Web Hacking Techniques: 2024's Top 10 Revealed!
Basically, these are the most clever ways hackers break into websites this year.
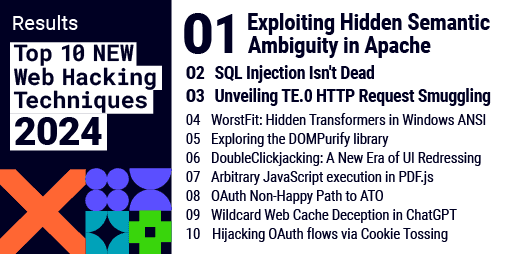
The latest report reveals the top 10 web hacking techniques for 2024. These methods pose risks to everyone online, from personal data theft to financial fraud. Stay informed and protect yourself with the latest cybersecurity practices.
What Happened
Every year, cybersecurity experts gather to highlight the most innovative web hacking techniques. 2024 is no exception, as the latest list showcases ten groundbreaking methods that hackers are using to exploit vulnerabilities. This annual report serves as a crucial resource for developers, security professionals, and anyone interested in understanding the evolving landscape of web security.
The techniques identified this year range from sophisticated phishing schemes to advanced SQL injection methods. Each technique represents a unique approach to breaching web applications, emphasizing the need for constant vigilance in cybersecurity practices. As technology evolves, so do the tactics employed by malicious actors, making it essential to stay informed about emerging threats.
Why Should You Care
If you use the internet, you should care about these hacking techniques. Every time you log into a website or enter personal information, you could be at risk. Think of it like locking your front door; if the lock is weak, anyone can just walk in. Understanding these techniques helps you recognize potential threats and protect your sensitive data.
Imagine your favorite online shopping site getting hacked. Your credit card information could be stolen, leading to financial loss and identity theft. By knowing how hackers operate, you can take steps to safeguard your online presence. Stay informed and proactive to keep your personal and financial information secure.
What's Being Done
Cybersecurity experts and organizations are already responding to these emerging threats. Many are developing new tools and strategies to counteract these hacking techniques. Here are some immediate actions you can take:
- Educate yourself about the latest web security practices.
- Use strong, unique passwords for each of your accounts.
- Enable two-factor authentication wherever possible.
Experts are closely monitoring these techniques to see how they evolve and what new threats may arise. The cybersecurity community is committed to staying one step ahead of hackers to protect users like you.
PortSwigger Research