TA446 - Russia-linked Group Targets iPhone Users with Phishing
Basically, a Russian hacker group is tricking iPhone users to steal their information using fake emails.
A new phishing wave from Russia-linked TA446 is targeting iPhone users using the DarkSword exploit kit. This development raises serious security concerns for many organizations and individuals. Stay alert to protect your data from these sophisticated attacks.
The Threat
APT group TA446, also known as SEABORGIUM, has ramped up its phishing efforts. Recently, they have begun using the DarkSword iOS exploit kit to target iPhone users. This marks a significant shift in their tactics, as they had not previously focused on Apple devices. The group's campaigns primarily target NATO countries and have expanded to include the Baltics, Nordics, and Eastern Europe, including Ukraine.
The attacks typically start with malicious emails that aim to compromise iPhones. This method highlights the growing threat posed by state-sponsored actors, especially as TA446 has been active since at least 2017. Their operations often involve persistent phishing and credential theft, leading to significant intrusions and data theft.
Who's Behind It
TA446 has a reputation for targeting specific sectors, including defense, intelligence consulting, and non-governmental organizations. They also focus on think tanks and higher education institutions, as well as individuals with expertise in Russian affairs. This targeted approach allows them to conduct reconnaissance on potential victims, gathering information on their social networks and influence spheres.
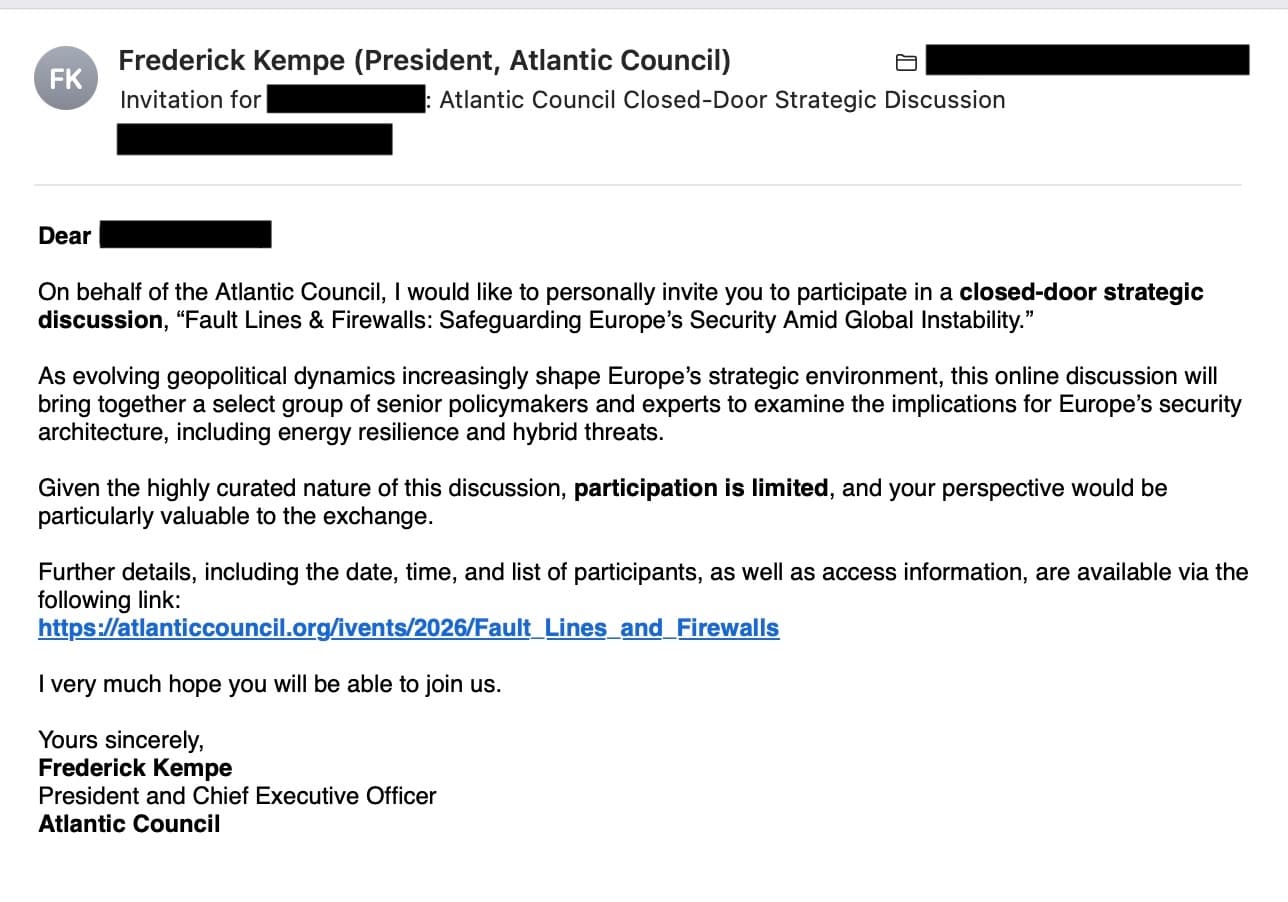
Proofpoint researchers have observed a notable increase in phishing emails attributed to TA446, particularly one campaign that spoofed the Atlantic Council. This surge in activity indicates a more aggressive stance from the group, as they attempt to exploit the vulnerabilities of iOS users through the newly adopted DarkSword exploit kit.
Tactics & Techniques
The phishing campaigns attributed to TA446 have shown a shift in their delivery methods. Previously, they relied on attachments, but recent attacks utilized links instead. This change is likely due to server-side filtering that redirects only iPhone users to the exploit kit. The emails often contain benign decoys, masking the true intent of credential harvesting and intelligence collection.
Researchers have confirmed that a TA446-controlled domain is delivering the DarkSword exploit kit, which includes components for remote code execution and bypassing security measures. While the researchers have not observed any sandbox escapes, the potential for exploitation remains high, especially with the broader target set observed in recent campaigns.
Defensive Measures
Given the evolving tactics of TA446, it is crucial for individuals and organizations to remain vigilant. Users should be cautious when receiving unsolicited emails, particularly those that appear to be from reputable organizations. Implementing multi-factor authentication (MFA) can add an extra layer of security against unauthorized access.
Organizations should also consider conducting regular security training for employees to recognize phishing attempts. Monitoring for unusual account activity can help detect potential breaches early, allowing for swift remediation. As TA446 continues to adapt its strategies, staying informed about these threats is essential for maintaining cybersecurity.