🎯Basically, AES 128 encryption is still safe even with quantum computers around.
What Happened
With the rise of quantum computing, many have expressed concerns about the security of existing encryption methods. Filippo Valsorda, a cryptography engineer, has addressed a common myth: AES 128 is still secure in a post-quantum world. This misconception has led to unnecessary fears that could divert focus from crucial cryptographic updates.
The Flaw in the Myth
People often believe that quantum computers will halve the effectiveness of symmetric keys like AES 128, suggesting that a shift to AES 256 is necessary. Valsorda argues that this interpretation of quantum algorithms, particularly Grover's algorithm, is misleading. While Grover's algorithm does provide a speedup in brute-force searches, it does not operate in the same manner as classical searches.
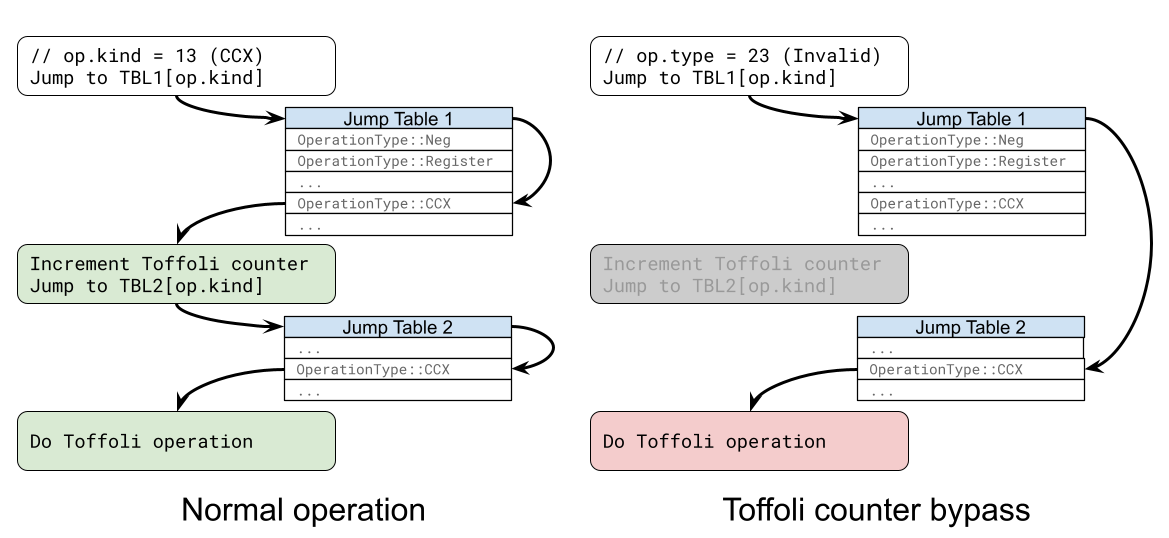
How Grover's Algorithm Works
In classical computing, tasks can be parallelized effectively. For instance, if you have 256 possible combinations for a lock, splitting the workload among friends can significantly reduce the time needed to find the correct combination. However, Grover's algorithm operates differently. It requires a long-running serial computation, meaning that parallelization does not yield the same benefits. This results in a much higher effective cost for attacks on AES 128 than previously assumed.
The Real Cost of Attacks
Valsorda illustrates this with a simple analogy. If you have a lock with 256 combinations, a classical attack would take 256 tries. If you enlist help, you can divide the work and finish faster. In contrast, Grover's algorithm would only allow a quantum computer to check a limited number of combinations in parallel, making the attack slower overall. This means that the actual cost to break AES 128 is much higher than the simplified calculations suggest, making it secure against quantum threats.
Recommendations from Experts
Numerous sources, including the National Institute of Standards and Technology (NIST), support Valsorda's assertion that AES 128 is acceptable in a post-quantum world. However, the NSA recommends AES 256 for specific use cases, primarily to avoid fragmentation in security levels. Valsorda emphasizes that the focus should remain on updating asymmetric algorithms vulnerable to quantum attacks, rather than on unnecessary changes to symmetric encryption.
Conclusion
In conclusion, the fear that quantum computing will undermine AES 128 security is largely unfounded. By understanding the mechanics of quantum algorithms and their implications, engineers can better prepare for the challenges posed by quantum computing without being distracted by myths. As Valsorda aptly states, it is essential to focus on the real work needed to secure our cryptographic systems against future threats.
🔒 Pro insight: Misconceptions about AES 128's vulnerability to quantum attacks could misallocate resources needed for critical cryptographic updates.