Unicode Overflow Attacks: A New Bypass Method Uncovered
Basically, attackers can trick servers by using special characters that overflow storage limits.
A new attack method called Unicode overflow is being exploited to bypass security measures. This affects web applications and services, putting user data at risk. Companies are urged to update systems and educate teams to prevent these vulnerabilities.
What Happened
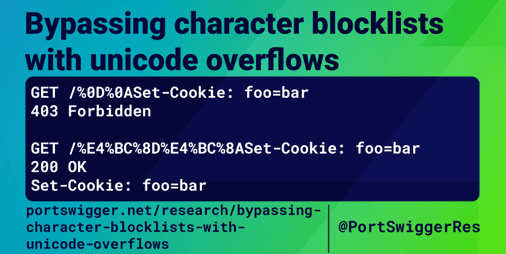
A new method of attack has emerged, known as Unicode overflow. This technique exploits how servers handle Unicode? characters, which can lead to security vulnerabilities?. When a server attempts to store a Unicode? character in a single byte?, it can cause unexpected behavior, allowing attackers to bypass security measures.
In essence, this occurs when the server miscalculates the storage needed for these characters. The maximum value of a byte? is 255, and if a character exceeds this limit, it can lead to truncation? or overflow?. This can allow malicious users to input harmful data that the server may not properly validate, opening the door to various attacks.
Why Should You Care
This issue is particularly concerning for anyone who uses web applications or services. Imagine sending a message or filling out a form, only to have your data manipulated without your knowledge. Unicode overflow attacks can lead to unauthorized access, data breaches, or even complete system compromise.
If you rely on online services for banking, shopping, or communication, you need to be aware of these vulnerabilities?. Just like leaving your front door unlocked, neglecting to understand these risks could allow attackers to waltz right in and exploit your sensitive information. Protecting your data starts with understanding these threats.
What's Being Done
Security experts are already on high alert regarding this new attack vector. Companies are urged to review their systems and implement necessary patches to mitigate these vulnerabilities?. Here are some immediate actions you should consider:
- Update your software and applications to the latest versions.
- Conduct security audits to identify potential weaknesses.
- Educate your teams about the risks associated with Unicode? handling.
Experts are closely monitoring how this attack method evolves and what new exploits may arise from it. Staying informed and proactive is crucial in the fight against these types of cyber threats.
PortSwigger Research