🎯Imagine if someone could unlock your secret diary using a super advanced key. That's what quantum computers could do to today's encryption. We need to upgrade our locks (encryption methods) before they get that key!
What Happened
Imagine a world where your encrypted messages, bank details, and private files could be easily read by anyone. This isn't just a sci-fi scenario; it's a looming reality. Many attackers are already preparing for a future where today's encryption methods can be broken by quantum computers. Instead of decrypting data immediately, they are adopting a strategy called 'harvest now, decrypt later.' This means they collect and store encrypted information today, waiting for the technology to crack it in the future.
This tactic poses a significant risk to organizations and individuals alike. As quantum computing technology advances, the encryption that protects our sensitive data could become obsolete. This isn't just theoretical; experts warn that the potential for exploitation is real and imminent. The race is on to develop new cryptographic methods that can withstand these powerful quantum attacks.
Why Should You Care
You might think your data is safe because it’s encrypted, but that's not enough anymore. Imagine locking your front door, only to find out that a new type of key can open it effortlessly. If attackers can decrypt your data in the future, your personal and financial information could be at risk. This isn't just a concern for tech companies; it affects everyone who uses the internet for banking, shopping, or communication.
As quantum computers become more powerful, the urgency to transition to post-quantum cryptography grows. Think of it like upgrading your home security system to protect against new types of break-ins. You wouldn’t wait until after a burglary to reinforce your defenses, would you? The same logic applies to your digital security.
What's Being Done
Organizations are starting to take action, but the clock is ticking. Security leaders are urged to participate in webinars and training sessions focused on post-quantum cryptography. Experts are working on developing new encryption standards that can withstand quantum attacks. Here’s what you can do right now:
- Stay informed about the latest developments in post-quantum cryptography.
- Evaluate your current encryption methods and consider transitioning to quantum-resistant solutions.
- Engage with cybersecurity professionals to understand how to protect your data effectively.
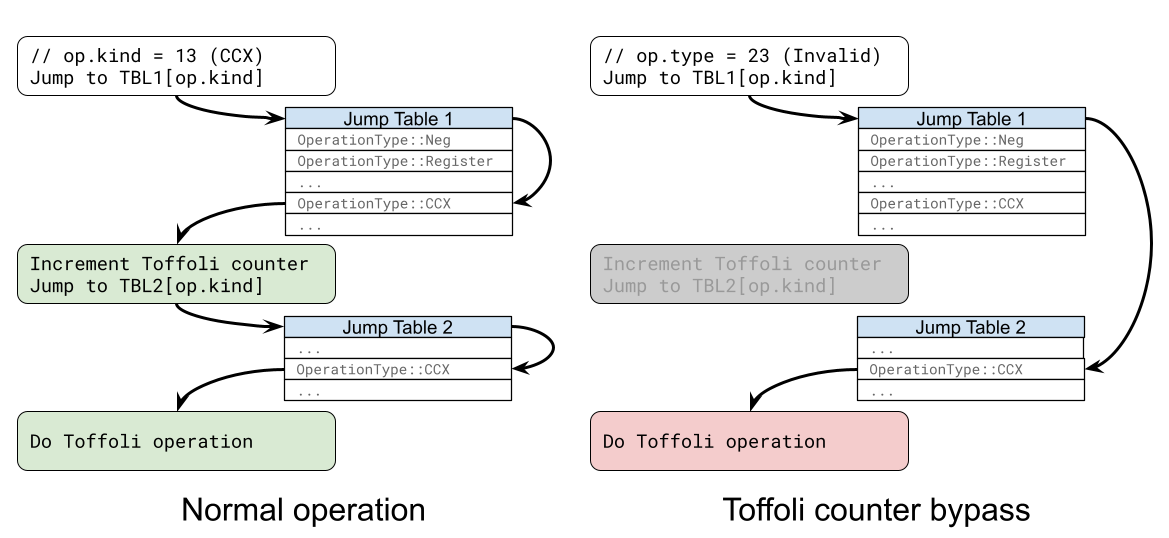
Google has recently moved up its estimated deadline for quantum preparedness in cryptography to 2029, just 33 months away. This shift comes after significant advancements in quantum technology, emphasizing the urgent need for organizations to update their systems. Experts warn that if systems are not updated in time, attackers with powerful quantum computers could exploit vulnerabilities to impersonate users and gain unauthorized access to sensitive information.
Additionally, the National Institute of Standards and Technology (NIST) has been actively working on standardizing post-quantum cryptographic algorithms, with the first round of selected candidates expected to be finalized by late 2024. This initiative aims to provide a framework for organizations to adopt quantum-resistant encryption methods, ensuring a smoother transition as quantum capabilities evolve.
Fortunately, not all cryptography is vulnerable to quantum attacks. Symmetric encryption, for instance, remains largely quantum-resistant, provided that key lengths are sufficiently robust. However, the challenge lies in key distribution and authentication processes, which must also be fortified against potential quantum threats.
As the transition to post-quantum cryptography progresses, it's crucial to remain vigilant. Current estimates suggest that about 40% of websites already support post-quantum key exchange, but many systems still need significant updates. Users are encouraged to apply software updates promptly and to verify whether their encrypted messaging platforms have implemented quantum-resistant protocols. As we approach the 2029 deadline, the importance of proactive measures cannot be overstated. The future of your data security depends on it.
The rapid advancements in quantum computing technology necessitate immediate action from organizations to adopt post-quantum cryptographic solutions. The NIST's upcoming standards will play a crucial role in guiding this transition.