Tools & Tutorials News
Elevate your cybersecurity skillset with our curated tools and tutorials. Discover open-source threat hunting utilities, master reverse-engineering frameworks, and follow step-by-step guides designed for both aspiring ethical hackers and veteran security professionals.

AI SOC Customization - Why Your Security Needs Control
AI SOCs must be customizable to meet unique security needs. Rigid systems can hinder effectiveness, leading to operational challenges. Learn how to choose the right AI SOC.

Decipio - New AI Tool to Catch Credential Theft Early
Arctic Wolf has launched Decipio, a new AI tool designed to detect credential theft in real-time, providing a proactive defense against cyberattacks.

Syncthing - Secure and Private File Synchronization Tool
Syncthing is a free tool for secure file synchronization across devices. It uses a peer-to-peer model to keep your data private and under control. With automatic updates and encryption, it's a trusted solution for file sharing.
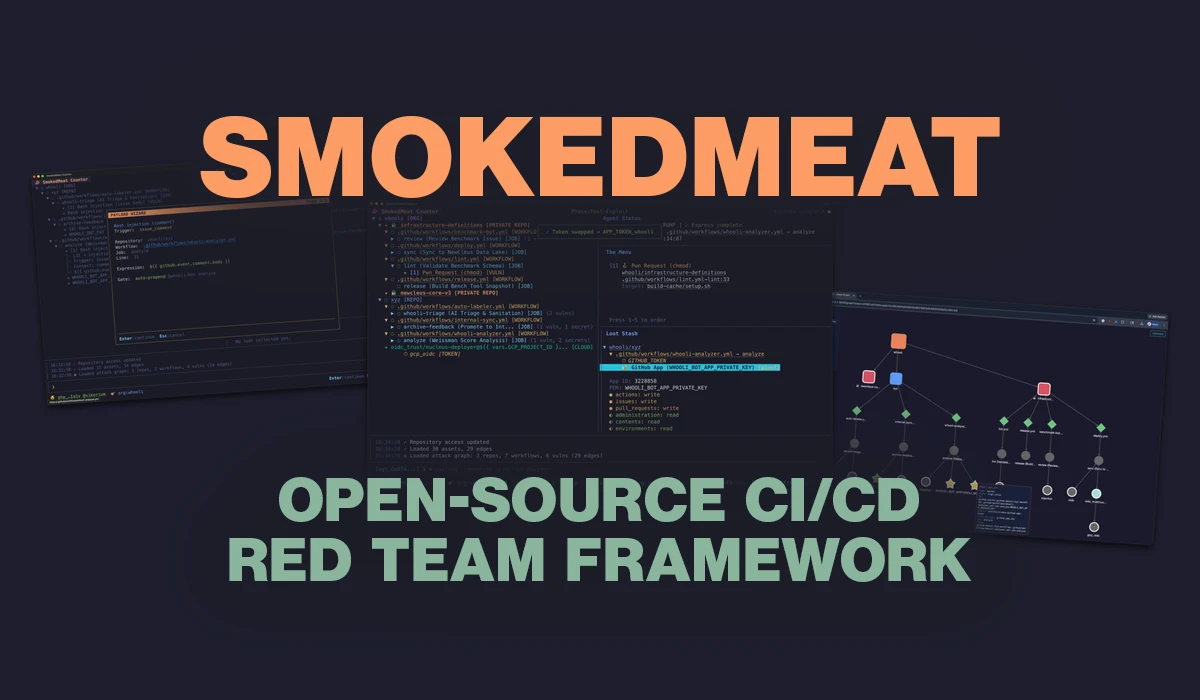
SmokedMeat - New Tool Demonstrates CI/CD Attack Scenarios
Boost Security has launched SmokedMeat, a tool that simulates attacks on CI/CD pipelines. This open-source framework helps teams visualize vulnerabilities and improve their security measures. Available for free on GitHub, it aims to enhance awareness and remediation of potential threats.

Dungeons and Daemons - Experience Cybersecurity as a Game
Dungeons and Daemons is a cybersecurity RPG that lets you play as a Red Team operator. Infiltrate corporate facilities and use real attack techniques. It's a fun way to learn about cybersecurity while gaming!

Security Mindsets - 6 Mindsets to Abandon Now
Cybersecurity professionals are often trapped in harmful mindsets. This article reveals six mindsets to abandon for better outcomes and reduced burnout. Embrace a healthier approach to security today!

SHE@CYBER - Training Model Expands Beyond EU Funding
The SHE@CYBER program is gaining traction in Poland and North Macedonia, promoting women's participation in cybersecurity. This expansion follows the end of EU funding, showcasing its sustainability. The program offers free access to training materials until 2028, encouraging more women to enter the field.

Microsoft Teams - Right-Click Paste Bug Caused by Edge Update
A bug in Microsoft Teams, caused by a recent Edge update, has disabled the right-click paste function for users on Windows and macOS. Microsoft is rolling out a fix while recommending temporary workarounds.
Third-Party Notices - Addressing Compliance Challenges
Third-party notices are failing under modern software demands, impacting compliance and security. A new framework aims to transform these notices into structured security intelligence. This could close significant visibility gaps in software supply chains.

Proxy Server - Understanding Its Role in Network Security
Learn about proxy servers and their role in network security. They help control access and improve performance while hiding user identities. However, they also introduce risks.
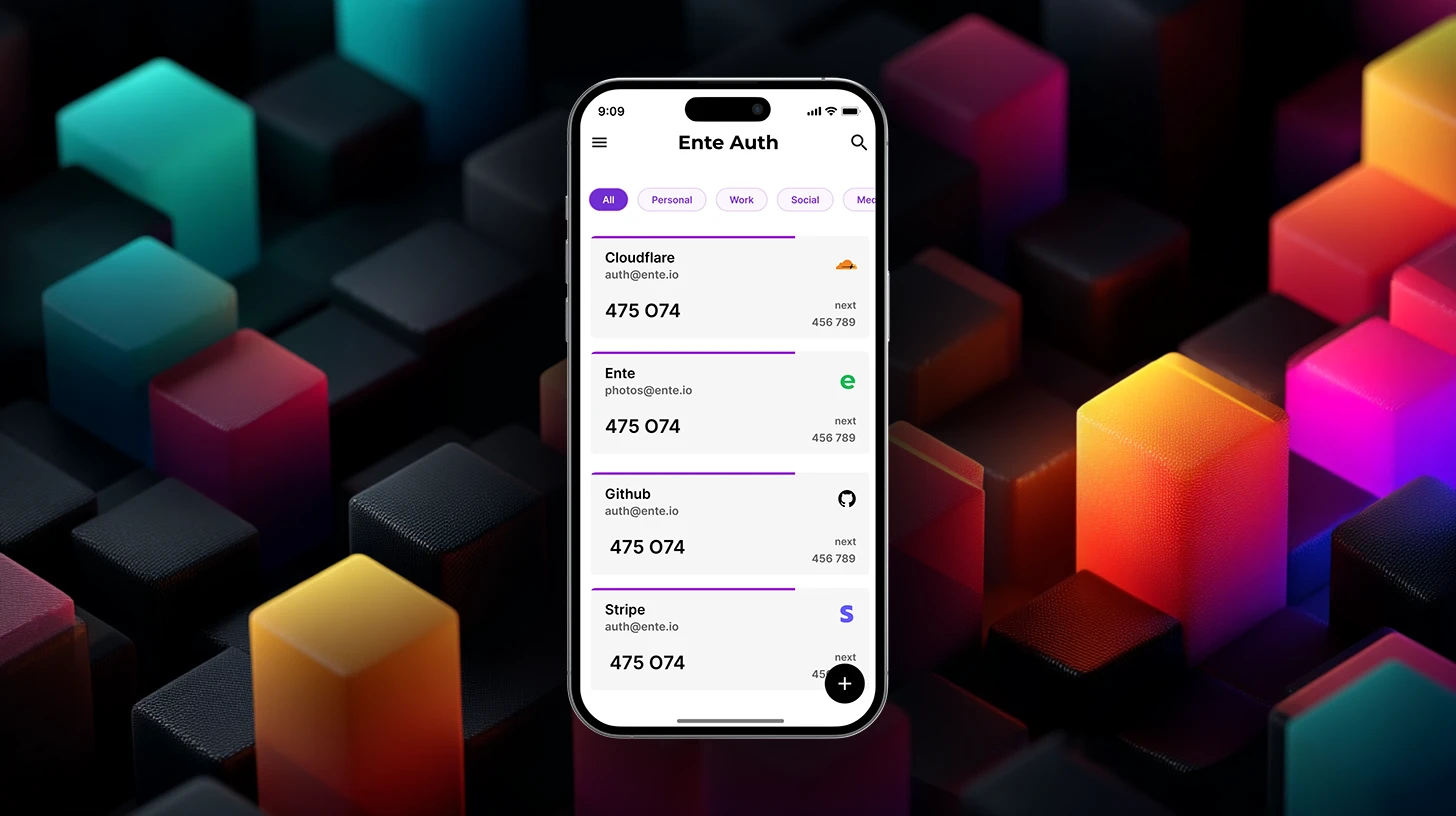
Ente Auth - Simplifying 2FA Management and Security
Ente Auth is a free, open-source app that simplifies managing your 2FA codes. It securely generates, backs up, and syncs codes across devices. With offline functionality and encrypted backups, it ensures your data stays safe and accessible.
Threat Intelligence - Essential Integration Workflows Explained
Recorded Future shares four essential workflows for integrating threat intelligence into your security stack. These workflows help organizations improve their cybersecurity maturity and operational efficiency. Discover how to move from reactive to autonomous threat operations.
Secure by Design - Building Cybersecurity into Foundations
Secure by Design emphasizes embedding security into software development. This proactive approach helps reduce vulnerabilities and protects users effectively. Sophos leads the charge, ensuring security is prioritized from the start.

GitHub Actions - Updated Guide for Enhanced Security
A new guide has been released to enhance security for GitHub Actions workflows. Following recent attacks, developers can learn vital practices to protect their projects. This is essential for anyone using GitHub Actions in their CI/CD pipelines.

Bitdefender - Launches GravityZone Email Threat Protection
Bitdefender has launched GravityZone Extended Email Security to combat modern email threats. This unified platform protects against phishing, BEC, and ransomware. It's designed for organizations and MSPs, enhancing email security and streamlining management.

Legitify - Open-Source Scanner for Security Misconfigurations
Legitify is an open-source tool that scans GitHub and GitLab for security misconfigurations. It helps organizations identify vulnerabilities in their settings, enhancing overall security. By improving visibility into potential risks, Legitify plays a crucial role in safeguarding software supply chains.

Outsourcing MDR - 4 Key Questions for Cyber Resilience
As cyber threats grow, outsourcing Managed Detection and Response (MDR) can enhance security. Learn four essential questions to ensure it fits your strategy and improves resilience.

Security Risk Advisors - Purple Team Earns CPE Credits
Security Risk Advisors' Purple Team exercises are now recognized for CPE credits, enhancing cybersecurity professionals' skills and certification maintenance.

Oligo Launches Real-Time Exploit Detection and Blocking
Oligo Security has unveiled a new capability to block exploits at the application layer in real time. This innovation is crucial as attackers evolve their tactics, making traditional methods less effective. Oligo's solution allows organizations to protect their applications without disrupting operations.
OWASP SPVS - Enhancing Software Security Standards Explained
The OWASP Secure Pipeline Verification Standard enhances software security by addressing vulnerabilities in the software supply chain. This initiative is crucial for developers and organizations aiming to protect their software from evolving threats. Get involved and help shape the future of secure software practices.
Psychology of Information Security - A Comprehensive Review
Leron Zinatullin's book reveals how human behavior shapes security controls. It’s essential reading for security professionals focused on compliance and policy design. Understanding these dynamics can significantly reduce risks in organizations.

Pentesting - Essential Advice from BHIS Pentest Lead
A pentest lead from BHIS shares insights on starting a pentesting career. Discover essential skills, training paths, and the importance of hands-on experience. This advice is crucial for anyone looking to break into offensive security.
AI-Powered Log Summary - Enhancing SOC Team Efficiency
Rapid7 has launched an AI-powered log summary tool designed to help SOC teams analyze security alerts more efficiently. This innovation reduces investigation time and enhances response accuracy, allowing teams to focus on critical tasks.

SPF Flattening - Essential Guide for Office 365 and Google Workspace
SPF flattening simplifies email authentication for Office 365 and Google Workspace users. It reduces DNS lookups, enhancing email deliverability. Learn how to implement this essential practice.

Federated Identity Management - Enhancing Security and Usability
Federated Identity Management enhances security and user experience by allowing a single login for multiple services. This approach simplifies authentication while maintaining security. Discover how it works and its benefits!

Capability-Centric Governance - Redefining Access Control
A new governance model for legacy systems enhances access control by focusing on capabilities rather than permissions. This shift improves security and accountability, addressing legacy system risks effectively.

Little Snitch for Linux - New Tool Monitors App Connections
Little Snitch for Linux has launched, providing users with visibility into app connections. This free tool enhances desktop privacy for Linux users. It's open source and uses eBPF for effective monitoring.
Mallory Launches AI-Native Threat Intelligence Platform, Now with Enhanced Contextual Insights
Mallory has launched an AI-native threat intelligence platform that enhances the ability of security teams to contextualize threats and prioritize vulnerabilities, addressing the challenges posed by AI-enabled attackers.

Linux Security Operations - Rethinking for Better Outcomes
Linux security operations are becoming more efficient by integrating tools and leveraging AI. This shift helps teams improve their security posture and streamline processes. A unified approach is essential for effective management.

Penetration Testing - Safely Assessing OT Networks
Penetration testing OT networks is possible without disruption. This structured approach helps identify vulnerabilities while keeping systems safe. Don't leave security gaps open for attackers.

C and C++ Security Checklist - New Testing Handbook Chapter
A new chapter in the Testing Handbook introduces a security checklist for C and C++ code. It covers common bugs and platform-specific issues, enhancing manual review processes. Developers can also test their skills with challenges for a chance to win prizes.

Visibility - Enhancing Security Through Better Decisions
Visibility in security is more than compliance; it shapes user behavior and improves decision-making. Learn how better visibility can enhance your organization's security posture.

Advenica Launches File Scanner Kiosk for USB Malware Detection
Advenica has launched the File Scanner Kiosk, a system that scans USB media for malware. This tool is crucial for businesses that rely on USB drives for file transfers, helping to reduce the risk of malware infections. With its advanced scanning capabilities, it ensures clean file transfers and operational continuity.

Post-Incident Review - Essential Steps for Improvement
Learn how to conduct effective Post-Incident Reviews to strengthen your cybersecurity practices. Discover essential steps to analyze incidents and improve future responses.
NETSCOUT Arbor DDoS Protection Earns G2 Leader Badges
NETSCOUT's Arbor Threat Mitigation System has earned five G2 Leader badges for DDoS protection, showcasing its reliability. This recognition highlights its effectiveness in safeguarding networks against attacks.

GPU Password Cracking - Specops Analyzes Performance Limits
Specops reveals that a $30,000 GPU isn't superior for password cracking. In fact, consumer GPUs outperform them, highlighting the need for strong password policies.

Secrets Detection - Integrating It into Your Security Workflow
Secrets detection is essential for modern security workflows. It helps identify leaked credentials across various platforms. Organizations must implement automated validation to enhance their defenses.

Secureframe - Launches User Access Reviews for Governance
Secureframe has launched User Access Reviews, automating access validation for organizations. This new feature enhances security governance and streamlines compliance efforts, reducing manual workload. It's a game-changer for audit readiness and accountability.

Automated Pentesting - Why It's Not Enough for Security
Join today's webinar to learn why automated pentesting tools may not be enough for comprehensive security validation and how to address hidden vulnerabilities.

Acronis MDR Launch - 24/7 Managed Detection for MSPs
Acronis has launched Acronis MDR, a 24/7 managed detection and response service tailored for MSPs, enhancing security capabilities while reducing operational costs.

Detection Engineering - Correlation Techniques Explained
The latest installment in the detection foundation series focuses on correlation techniques in security. Learn how to connect Windows logs and Sysmon data for better incident response. This is crucial for identifying suspicious activities and enhancing your security posture.
PortSwigger - Partners with Meta for Bug Bounty Training
PortSwigger and Meta have teamed up to enhance bug bounty training, empowering researchers with tools and education for better vulnerability detection.

Microsoft Defender - New Update Enhances Malware Protection
Microsoft has released a vital update for Defender Antivirus, enhancing malware detection for Windows 11, 10, and Server. This update is crucial for user security.
Microsoft Removes Support and Recovery Assistant from Windows
Microsoft has deprecated the Support and Recovery Assistant tool. IT admins must now switch to the Get Help tool for troubleshooting Windows issues. This change enhances security across Microsoft products.

METATRON - New AI Tool Enhances Penetration Testing on Linux
A new open-source tool called METATRON is revolutionizing penetration testing. Designed for Linux, it uses AI to assess vulnerabilities offline. This ensures sensitive data remains secure, making it ideal for professionals.
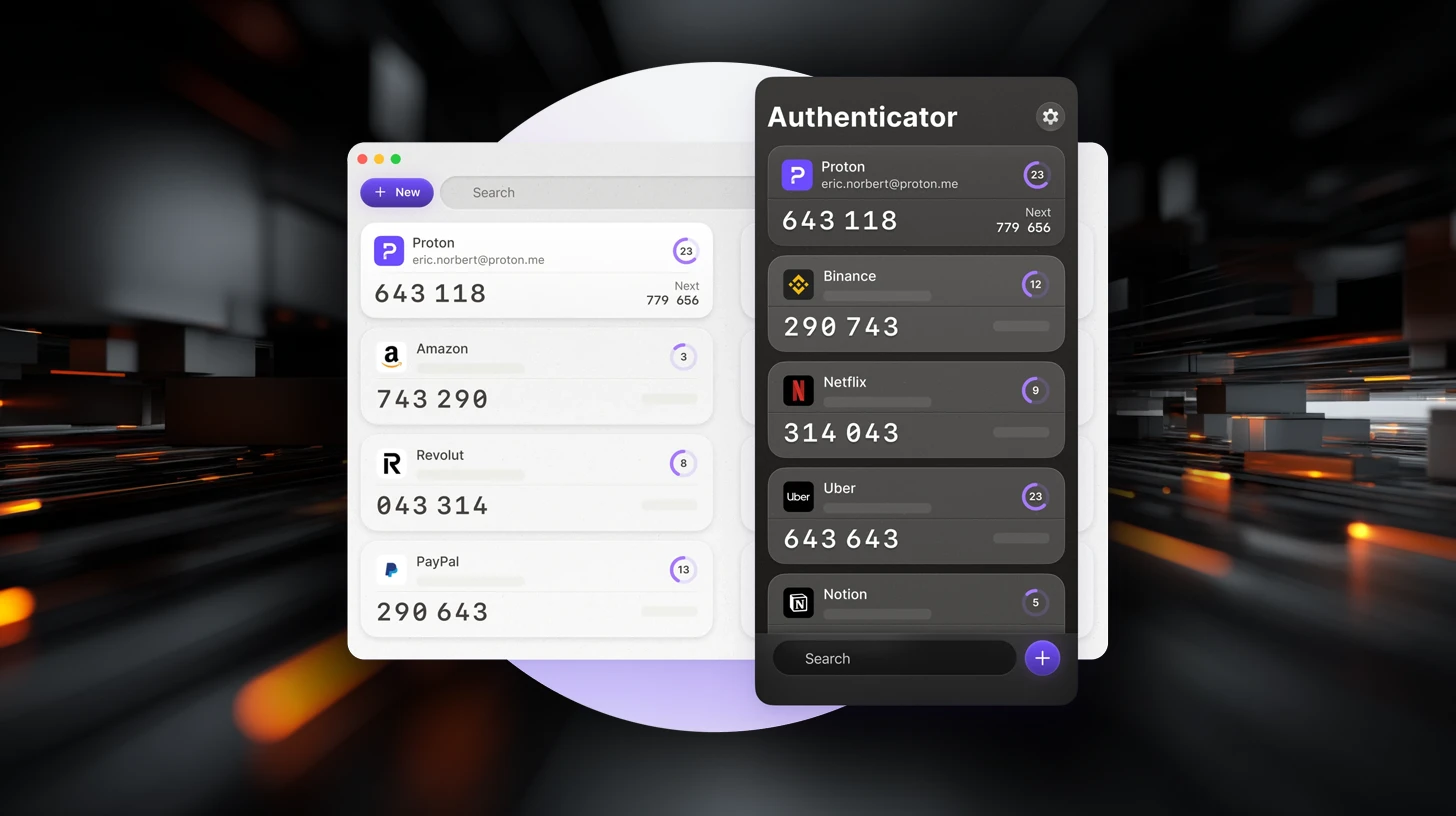
Proton Authenticator - End-to-End Encrypted 2FA App Explained
Proton Authenticator is a new open-source 2FA app that enhances online security. It generates time-based passwords and offers encrypted backups for user data. This app ensures privacy without ads or tracking, making it a reliable choice for securing accounts.
.webp)
Best User Access Management Tools - Top Picks for 2026
Explore the best user access management tools for 2026! These tools enhance security and streamline user permissions, helping organizations protect sensitive data and ensure compliance.

Elastic Security - Nine New Integrations Announced
Elastic Security Labs just launched nine new integrations! These tools boost cloud security, endpoint visibility, and email threat detection, helping teams respond to threats faster.

6 Critical Mistakes Undermining Cyber Resilience Explained
Organizations often make critical mistakes that weaken their cyber resilience. This article outlines six key errors and how to fix them for better security. Don't let silos hold you back.

CoBRA - Simplifying Mixed Boolean-Arithmetic Obfuscation
CoBRA simplifies Mixed Boolean-Arithmetic obfuscation, helping security engineers analyze malware and software protection schemes. It boasts a 99.86% success rate, making it a powerful tool in the cybersecurity toolkit. Available as a CLI tool, C++ library, and LLVM pass plugin.