🎯Basically, mutational grammar fuzzing can miss bugs even with lots of coverage.
What Happened
Fuzzing is a powerful technique used to find bugs in software, but it has its pitfalls. Mutational grammar fuzzing, a method that generates samples based on predefined grammar rules, can sometimes lead to misleading results. While it aims to maintain the structure of samples during mutation, it doesn't always find the bugs you might expect, especially in complex scenarios.
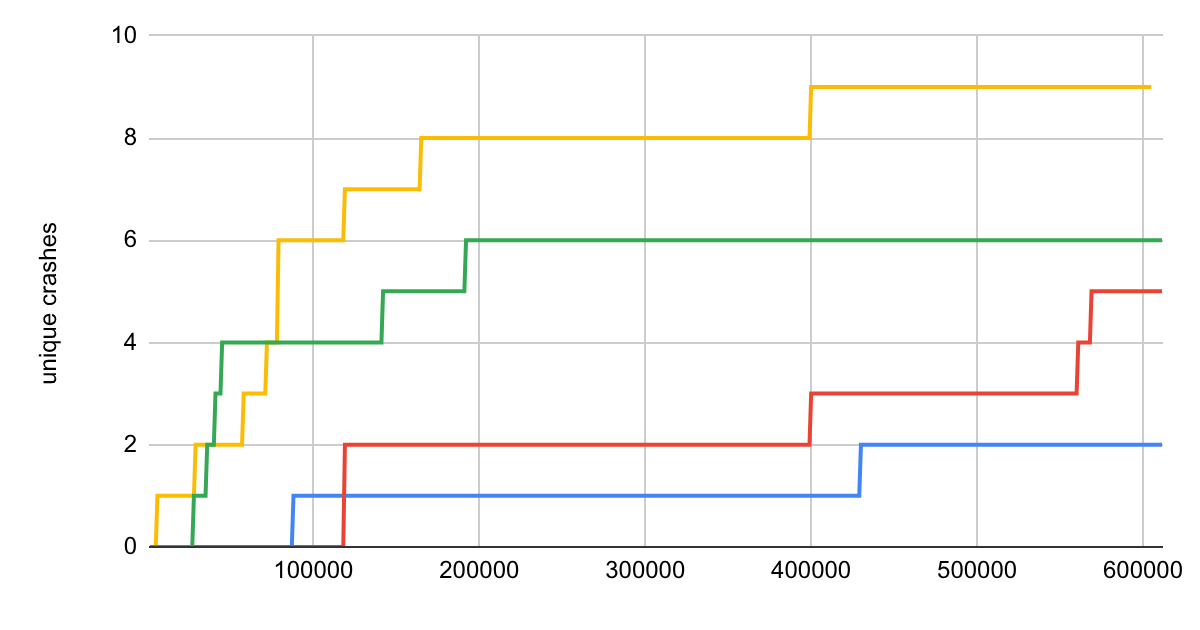
A recent blog post highlights a significant flaw in this approach: more code coverage does not necessarily equate to finding more bugs. For example, in language fuzzing, certain bugs require specific sequences of function calls. If a fuzzer generates samples that cover the same lines of code but do not interact correctly, it may miss critical bugs. This is particularly evident in cases like the libxslt library, where the order of function calls is essential for triggering specific issues.
Why Should You Care
You might wonder why this matters to you. If you're a developer or a security professional, understanding these flaws can save you time and resources. Imagine using a tool that claims to find bugs but overlooks critical issues because it focuses too much on coverage instead of the actual interactions between functions. This could lead to undetected vulnerabilities in your software, putting your users at risk.
The key takeaway is that simply increasing coverage in fuzzing does not guarantee better bug detection. Just like a security guard who checks every corner of a building but ignores the doors, a fuzzer needs to ensure that the right combinations of inputs are tested.
What's Being Done
The author of the blog post is not just pointing out flaws; they also offer solutions. They suggest improving fuzzing runs by combining samples in a way that reflects the necessary interactions between functions. Here are some immediate actions you can take:
- Review your fuzzing strategy to ensure it accounts for function interactions.
- Experiment with combining samples to better reflect the dependencies between functions.
- Stay updated on new techniques and improvements in fuzzing methodologies.
Experts are watching for how these insights will influence future fuzzing tools and techniques. The goal is to refine the process and ensure that fuzzing remains a reliable method for detecting complex bugs.
🔒 Pro insight: This highlights the need for fuzzers to focus on interaction patterns rather than just coverage metrics to effectively identify complex bugs.





