UAC-0255 - Phishing Campaign Spreads AGEWHEEZE Malware
Basically, hackers pretended to be a security agency to trick people into downloading harmful software.
A phishing campaign impersonating CERT-UA has spread AGEWHEEZE malware, targeting over 1 million users. Victims were tricked into installing a fake security tool. This incident underscores the need for enhanced cybersecurity measures.
What Happened
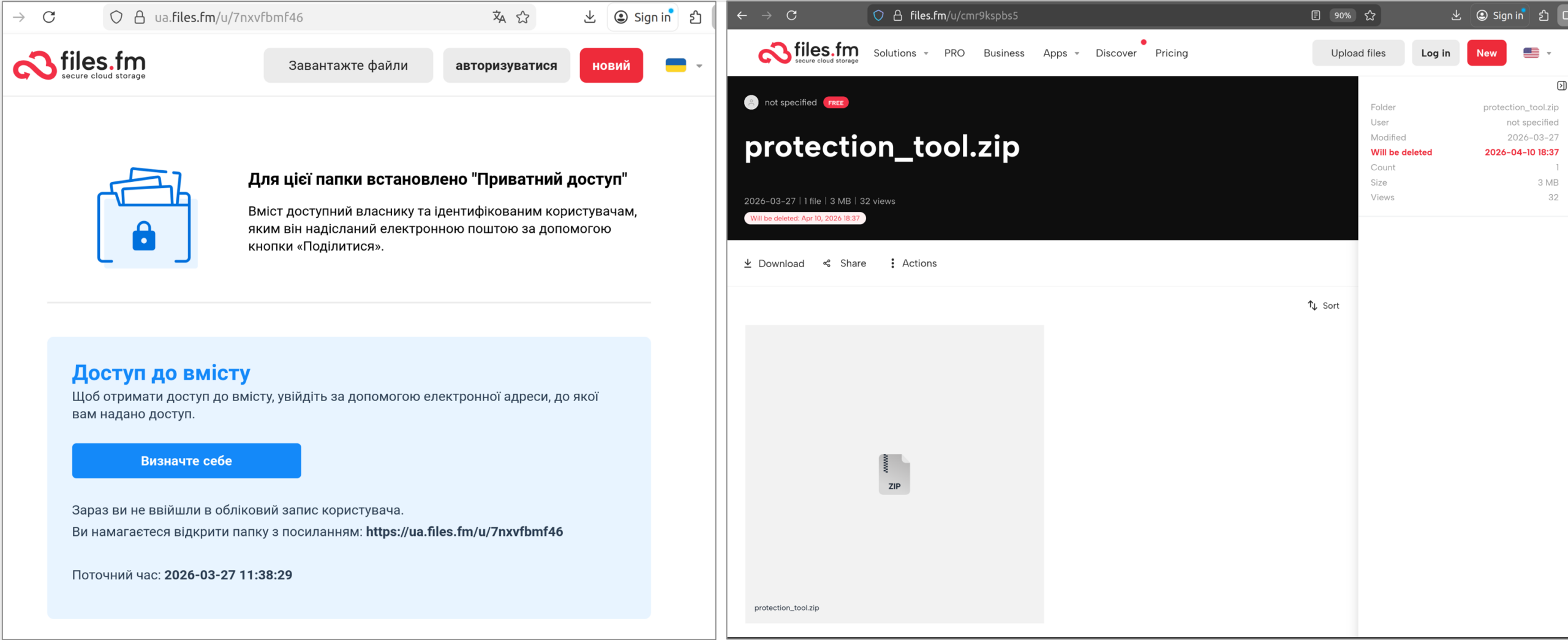
A new phishing campaign has emerged, led by the threat actor UAC-0255, impersonating the Ukrainian cybersecurity agency CERT-UA. This campaign targeted approximately 1 million users, urging them to download a password-protected archive from Files.fm. Victims were misled into installing what they believed was a legitimate security tool, but it was actually the AGEWHEEZE malware.
Who's Affected
The phishing emails were sent to a wide range of targets, including government organizations, medical centers, security companies, educational institutions, and financial institutions. While the attackers claimed to have infected over 200,000 devices, the actual impact was limited, with only a few devices in educational institutions being compromised.
How It Works
The AGEWHEEZE malware is a multifunctional remote access tool that allows attackers to control infected systems. Once installed, it can execute commands, manage files, capture screens, and even steal clipboard data. The malware maintains persistence by embedding itself in system startup processes and registry entries. It communicates with its command server via WebSockets, making it a potent threat for the affected systems.
Tactics & Techniques
The attackers created a fake website, cert-ua[.]tech, mimicking the real CERT-UA site, to distribute the AGEWHEEZE malware. This site contained links to a Telegram channel claiming responsibility for the attack, further confirming attribution to UAC-0255. The use of a password-protected archive and the guise of a security tool were key tactics in this campaign, showcasing the evolving methods of cybercriminals.
Defensive Measures
Experts from CERT-UA have been actively working to contain the spread of this malware. They emphasize the importance of reducing attack surfaces and utilizing security tools like AppLocker. Organizations are urged to strengthen their defenses against such phishing campaigns and to remain vigilant against suspicious emails.
Conclusion
This incident highlights the increasing sophistication of cyberattacks, particularly those leveraging AI technologies. As attackers become more adept at impersonating trusted entities, it is crucial for users and organizations to stay informed and proactive in their cybersecurity measures.