.webp)
🎯Basically, Iran's intelligence uses different hacker names to run a big cyber attack together.
What Happened
Iran’s Ministry of Intelligence and Security (MOIS) has been conducting a complex cyber campaign using three distinct hacker identities: Homeland Justice, Karma/KarmaBelow80, and Handala. Initially thought to be independent hacktivist groups, investigations revealed that these personas are part of a single, state-directed operation. This campaign combines cyber intrusions, data theft, and psychological influence tactics, targeting governments and organizations across various countries.
Who's Behind It
The campaign began in 2022 with Homeland Justice attacking the Government of Albania. MOIS actors had infiltrated Albanian government systems about fourteen months prior, allowing them to steal sensitive documents and deploy destructive tools. This attack was not just technical; it was a carefully orchestrated public influence event, showcasing the group's ability to blend hacking with propaganda.
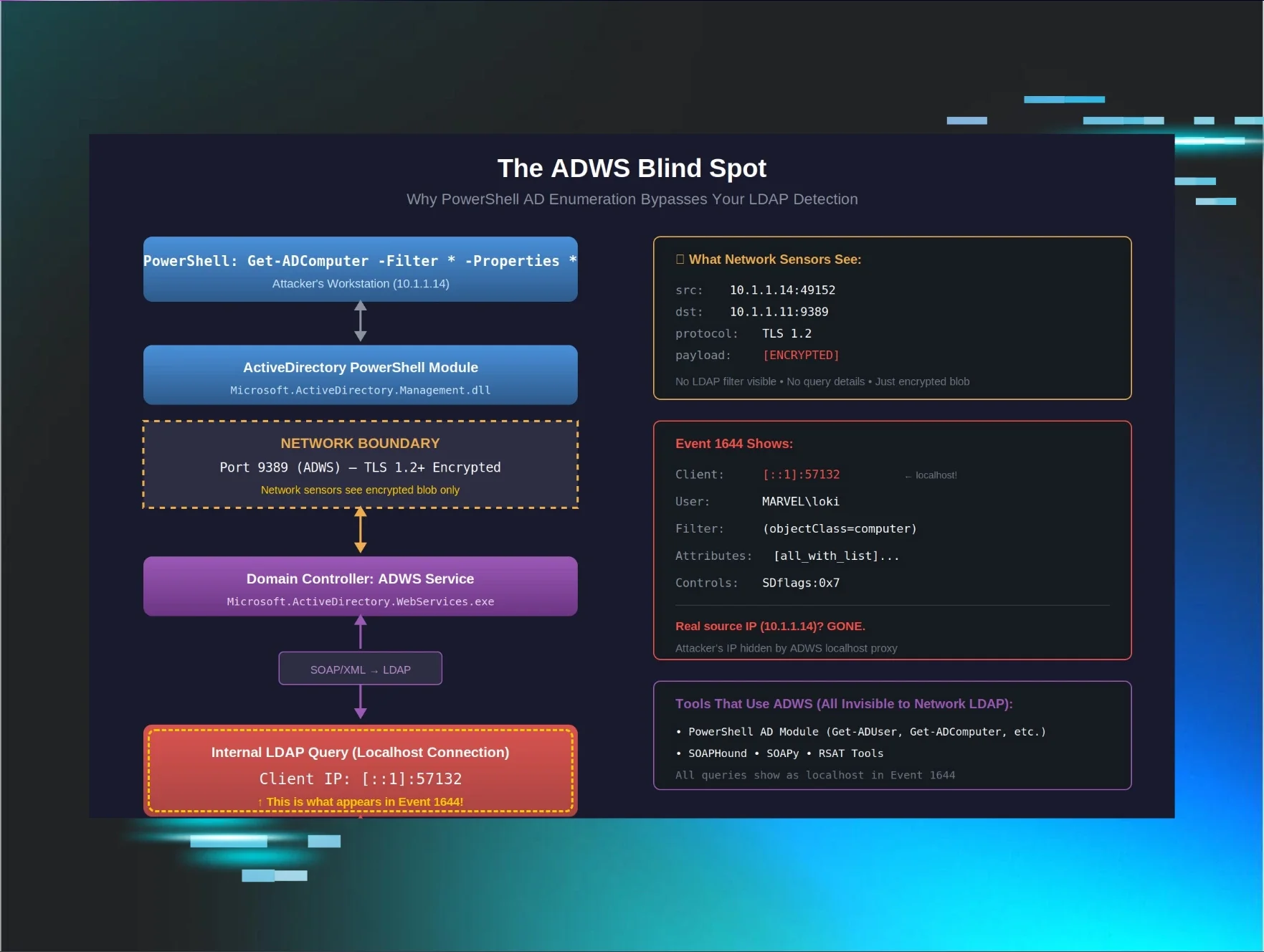
Tactics & Techniques
As the campaign evolved, the same threat actors transitioned to the Karma and KarmaBelow80 personas, shifting their focus to Israeli organizations by late 2023. Analysts noted that the tools and methods remained consistent across these rebranded campaigns, indicating a well-coordinated effort. The Handala persona emerged in 2024, emphasizing information operations, including curated data leaks and targeted harassment of journalists and dissidents.
Defensive Measures
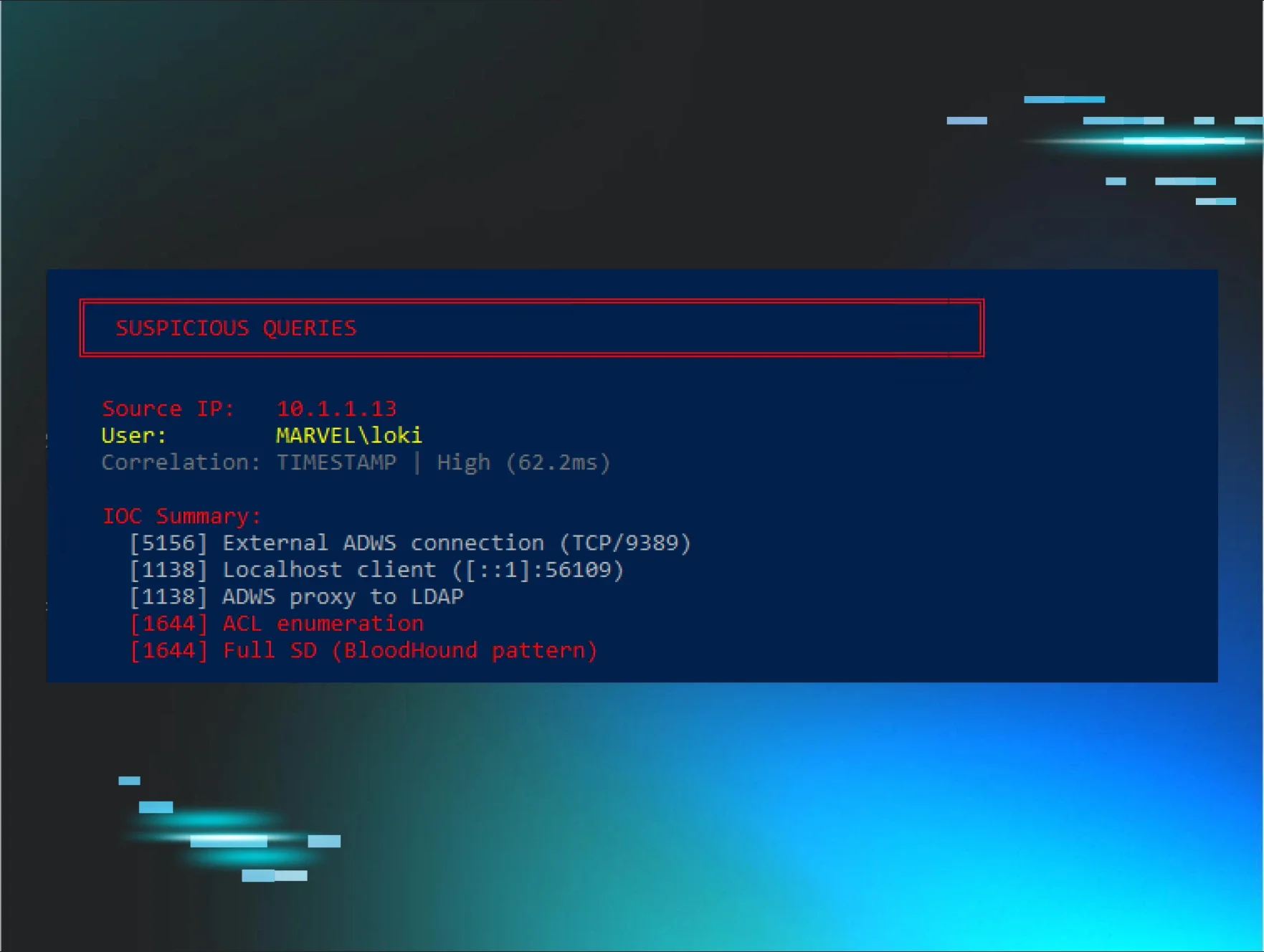
In response to these activities, the U.S. Justice Department seized four domains linked to these operations. Security organizations recommend that entities monitor for suspicious activity, especially exploitation of internet-facing services like Microsoft SharePoint, which was the initial access method used in the Albania campaign.
What You Should Do
Organizations should implement strict network segmentation, regularly audit privileged account activities, and deploy endpoint detection tools to identify manual intrusion behaviors. Monitoring domain infrastructure associated with MOIST GRASSHOPPER is crucial to reduce ongoing exposure to these threats. Blocking domains flagged in the Justice Department’s seizure can also mitigate risks.
🔒 Pro insight: The use of multiple personas under a single operational framework highlights the evolving complexity of state-sponsored cyber campaigns.