EngageLab SDK Flaw Exposes Private Data on 50M Android Devices
Significant risk — action recommended within 24-48 hours
Basically, a flaw in an app tool lets other apps access private data on millions of Android devices.
A critical flaw in EngageLab SDK exposes private data on 50 million Android devices, including 30 million crypto wallets. This vulnerability allows apps to bypass security protections, risking sensitive information. Developers have released a patch, but the incident underscores the risks of third-party SDKs.
What Happened
A serious vulnerability in the EngageLab SDK has been discovered, affecting up to 50 million Android users. This flaw allows apps to bypass Android's security measures, potentially exposing sensitive data, including information from over 30 million crypto wallets. Microsoft researchers identified this critical flaw, which enables unauthorized access to protected components within Android apps.
The Flaw
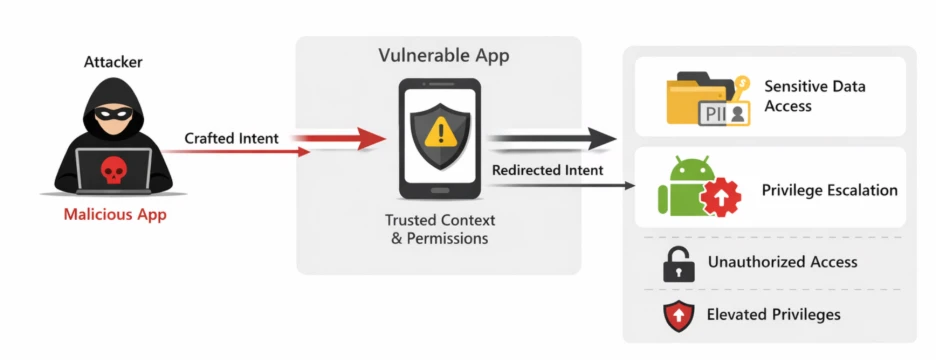
The vulnerability arises from an intent redirection issue. In simple terms, it allows a malicious app to manipulate the contents of an intent sent from a vulnerable app. This manipulation enables the attacker to execute actions with the privileges of the vulnerable app, leading to privilege escalation and unauthorized data access.
What's at Risk
The flaw primarily affects apps in the crypto and digital wallet ecosystem, making it particularly severe. The risk includes:
- Unauthorized access to sensitive data
- Exposure of private files
- Privilege escalation within the Android environment
Patch Status
EngageLab addressed the issue in version 5.2.1, released on November 3, 2025. The patch involved making the vulnerable component non-exported, which prevents other apps from accessing it. Following the disclosure, affected apps were removed from the Google Play Store.
Immediate Actions
To safeguard your apps, it is crucial to:
- Review the merged Android manifest when integrating third-party SDKs.
- Identify any components or permissions that could compromise your app's security.
Conclusion
While no active exploitation has been confirmed, the EngageLab SDK flaw highlights significant risks associated with third-party SDKs in mobile applications. As mobile wallets and high-value apps grow in popularity, even minor flaws can have widespread implications. Developers must remain vigilant and proactive in securing their applications against such vulnerabilities.
🔍 How to Check If You're Affected
- 1.Review the Android manifest for exported components.
- 2.Check for updates to the EngageLab SDK.
- 3.Monitor app permissions and access controls.
🔒 Pro insight: This incident underscores the critical need for developers to audit third-party SDKs to mitigate potential risks in mobile applications.