🎯Basically, Event 5156 helps identify who is making requests to Active Directory, even when they try to hide their identity.
What Happened
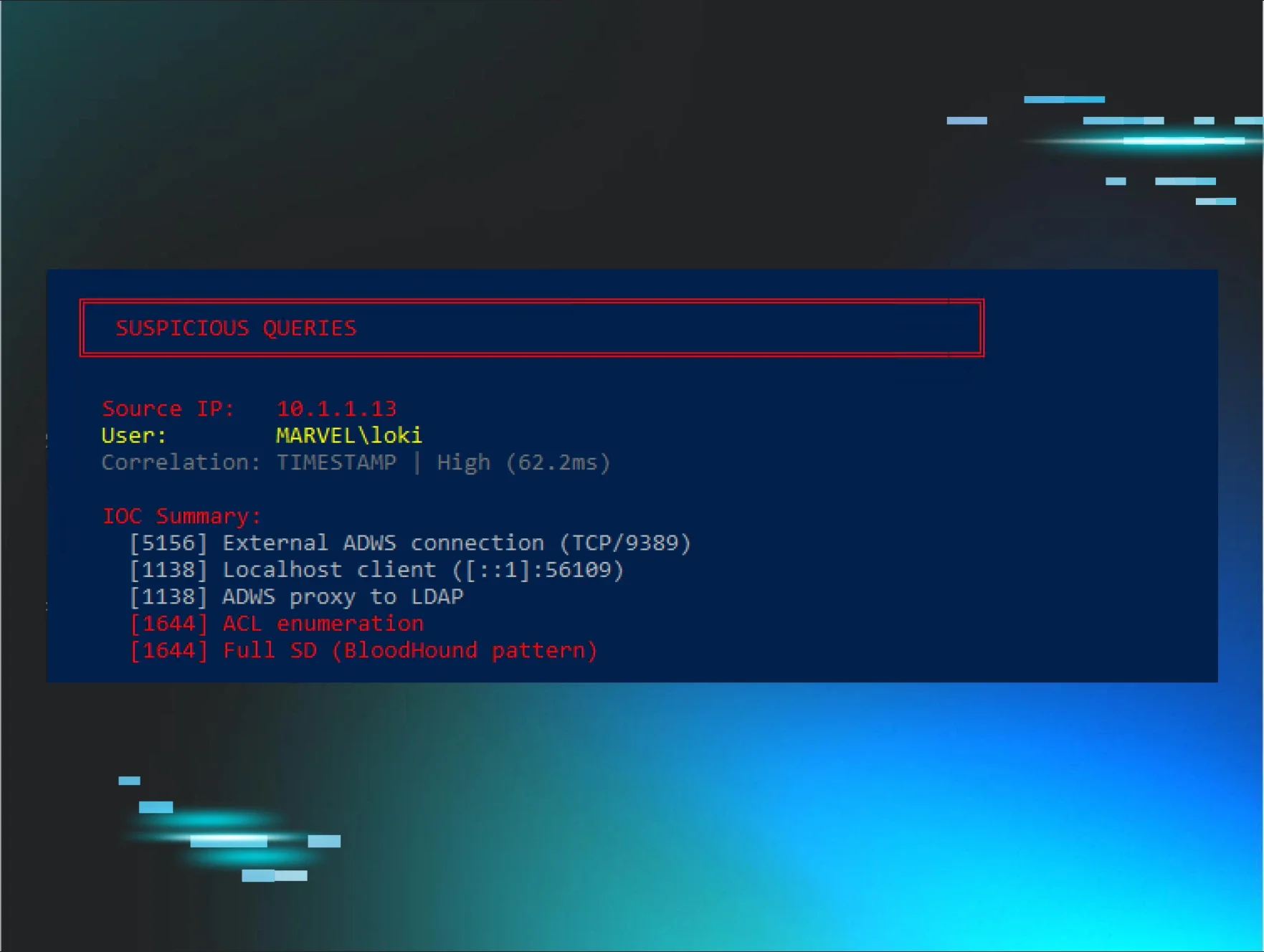
A recent discussion in the BloodHound Slack channel highlighted a significant challenge in attributing Active Directory Web Services (ADWS) queries. The problem arises because ADWS masks the attacker's real IP address, instead logging localhost in the event records. However, by correlating Event 5156 with a precise timing window, security professionals can trace back these queries to their actual source.
The Attribution Challenge
When an ADWS query is executed, the logging often shows the connection originating from the Domain Controller (DC) itself, making it difficult to pinpoint the actual user or machine initiating the request. This situation complicates detection efforts, especially in environments where stealthy enumeration techniques are employed. Traditional logging methods do not provide sufficient detail to identify the true source of these queries.
How Event 5156 Works
Event 5156 is generated by the Windows Filtering Platform (WFP) every time a network connection is allowed. This event captures the application responsible for the connection, providing a clearer picture than generic logs. For instance, instead of seeing a generic svchost.exe, you will see microsoft.activedirectory.webservices.exe, which is crucial for understanding the context of the connection. This event occurs before ADWS translates the request into an internal LDAP call, which is when the real IP gets replaced with localhost.
Correlating Events for Attribution
The breakthrough comes from correlating Event 5156 with Event 1644, which logs the internal LDAP query. By analyzing the timestamps of these events, security analysts can effectively trace back the source of the ADWS queries. The correlation relies on a tight timing window of approximately 60-80 milliseconds between the external Event 5156 and the corresponding Event 1644. This method allows for accurate attribution, even when the original connection event has rolled out of the logs.
Building a Detection Script
To automate this process, a detection script was developed that collects relevant events and attempts to correlate them based on both port and timing. This script can identify the source IP of LDAP queries in real-time, providing immediate insights during enumeration activities. The ability to monitor these events as they happen is critical for proactive threat detection.
Conclusion
Event 5156 presents a valuable opportunity for security professionals to enhance their detection capabilities in Active Directory environments. By leveraging this event, organizations can overcome the challenges posed by ADWS's inherent obfuscation of source IPs, leading to improved attribution and response strategies. As the landscape of cyber threats continues to evolve, utilizing such techniques will be essential for maintaining robust security postures.
🔒 Pro insight: This approach leverages existing logging mechanisms, offering a practical solution to a long-standing attribution challenge in ADWS environments.



.webp)
