Internet-Exposed ICS Devices Raise Security Risks
Significant risk — action recommended within 24-48 hours
Basically, some important machines connected to the internet are not safe and could be attacked.
Exposed ICS devices using insecure protocols like Modbus raise serious security concerns. Critical sectors may face disruptions and sabotage. Urgent action is needed to secure these systems.
What Happened
Recent research has revealed alarming vulnerabilities in Industrial Control Systems (ICS) due to their exposure to the internet. Devices using insecure protocols like Modbus are particularly at risk, allowing potential attackers to disrupt operations and gain unauthorized access to critical data. Notable malware attacks, such as Stuxnet and Industroyer, have already demonstrated the severe consequences of exploiting these vulnerabilities.
Who's Affected
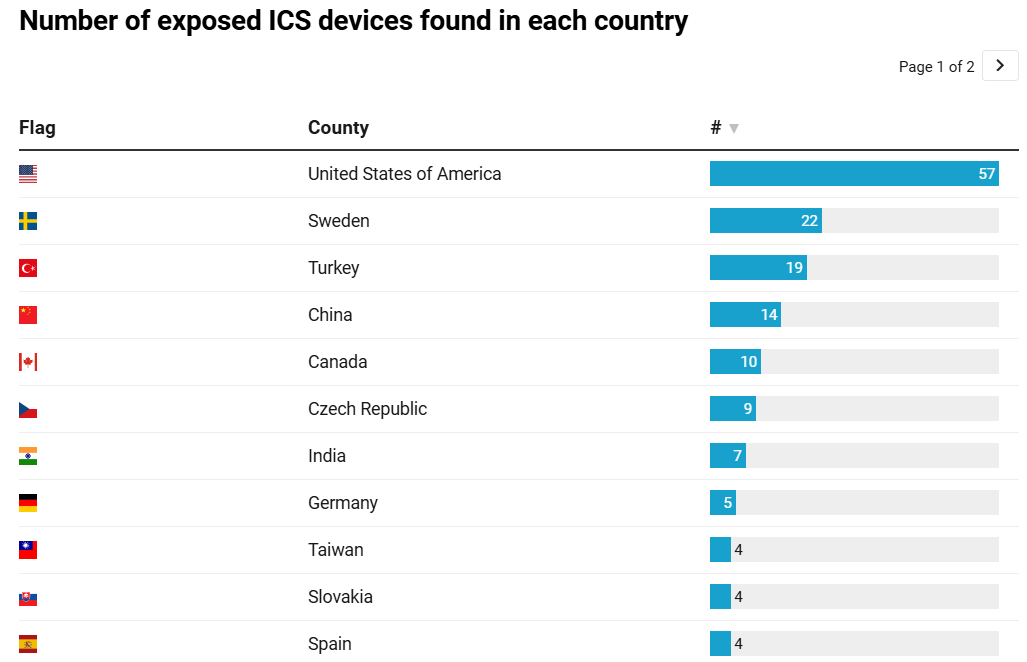
The exposure of ICS devices affects various sectors, including energy, manufacturing, and utilities. These sectors rely heavily on ICS for monitoring and controlling essential operations. The United States, Sweden, and Turkey have been identified as hosting significant numbers of these vulnerable devices, which are often linked to sensitive environments like national power grids and railway systems.
What Data Was Exposed
The research indicated that many ICS devices exposed their firmware versions and internal IDs, which can be exploited by attackers to locate documentation that defines how data is stored and interpreted. This could include critical operational data such as temperature and pressure readings. The ability to alter register values without authentication poses a significant risk, as even minor changes can disrupt industrial processes.
What You Should Do
To mitigate these risks, organizations should implement basic security measures such as:
- Firewalls to block unauthorized access.
- VPNs for secure remote connections.
- Network segmentation to isolate critical systems.
- Strong authentication methods to prevent unauthorized modifications.
However, many ICS environments still operate on outdated architectures, originally designed for isolated networks rather than today’s interconnected landscape. As the global ICS market continues to grow, the urgency to secure these systems against cyber threats becomes increasingly critical.
Conclusion
The growing exposure of ICS devices, combined with insecure legacy protocols and increasing interest from threat actors, creates a high-risk environment. Without significant improvements in security practices, these systems remain prime targets for cyber threats, potentially leading to severe operational disruptions and safety hazards.
🔍 How to Check If You're Affected
- 1.Conduct a scan for devices using Modbus on port 502.
- 2.Verify the firmware versions of ICS devices for known vulnerabilities.
- 3.Implement network segmentation to isolate ICS from external access.
🔒 Pro insight: The rapid increase in ICS vulnerabilities highlights a critical need for enhanced security measures in industrial environments.