🎯Basically, hackers are using a flaw in Bomgar software to attack companies and spread ransomware.
What Happened
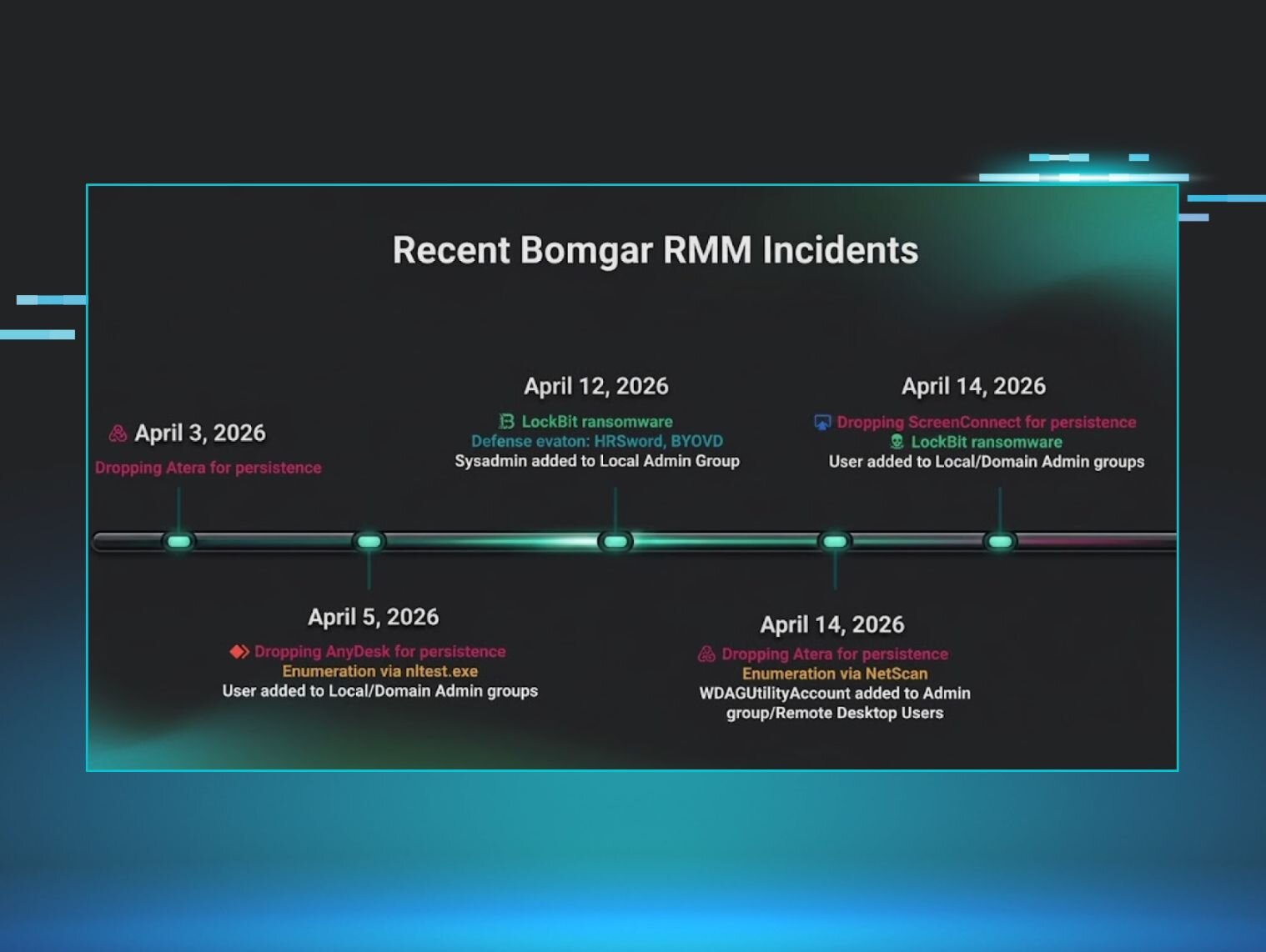
Over the past two weeks, the Huntress Security Operations Center (SOC) has reported a significant increase in incidents involving compromised Bomgar remote monitoring and management (RMM) instances. This uptick follows the disclosure of a critical vulnerability, CVE-2026-1731, by BeyondTrust in February 2026. The vulnerability allows unauthenticated attackers to execute code remotely, leading to potential exploitation of the affected systems.
Who's Being Targeted
The compromised Bomgar instances primarily belong to organizations that utilize remote support for their operations. Notably, incidents have affected a dental software company and a Managed Service Provider (MSP), which subsequently impacted numerous downstream clients. This highlights the ripple effect of such compromises, where one breach can lead to widespread consequences for multiple businesses.
Signs of Infection
Indicators of compromise (IoCs) have been identified, including malicious processes stemming from bomgar-scc.exe and the deployment of ransomware such as LockBit. Security analysts observed that attackers often create new administrator accounts, perform network reconnaissance, and install additional remote access tools like AnyDesk to maintain persistence within the network.
How to Protect Yourself
Organizations using Bomgar RMM should take immediate action to mitigate risks: By implementing these measures, organizations can significantly reduce the risk of exploitation and protect their assets from potential ransomware attacks.
Detection
- 1.Apply patches for CVE-2026-1731 as soon as possible.
- 2.Monitor for suspicious user activity in Local Administrators and Domain Administrators groups.
Removal
- 3.Audit RMM tools to ensure only authorized software is in use, referencing resources like LOLRMM.
- 4.Check logs for unusual RMM executions and verify the versions of Bomgar software in use.
🔒 Pro insight: The resurgence of attacks exploiting CVE-2026-1731 underscores the need for proactive patch management and continuous monitoring of RMM environments.