🎯Basically, attackers are using sneaky methods to break into virtual machines and steal data from servers.
What Happened
A new wave of attacks is making headlines as security researchers from Huntress reveal a sophisticated method to exploit ESXi hypervisors. This multi-step attack is designed to escape from guest virtual machines (VMs) and target the underlying hypervisor. The attackers are leveraging potential zero-day vulnerabilities, which means they are exploiting weaknesses that haven't yet been publicly disclosed or patched.
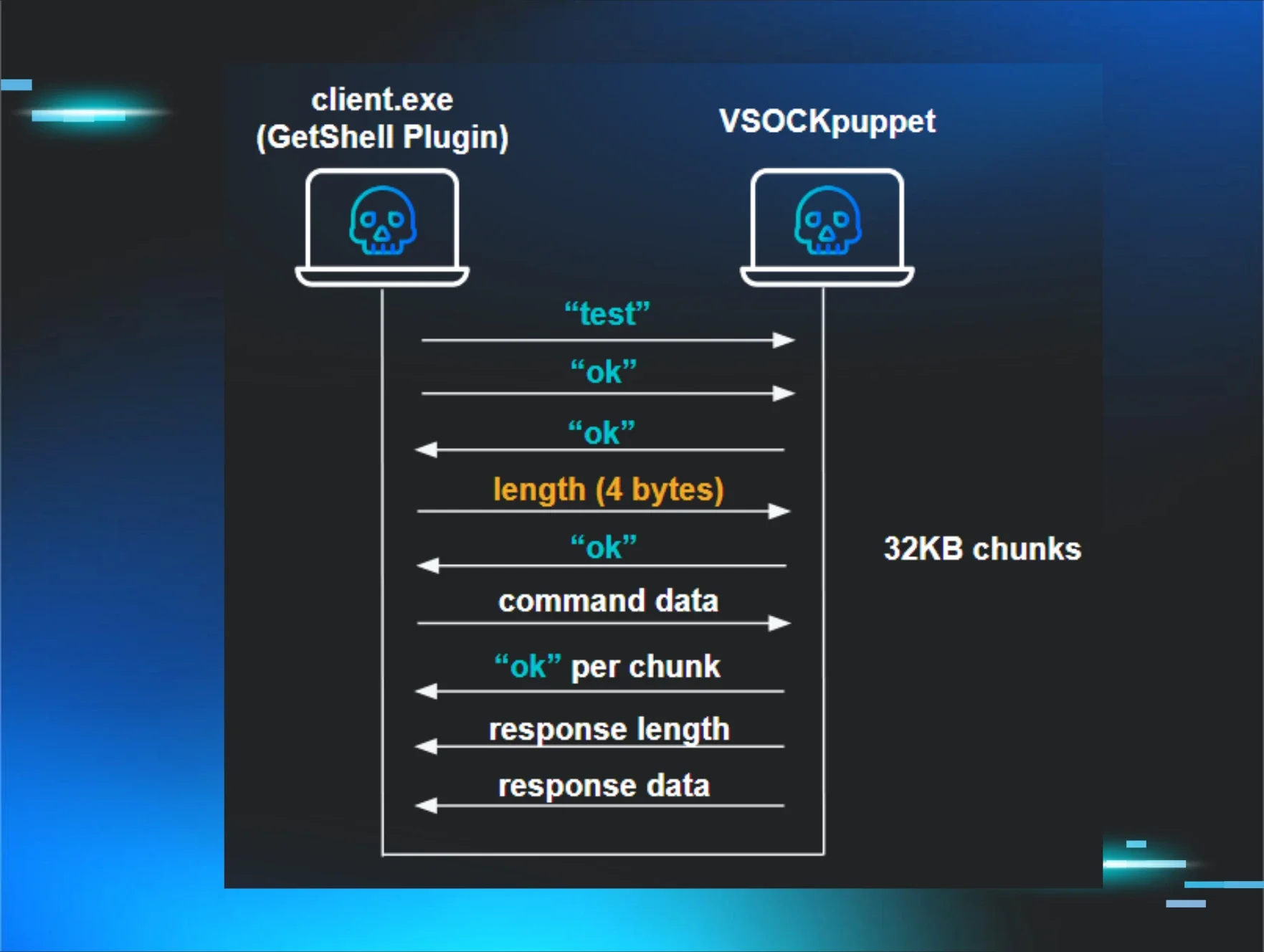
The technique involves using VSOCK communication, a method that allows communication between virtual machines and the host system. This sneaky approach enables attackers to bypass traditional security measures, making it harder for defenses to detect their activities. As the complexity of these attacks increases, the urgency for organizations to safeguard their virtual environments becomes paramount.
Why Should You Care
If you use virtual machines in your business or personal projects, this news directly affects you. Think of your VMs like apartments in a high-rise building. If an intruder can break into one apartment, they might find a way to access the entire building. This could lead to significant data breaches, exposing sensitive information stored on your servers.
Moreover, many companies rely on ESXi hypervisors to manage their virtual environments. If attackers successfully exploit these vulnerabilities, they could steal data, disrupt services, or even hold systems hostage. Protecting your virtual infrastructure is not just a technical requirement; it's essential for maintaining trust with your customers and clients.
What's Being Done
Security experts are on high alert, and organizations are urged to take immediate action. Here are some steps you can take to protect your systems:
- Update your ESXi hypervisors to the latest version to patch any known vulnerabilities.
- Monitor your network for unusual VSOCK communications that could indicate an ongoing attack.
- Implement strict access controls to limit who can interact with your hypervisors.
Experts are closely monitoring the situation for any new developments, especially if more vulnerabilities are discovered or if attackers refine their methods. Staying informed and proactive is your best defense against these evolving threats.
🔒 Pro insight: The sophistication of these attacks highlights the need for enhanced monitoring and defense strategies in virtual environments.





