🎯Imagine if a thief broke into your house and turned off your security alarm. That's what happened with SonicWall, where hackers used stolen VPN details to disable security tools. This shows that even the best defenses can be broken, and we need to be extra careful.
What Happened
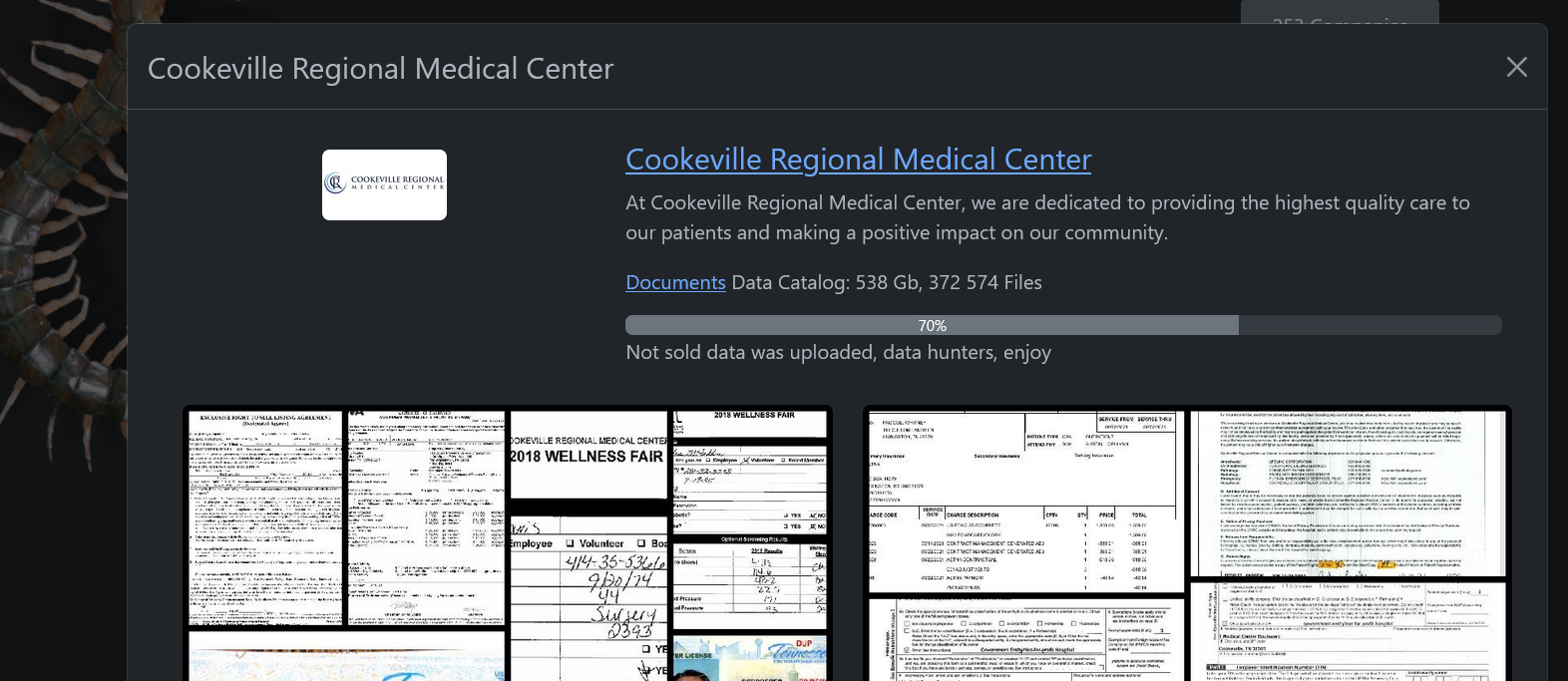
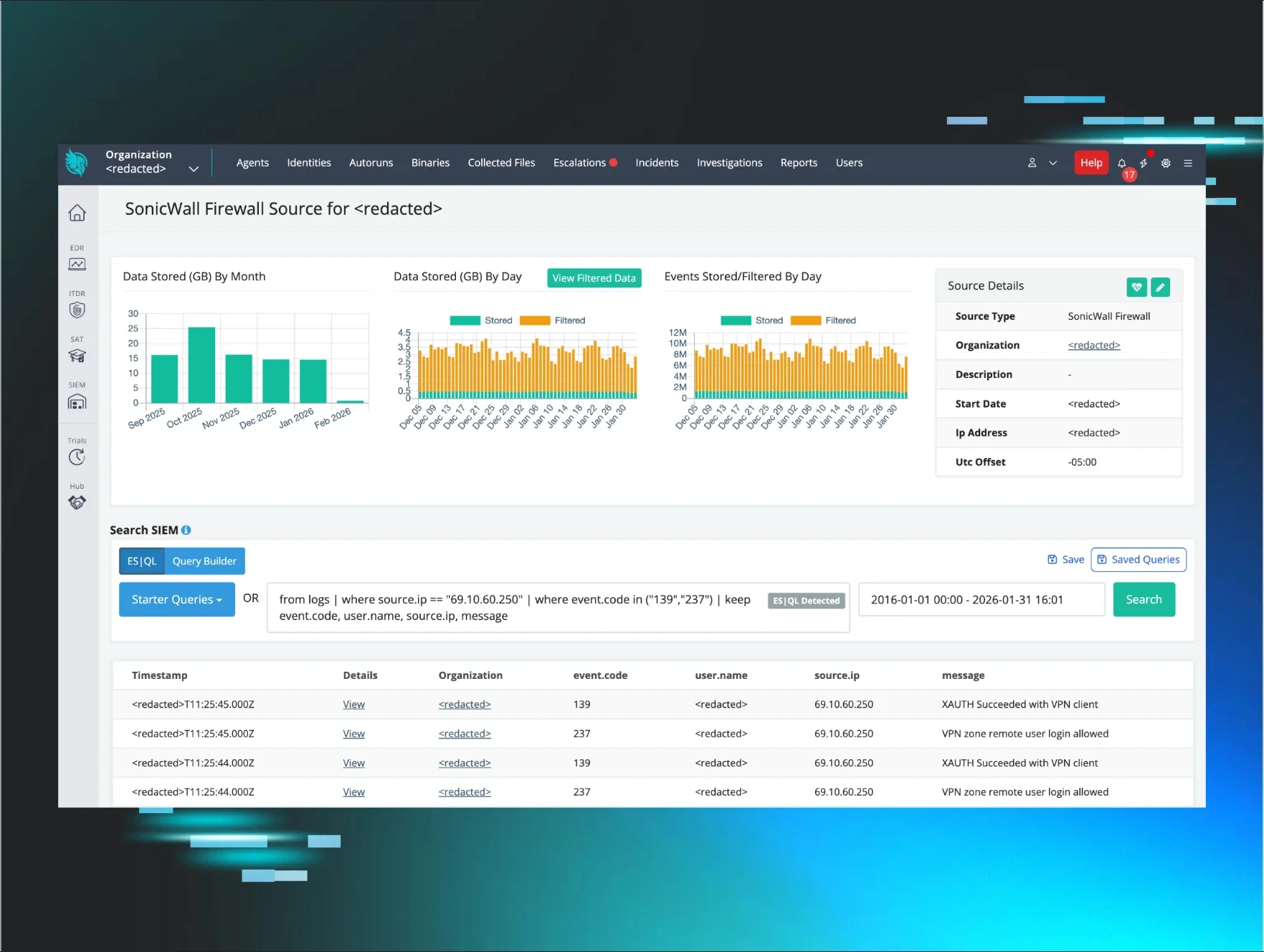
Imagine waking up to find that your home security system has been disabled by an intruder. This is exactly what happened in a recent cyber incident involving SonicWall VPN credentials. Attackers exploited these credentials to gain unauthorized access to systems, allowing them to execute a malicious plan.
Once inside, the hackers employed a technique known as BYOVD (Bring Your Own Vulnerable Driver). They used a revoked EnCase forensic driver to terminate critical security processes. This tactic is alarming because it directly undermines the very tools designed to protect against such intrusions. The implications of this breach are significant, as it highlights vulnerabilities in security protocols that many organizations rely on.
New Developments
Recent reports indicate that the breach may be part of a larger trend where attackers are increasingly targeting security tools themselves. This tactic not only compromises individual organizations but also poses a systemic risk to cybersecurity infrastructure as a whole. Experts warn that such direct attacks on security tools could lead to more widespread vulnerabilities across the industry.
Additionally, the attackers may have utilized sophisticated methods to escalate privileges within affected systems, potentially allowing them to maintain persistence and evade detection. This underscores the need for organizations to implement robust monitoring and response strategies.
Why Should You Care
You might think that security tools are foolproof, but this incident shows that even the best defenses can be compromised. If you use SonicWall or similar VPN solutions, your organization could be at risk. Imagine if a burglar not only broke into your house but also disabled your alarm system — that’s what these hackers did to security software.
Your data and privacy are at stake. If attackers can disable your security tools, they can freely access sensitive information, potentially leading to data breaches or financial losses. This incident serves as a wake-up call for everyone, from individuals to large corporations, about the importance of safeguarding access credentials and continuously monitoring security systems.
What's Being Done
In response to this alarming breach, cybersecurity firms like Huntress are actively investigating the incident. They are working to identify affected systems and implement necessary patches. Here are some immediate actions you should consider:
- Change your SonicWall VPN credentials immediately.
- Review your security tools for any signs of tampering or unauthorized access.
- Stay informed about updates from cybersecurity experts on this incident. Experts are closely monitoring the situation to see if similar attacks emerge, emphasizing the need for vigilance in cybersecurity practices.
This breach underscores the importance of not only securing access credentials but also ensuring that security tools themselves are resilient against targeted attacks. Organizations must adopt a proactive approach to monitor and respond to potential threats.