🎯Basically, companies can use insider risks to improve security and show value.
What Happened
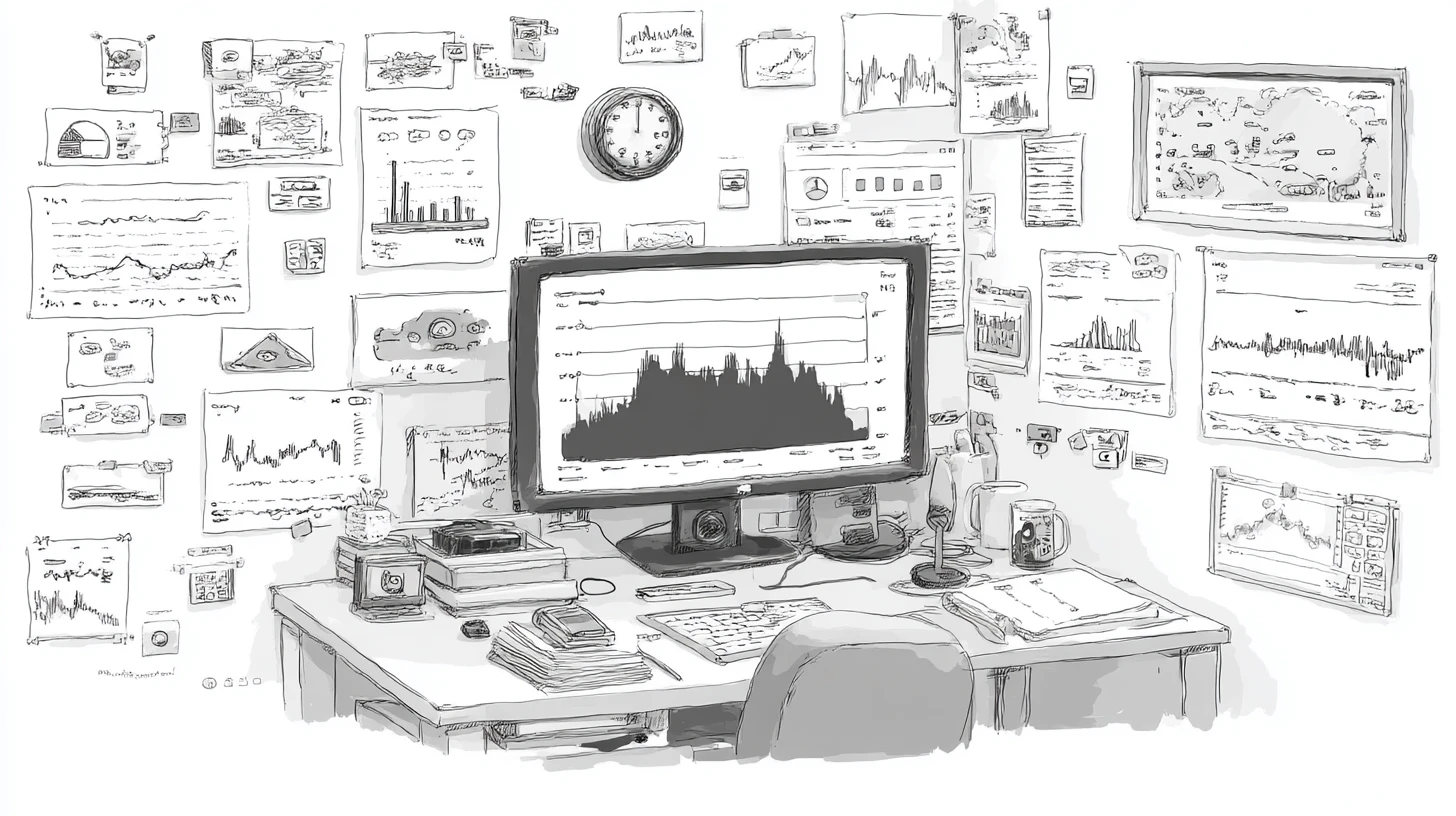
In today's fast-paced digital landscape, organizations face increasing challenges related to insider risks. With a more distributed workforce and rapid data movement, traditional security controls often fall short. A recent article highlights how businesses can turn these risks into measurable value through effective insider risk management strategies.
Why It Matters
Insider risks, such as lost intellectual property (IP) and policy violations, can significantly impact an organization's bottom line. According to Mimecast, 60% of breaches involve human error, underscoring the importance of addressing these vulnerabilities. By leveraging insider risk management solutions, companies can not only mitigate these risks but also demonstrate the value of their security investments.
Key Strategies for Insider Risk Management
- Identify and Mitigate Shadow IT Risks: Employees often resort to unauthorized tools, creating security blind spots. Modern solutions can detect risky behavior and educate employees in real-time to prevent unauthorized data sharing.
- Expose Hidden Risks: Remote work can lead to employees taking on secondary jobs, potentially moving sensitive data without oversight. Insider risk platforms help uncover abnormal data movement patterns, protecting IP effectively.
- Prevent IP Theft: With a significant portion of data uploaded to generative AI tools being source code, organizations must adopt advanced insider risk solutions. These tools provide visibility into sensitive data movements, enabling early intervention.
- Detect Intentional Leaks: Not all data leaks are accidental. Insider risk platforms focus on behavioral patterns, allowing organizations to detect and block suspicious activity before it escalates.
- Understand Obfuscation Techniques: Employees may use simple tactics to evade detection, such as renaming files or compressing data. Insider risk management tools analyze user behavior to identify these tactics and prevent data exfiltration.
What You Should Do
Organizations should evaluate their current security measures and consider investing in insider risk management solutions. Key questions to ask include: By addressing insider risks proactively, organizations can enhance their security posture while demonstrating the value of their investments in cybersecurity.
Do Now
- 1.Can the solution detect user activity across managed and unmanaged devices?
- 2.Does it provide context around data movement?
Do Next
🔒 Pro insight: Investing in insider risk management not only mitigates threats but also enhances overall business resilience and compliance.