HTTP Smuggling: Spotting Real Threats vs. False Positives
Basically, some web traffic looks suspicious but isn’t harmful, confusing many people.
Confusion between HTTP request smuggling and harmless traffic is common. This misidentification can lead to wasted resources and missed threats. Experts are refining detection methods to improve accuracy and reduce false alarms.
What Happened
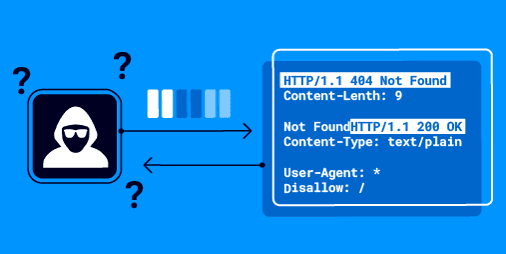
In the world of web security, distinguishing between HTTP request smuggling and harmless behaviors like HTTP keep-alive? or pipelining is crucial. Many security professionals mistakenly identify normal traffic as a potential threat. This confusion can lead to unnecessary alarm and misallocation of resources.
HTTP request smuggling? occurs when an attacker manipulates the way web servers interpret requests, potentially allowing them to bypass security measures. However, not every odd-looking request is a sign of trouble. False positives can arise from legitimate features of HTTP, such as keep-alive connections, which allow multiple requests to be sent over a single connection, or pipelining, where multiple requests are sent without waiting for the previous one to finish.
Understanding the difference is essential for effective security practices. Misidentifying a harmless request as a threat can waste time and lead to a lack of focus on real vulnerabilities.
Why Should You Care
You might wonder why this matters to you personally. Imagine your bank's website mistakenly flagging your login attempt as suspicious. This could lock you out of your account, causing frustration and delays. In a business context, misidentifying legitimate traffic can lead to wasted resources and missed opportunities to address actual threats.
When security teams are overwhelmed by false alarms, they may overlook genuine risks. Your online safety relies on accurate threat detection. If security systems are constantly crying wolf, they may miss the real dangers lurking in your web traffic.
What's Being Done
Security experts are working to refine detection methods to better differentiate between legitimate traffic and potential threats. Here are some steps being taken:
- Improved algorithms: Developers are enhancing algorithms to reduce false positives?.
- Training and awareness: Security teams are being educated on the nuances of HTTP behaviors to make more informed decisions.
- Monitoring tools: New tools are being developed to assist in real-time analysis of web traffic.
Experts are closely watching how these advancements evolve. They aim to strike a balance between vigilance and accuracy, ensuring that security measures protect users without causing unnecessary alarm.
PortSwigger Research