🎯Basically, manufacturing security can't use regular IT methods because machines are different and older.
What Happened
In a recent interview, Ejona Preçi, Group CISO at Lindal Group, highlighted a pressing issue in cybersecurity: the failure of traditional IT security practices in manufacturing environments. While IT security focuses on protecting data and networks, the unique challenges of Operational Technology (OT) require a different approach, especially on the shop floor where machines and systems operate.
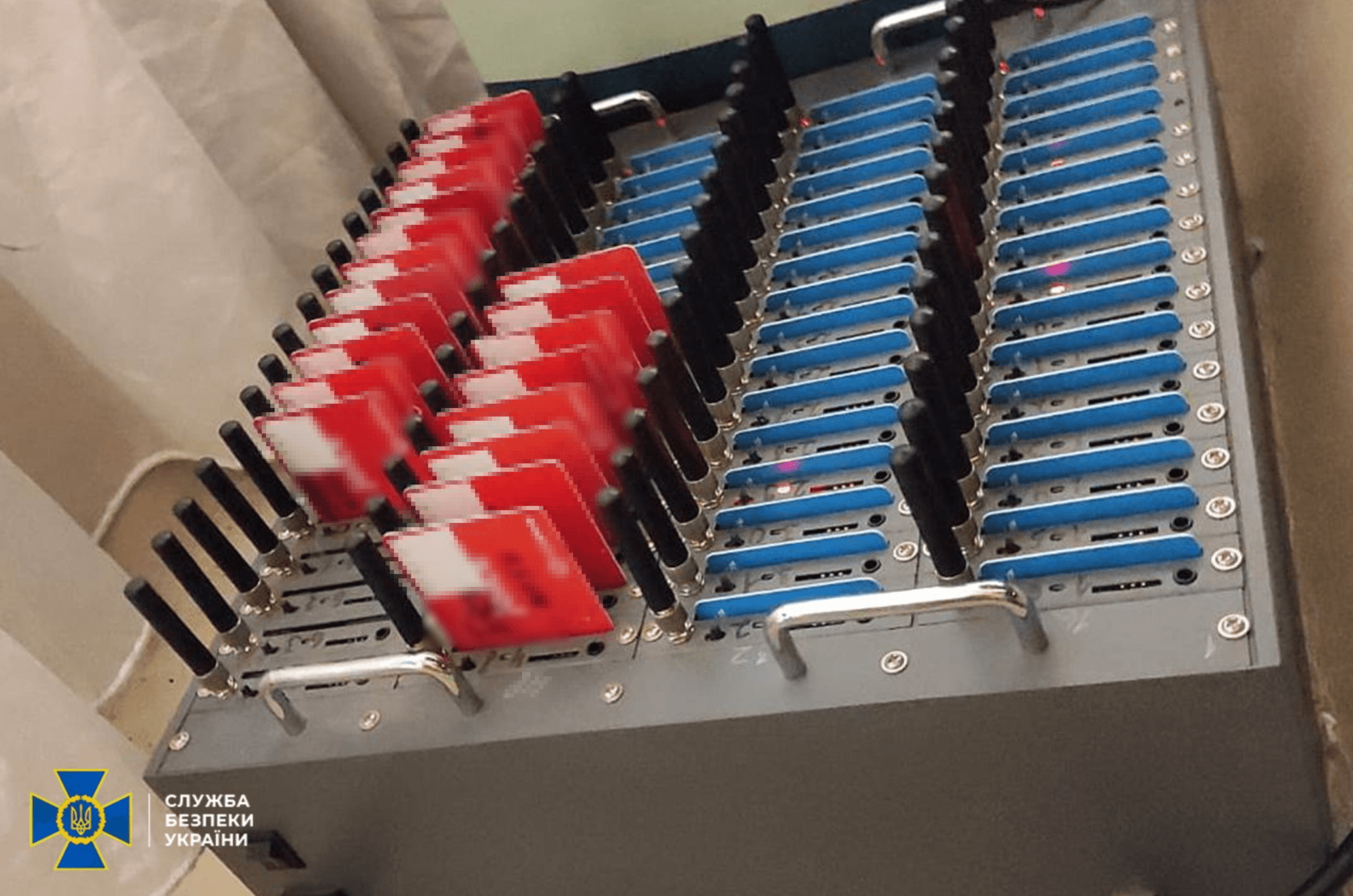
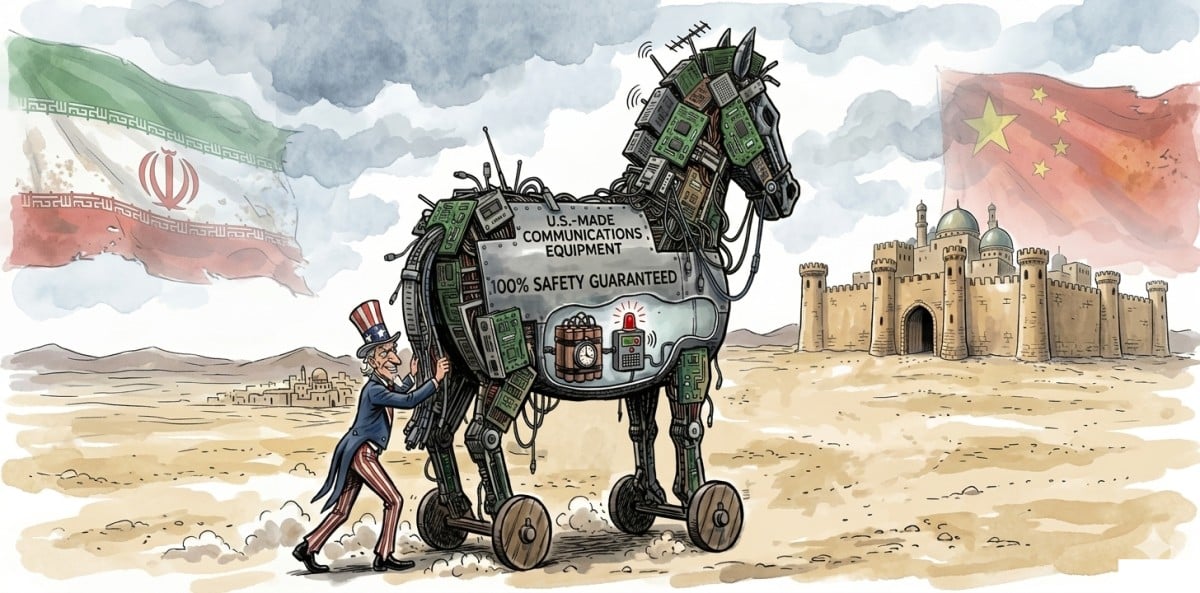
Preçi pointed out that many Programmable Logic Controllers (PLCs) and other industrial devices are often running on outdated firmware that was never designed for network connectivity. This creates vulnerabilities that can be exploited by cybercriminals and nation-state actors alike. These attackers can infiltrate industrial networks using stale accounts and compromised workstations, all while remaining undetected.
The conversation sheds light on the critical need for tailored security strategies that address the specific risks associated with OT environments, rather than applying generic IT solutions that may not be effective or even harmful.
Why Should You Care
If you work in manufacturing or any industry that relies on machinery, this issue directly impacts you. Imagine your factory's machines suddenly shutting down due to a cyberattack. It could halt production, leading to significant financial losses and safety risks. Understanding the difference between IT and OT security is crucial for protecting your workplace.
Think of it like a traditional office building versus a factory. In an office, you might focus on protecting computers and data, but in a factory, you need to ensure the machines that keep everything running are secure. This distinction is vital for preventing disruptions and maintaining safety in your operations.
What's Being Done
As awareness grows, industry leaders like Preçi are advocating for a shift in how organizations approach OT security. Here are some key actions being recommended:
- Develop specialized security protocols tailored for OT environments.
- Invest in training for staff to recognize and respond to unique threats.
- Regularly assess and update your security measures to adapt to evolving threats.
Experts are closely monitoring how organizations adapt to these challenges and whether they implement the necessary changes to protect their industrial environments effectively. The conversation emphasizes that without a dedicated focus on OT security, the risks will only continue to grow.
🔒 Pro insight: The divergence between IT and OT security practices highlights a critical gap that attackers are exploiting, necessitating immediate strategic realignment.