🎯Hackers are breaking into trucking companies to steal cargo and money. They use smart tricks to hide their tracks and stay in control of the systems they break into, making it hard for the companies to stop them.
What Happened
Security researchers from Proofpoint have been investigating cybercriminal activities targeting the trucking and logistics industry. Their findings reveal that hackers are running sophisticated remote access campaigns that not only steal cargo but also divert payments. This trend is closely linked to organized crime, highlighting the increasing sophistication of cyber-enabled cargo theft.
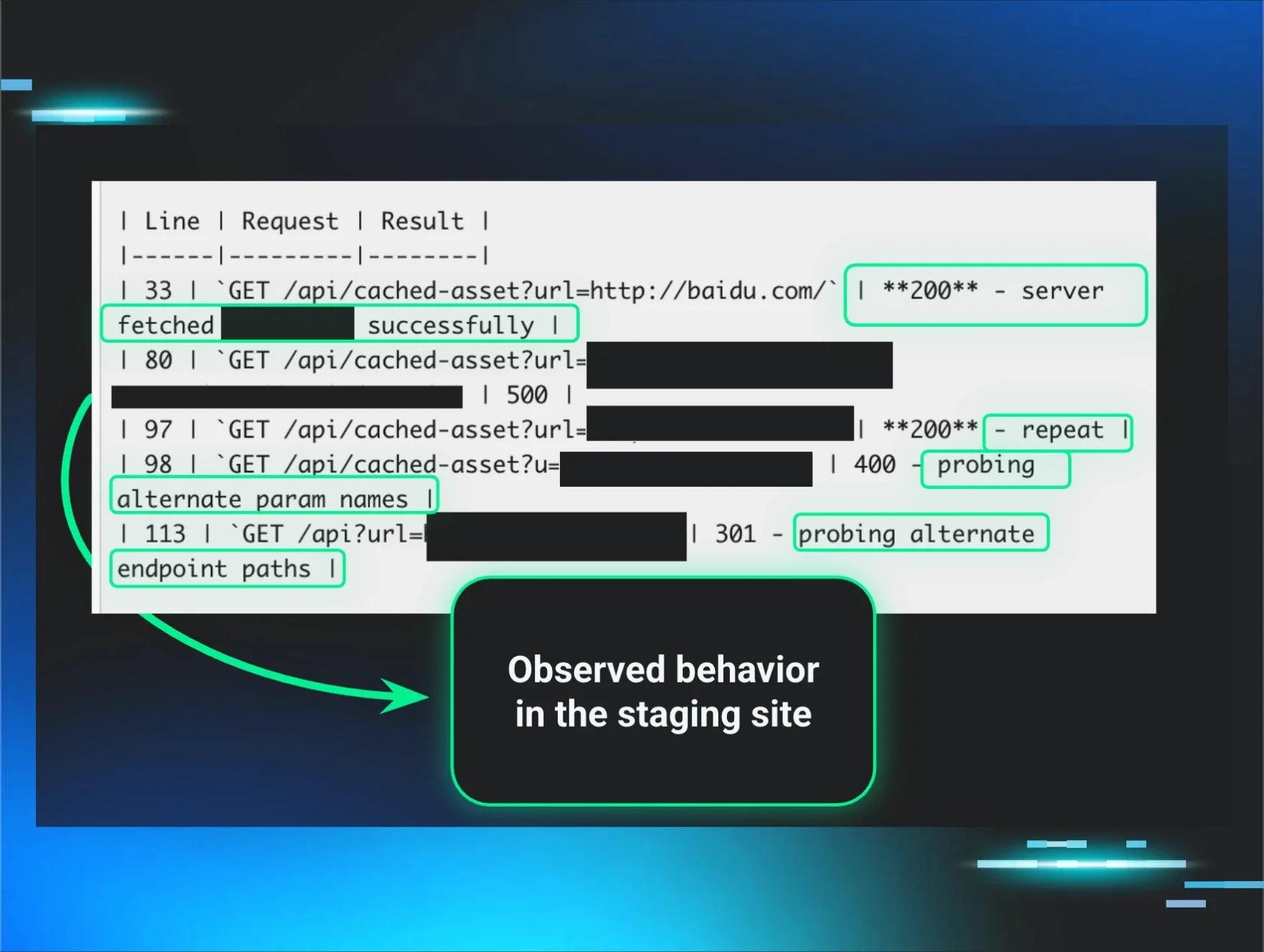
In a controlled decoy environment, researchers executed a malicious payload that had been sent to transportation organizations. This environment remained compromised for over a month, providing invaluable insights into post-compromise operations and the tools used by cybercriminals.
Who's Affected
The logistics sector, particularly small enterprises with fewer than 10 trucks, is particularly vulnerable. These companies often lack robust cybersecurity defenses, making them easy targets for cybercriminals. The attacks have been noted to impact multiple carriers simultaneously through compromised load board platforms.
What Data Was Exposed
Cybercriminals are not just focused on cargo theft; they are also targeting financial information. The attackers have been observed scanning for cryptocurrency wallets, checking PayPal credentials, and accessing financial institutions and money transfer services. They utilize PowerShell scripts to gather user data, browser history, and signs of access to various financial platforms.
Tactics & Techniques
The attackers employ a variety of remote management tools, including multiple instances of ScreenConnect, Pulseway, and SimpleHelp, to maintain persistent access to compromised systems. A notable technique is the use of a 'signing-as-a-service' capability, which allows them to sign malicious components with valid certificates to evade detection. This method has been adapted to bypass recent security measures that target revoked certificates.
In addition to stealing cargo, the attackers focus on broader financial targeting, using custom tools to profile victims and gather sensitive information. They have been observed using over a dozen PowerShell scripts to collect data, including locked files and security tool checks, and reporting findings through secure channels like Telegram.
What You Should Do
Organizations in the transportation and logistics sectors should enhance their cybersecurity measures by monitoring for unauthorized remote management tools and suspicious PowerShell activity. It is crucial to implement robust security protocols to protect against these evolving threats.
The findings underscore a growing trend where cybercriminals leverage legitimate trust mechanisms to execute their attacks, emphasizing the need for heightened vigilance in the logistics industry.
The rise in cyber-enabled cargo theft is not just a logistical challenge but a significant financial threat, demanding immediate action from stakeholders in the industry to bolster their cybersecurity defenses.