China-Linked Groups Target Southeast Asian Government with Malware
Basically, hackers from China used advanced malware to attack a Southeast Asian government.
In 2025, China-linked groups executed a sophisticated malware attack on a Southeast Asian government. This campaign used multiple malware families, posing serious risks to national security. The advanced tactics employed highlight the growing threat of cyber espionage. Organizations must strengthen defenses against such well-coordinated efforts.
What Happened
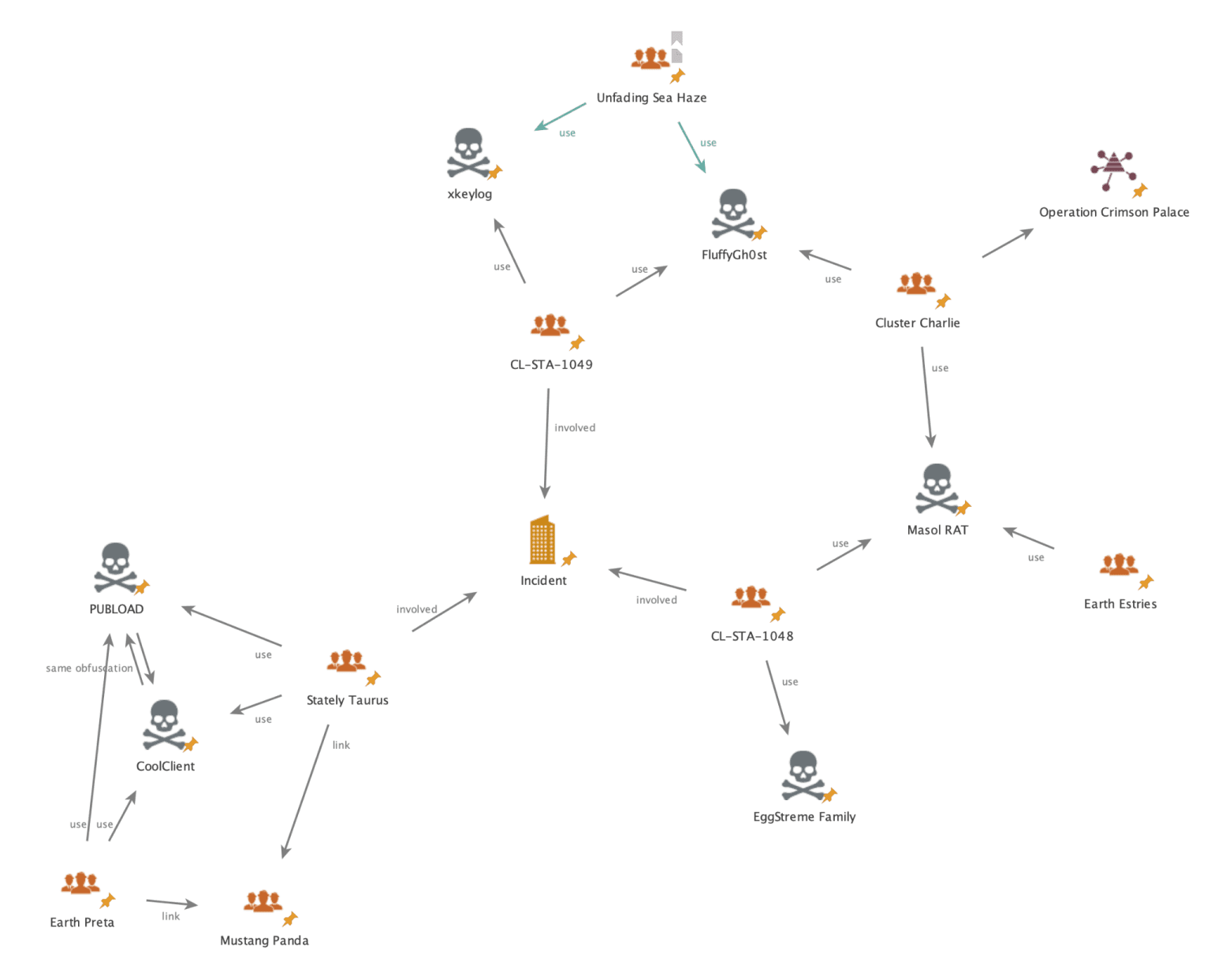
In 2025, three China-linked threat clusters launched a sophisticated cyber operation targeting a Southeast Asian government. This well-funded campaign involved deploying multiple malware families, including PUBLOAD, FluffyGh0st, and MASOL RAT. Researchers from Palo Alto Networks reported that these groups demonstrated advanced tactics and maintained persistent access to sensitive systems.
The cyber activity was linked to clusters known as Mustang Panda, CL-STA-1048, and CL-STA-1049. Each cluster utilized different malware types and strategies, showing a coordinated effort to infiltrate and exfiltrate data from the targeted government entity. The attackers aimed for long-term access rather than immediate disruption, indicating a focus on espionage.
Who's Being Targeted
The primary target of this cyber campaign was a Southeast Asian government, specifically its critical infrastructure and sensitive information systems. The attackers employed a variety of malware to gain footholds within the government’s networks. This operation is notable for its complexity and the resources behind it, suggesting significant backing from state-level actors.
The clusters involved in this attack have been linked to previously reported campaigns, indicating a pattern of behavior among China-aligned groups. The overlapping tactics and techniques used by these clusters suggest a concerted effort to achieve common objectives, potentially coordinated to maximize impact.
Signs of Infection
Indicators of compromise include the deployment of PUBLOAD through infected USB drives, which facilitated lateral movement within the network. The malware was designed to collect and exfiltrate critical system information, such as usernames and computer details, over obfuscated channels. Additionally, the use of CoolClient loaders showcased advanced anti-analysis techniques, further complicating detection efforts.
Other malware, such as EggStremeFuel and MASOL RAT, provided backdoor access and keylogging capabilities, allowing attackers to gather sensitive data and maintain control over compromised systems. The stealthy nature of the Hypnosis DLL loader used to deploy FluffyGh0st RAT further exemplifies the sophisticated techniques employed by these threat actors.
How to Protect Yourself
To mitigate the risks posed by such advanced malware campaigns, organizations should enhance their cybersecurity measures. This includes implementing robust endpoint protection solutions that can detect and respond to suspicious activities. Regularly updating software and conducting security audits can help identify vulnerabilities before they are exploited.
Additionally, training staff to recognize phishing attempts and suspicious USB devices is crucial. Organizations should also consider adopting a zero-trust security model, ensuring that access to sensitive systems is tightly controlled and monitored. By staying vigilant and proactive, organizations can better defend against the evolving threat landscape presented by sophisticated malware attacks.