Burp AI: Rapid Functional PoCs in Under a Minute!
Basically, Burp AI can help security testers create proof-of-concept attacks super quickly.
Julen Garrido Estévez tests Burp AI's ability to create proof-of-concept attacks in under a minute. This breakthrough could revolutionize penetration testing, making it faster and more efficient. Security professionals should consider integrating this tool into their workflows for better results.
What Happened
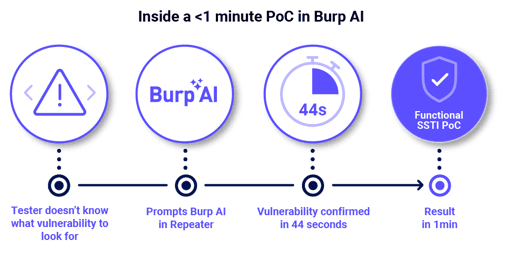
Imagine being able to create functional proof-of-concept (PoC)? attacks in less than a minute. Julen Garrido Estévez, a skilled pentester, recently tested the capabilities of Burp AI, a tool designed to assist security professionals in identifying vulnerabilities. His findings are not just intriguing; they could change the way pentesters approach their work.
During his evaluation, Garrido demonstrated how Burp AI can streamline the process of generating PoCs. Traditionally, this task can be tedious and time-consuming, requiring extensive knowledge and manual effort. However, with Burp AI, he was able to produce effective PoCs rapidly, showcasing its potential to enhance efficiency? in penetration testing?.
The results were impressive. Garrido shared various examples that illustrated how Burp AI simplifies complex tasks. This includes generating scripts and automating repetitive processes, which allows pentesters to focus on more critical aspects of their assessments. The speed and accuracy of Burp AI could significantly reduce the time spent on vulnerability assessments.
Why Should You Care
If you're a security professional, this could be a game-changer for your workflow. Think about how much time you spend on manual tasks. With tools like Burp AI, you can reclaim hours and focus on improving your overall security posture.
For businesses, faster vulnerability assessments? mean quicker remediation of potential threats. This is crucial in today’s fast-paced digital landscape where cyber threats are constantly evolving. The key takeaway is that adopting advanced tools like Burp AI can enhance your security efforts and save valuable resources.
What's Being Done
The cybersecurity community is buzzing about Garrido's findings. Many are eager to integrate Burp AI into their testing methodologies. Here are a few steps you can take if you're interested in leveraging this technology:
- Explore Burp AI’s features and capabilities.
- Attend workshops or webinars to learn from experts like Garrido.
- Experiment with Burp AI in your own testing environments to see its potential firsthand.
Experts are closely monitoring how Burp AI evolves and its impact on penetration testing? practices. As more professionals adopt this tool, we can expect to see innovative approaches to vulnerability assessments? emerge.
PortSwigger Blog