🎯Basically, attackers use clever tricks to break into computer systems, often by pretending to be someone else.
What Happened
Cybersecurity is evolving, and so are the techniques used by cybercriminals. Recent reports highlight that attackers are increasingly exploiting identity-related vulnerabilities. Traditional methods like malware deployment are being overshadowed by more subtle tactics that focus on human behavior and system trust.
The Threat
According to experts, identity-based attacks are on the rise. Phishing, stolen credentials, and social engineering are now the leading methods for initial breaches. For instance, phishing accounts for 41% of incidents, while stolen credentials make up 18%. Attackers are shifting their focus from software vulnerabilities to exploiting the human element in security.
Key Techniques Used by Attackers
-
Drive-By RMM Misuse: Attackers are abusing legitimate Remote Monitoring and Management (RMM) tools to camouflage their activities. Tools like ConnectWise ScreenConnect are being used for command-and-control operations, lateral movement, and deploying ransomware.
-
Network Security Device Hacking: Security devices, such as SSL VPN systems, have become prime targets. Recent data shows that SSL VPN compromises account for 33% of identifiable attack activity.
-
ClickFix: This social engineering tactic tricks users into executing malicious commands through fake prompts. It bypasses traditional security measures, making it a favored method for distributing malware.
-
Identity-Based Attacks: Attackers impersonate legitimate users or services to gain unauthorized access. This technique is gaining traction due to enhanced security measures that protect against direct software exploitation.
-
Phishing: Despite a decrease in click rates, phishing remains a significant threat. Attackers are now using AI to create highly personalized phishing lures, increasing their success rate.
-
Hacking Machine Identities: The rise of machine identities, such as service accounts and APIs, provides attackers with new avenues for exploitation. These identities often have weak protections, making them attractive targets.
-
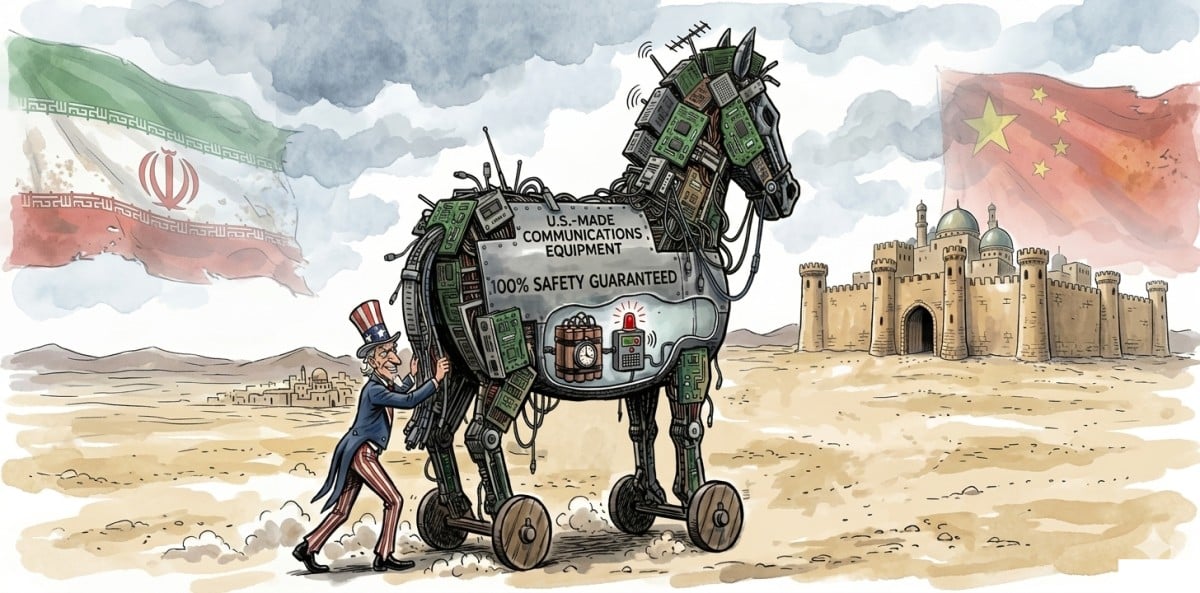
Supply Chain Attacks: The Shai-Hulud attack demonstrated how credential-stealing code can propagate through npm libraries, complicating containment efforts.
Defensive Measures
To counter these evolving threats, organizations need to adopt layered defense strategies. Key recommendations include: In conclusion, understanding these techniques is crucial for cybersecurity professionals. By staying informed about the latest tactics, organizations can better protect their systems against the evolving landscape of cyber threats.
Do Now
- 1.User Training: Educate employees about ClickFix and other social engineering tactics.
- 2.RMM Tool Management: Implement allowlists for RMM tools to prevent misuse.
Do Next
- 3.Phishing-Resistant Authentication: Utilize hardware security keys and password-free methods to enhance security.
- 4.Zero Trust Principles: Adopt a zero trust approach to continuously validate user behavior and device posture.
🔒 Pro insight: The shift towards identity-based attacks indicates a need for organizations to strengthen their authentication mechanisms and user training.