App Domain Manager Injection - Understanding the Threat
Significant risk — action recommended within 24-48 hours
Basically, attackers manipulate .NET apps to run harmful code without being noticed.
Attackers are exploiting App Domain Manager injection to run harmful code in trusted .NET applications. This poses serious security risks. Learn how to detect and prevent these attacks.
The Flaw
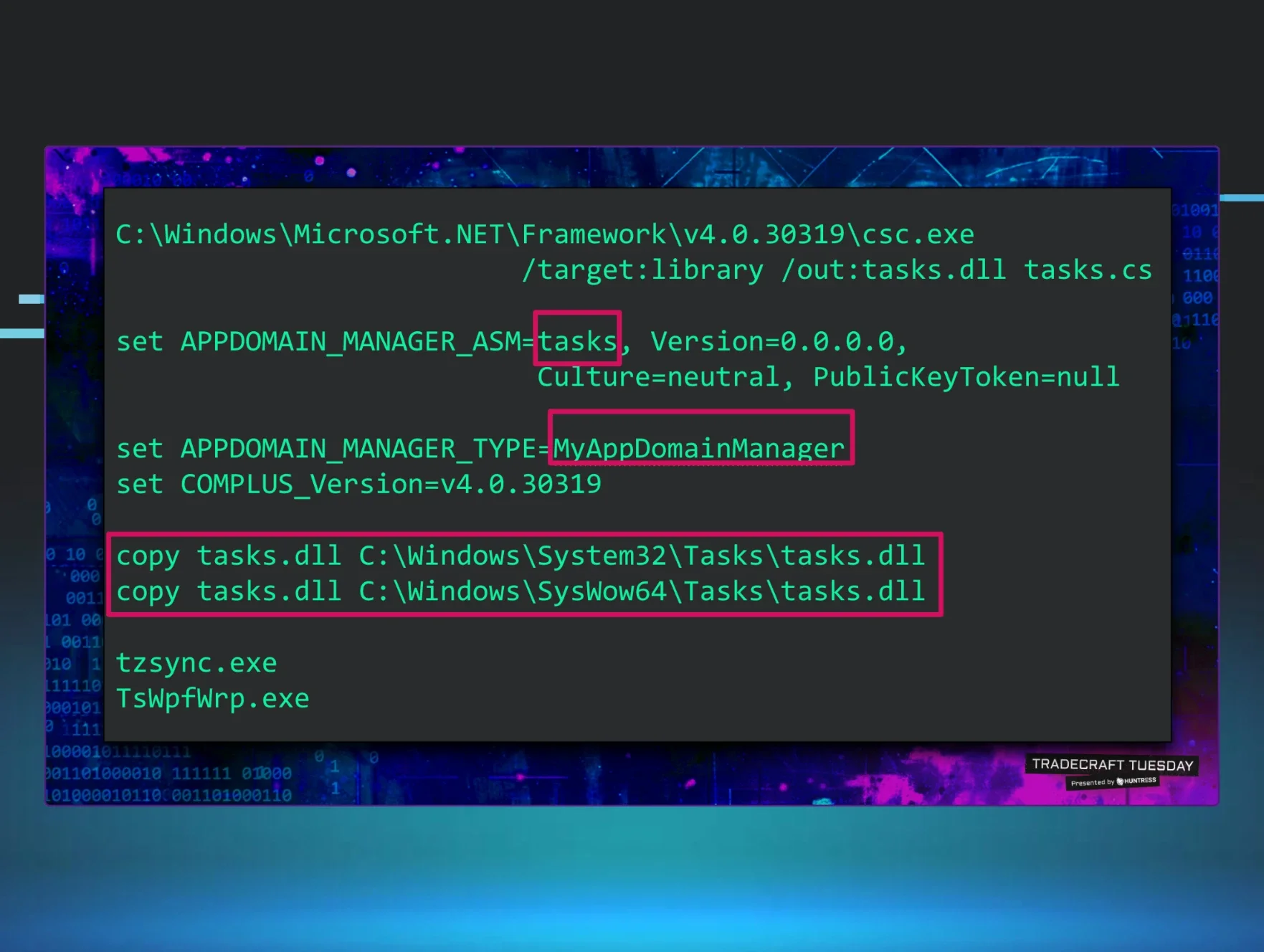
App Domain Manager injection is a sophisticated attack technique that allows malicious actors to execute code within trusted .NET applications. By modifying configuration files, attackers can bypass application security controls, making it difficult for standard defenses to detect their activities.
What's at Risk
This vulnerability targets .NET applications, which are widely used in various sectors, including finance, healthcare, and technology. If exploited, it can lead to unauthorized access, data breaches, and the compromise of sensitive information.
Patch Status
Currently, there are no specific patches available for this type of injection vulnerability. However, developers and security teams are encouraged to implement best practices in application security to mitigate risks.
Immediate Actions
Organizations should take proactive steps to protect their .NET applications:
- Review configuration files regularly to ensure they haven't been tampered with.
- Implement strict access controls to limit who can modify application settings.
- Conduct security audits to identify potential vulnerabilities in your applications.
- Educate developers on secure coding practices to prevent such vulnerabilities from being introduced in the first place.
Detection Strategies
To effectively detect App Domain Manager injection attempts, consider the following strategies:
- Monitor application logs for unusual activity, particularly around configuration changes.
- Utilize intrusion detection systems (IDS) to flag suspicious behavior.
- Regularly update security protocols and tools to stay ahead of evolving threats.
By understanding and addressing the risks associated with App Domain Manager injection, organizations can significantly enhance their application security posture and protect against potential exploits.
🔍 How to Check If You're Affected
- 1.Monitor application logs for unauthorized configuration changes.
- 2.Implement intrusion detection systems to identify suspicious activities.
- 3.Regularly review access controls and permissions for application settings.
🔒 Pro insight: The stealthy nature of App Domain Manager injection requires enhanced monitoring and proactive security measures to mitigate potential exploits.