🎯Basically, Trail of Bits found a way to improve a quantum security proof by exploiting code vulnerabilities.
What Happened
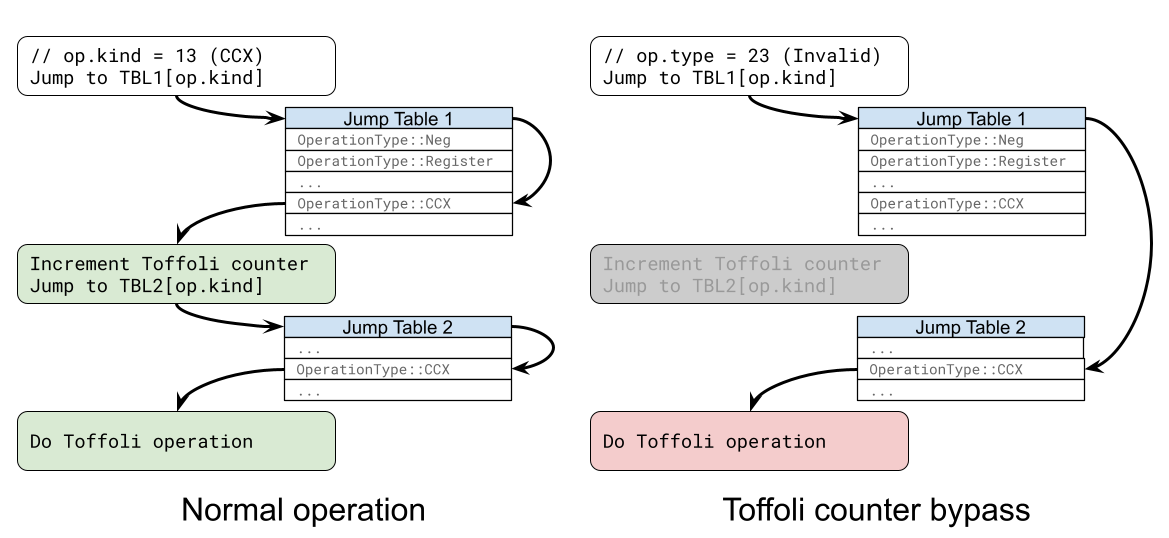
Two weeks ago, Google's Quantum AI group published a groundbreaking zero-knowledge proof claiming that first-generation quantum computers could break elliptic curve cryptography keys in just 9 minutes. Today, Trail of Bits has released their own proof that significantly outperforms Google's in all key metrics. This improvement is not due to any new quantum breakthroughs but rather the exploitation of subtle memory safety and logic vulnerabilities in Google's Rust prover code.
The Development
Google's proof utilized a zero-knowledge virtual machine (zkVM) to assess the cost of a quantum circuit based on three critical metrics: the total number of operations, the Toffoli gate count, and the number of qubits. Trail of Bits' proof improves on these metrics, demonstrating a total of 8.3 million operations and 1,164 qubits compared to Google's 17 million operations and 1,425 qubits.
Security Implications
This development underscores the unique attack surface that arises when using zero-knowledge proofs in quantum cryptography. By exploiting vulnerabilities in the Rust code, Trail of Bits was able to create a proof that is cryptographically indistinguishable from one that results from actual algorithmic improvements. This raises questions about the security of systems that rely on such proofs and the potential for similar exploits in other implementations.
Industry Impact
The implications of this advancement are significant for the field of quantum cryptography. As quantum computing technology evolves, the risk associated with memory safety and logic vulnerabilities in cryptographic proofs will need to be addressed. This incident serves as a reminder that even established systems can have exploitable weaknesses, and ongoing vigilance is necessary.
What to Watch
As the landscape of quantum security continues to evolve, stakeholders in the industry should closely monitor developments in zero-knowledge proofs and the security of implementations. Future improvements may require a more robust approach to coding practices, particularly in languages like Rust that allow for unsafe operations. Additionally, organizations should consider conducting thorough security audits of their quantum cryptographic systems to identify and mitigate potential vulnerabilities.
🔒 Pro insight: This breakthrough emphasizes the critical need for robust coding practices in quantum cryptography to mitigate potential vulnerabilities.