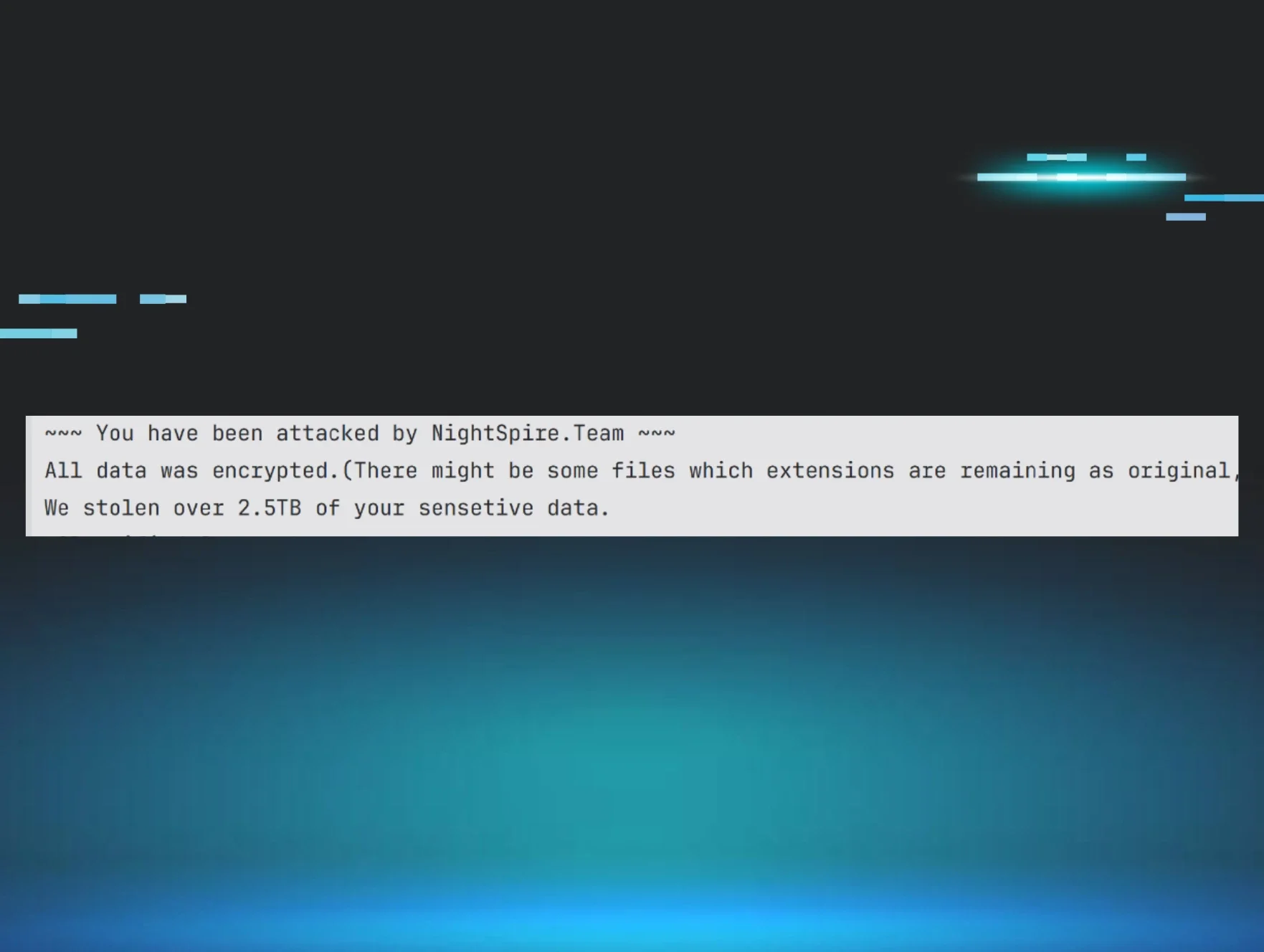
In late March 2026, a new incident involving NightSpire ransomware was reported. The Huntress team detected malicious activity shortly after installing their monitoring agent on a customer's endpoints. This incident highlighted the complexities of the ransomware-as-a-service (RaaS) model and how it affects investigations and recovery efforts.
The Threat
NightSpire ransomware, first identified in February 2025, has sparked debate about whether it operates under a RaaS model. Some researchers suggest it is a closed operation, while others believe it has evolved into a RaaS structure. This uncertainty complicates how defenders approach the threat.
Who's Being Targeted
Organizations across various sectors are at risk, especially those lacking robust cybersecurity measures. The evolving tactics of ransomware affiliates mean that attacks can vary significantly, even if they use the same ransomware variant.
Signs of Infection
In the recent incident, the threat actor gained access via Remote Desktop Protocol (RDP) before the Huntress agent was installed. They installed various tools for persistence and data exfiltration, including Chrome Remoting Desktop and MEGASync. This indicates a sophisticated approach to maintaining footholds within the network.
How It Works
The NightSpire ransomware employs a variety of tactics, techniques, and procedures (TTPs) that can differ from one attack to another. For instance, the ransomware has been observed to utilize embedded commands to delete system recovery options, making recovery more difficult for victims. This adaptability is a hallmark of modern ransomware operations.
What You Should Do
To protect against NightSpire and similar threats:
- Implement strong access controls: Limit RDP access and enforce multi-factor authentication.
- Monitor for unusual activities: Keep an eye on endpoint behaviors, especially after installing security agents.
- Educate employees: Train staff to recognize phishing attempts and suspicious downloads.
Conclusion
The NightSpire ransomware incident serves as a reminder of the evolving landscape of cyber threats. As ransomware tactics continue to change, organizations must remain vigilant and adaptable in their cybersecurity strategies. Understanding the intricacies of RaaS and the varying TTPs associated with different affiliates can significantly enhance incident response and recovery efforts.
🔍 How to Check If You're Affected
- 1.Check for unusual RDP access logs in your environment.
- 2.Monitor for the installation of unexpected applications like Chrome Remoting Desktop.
- 3.Review endpoint activity for signs of data exfiltration or file encryption.
🗺️ MITRE ATT&CK Techniques
🔒 Pro insight: The variability in TTPs among ransomware affiliates necessitates a dynamic response strategy to effectively mitigate risks.