LDAP Detection Rules Fail Due to Whitespace Issues
Basically, LDAP rules that work in testing don't work in real life because of extra spaces.
LDAP detection rules are failing in production due to whitespace issues. This affects organizations relying on LDAP for security. It's crucial to fix these rules to avoid missing critical alerts.
What Happened
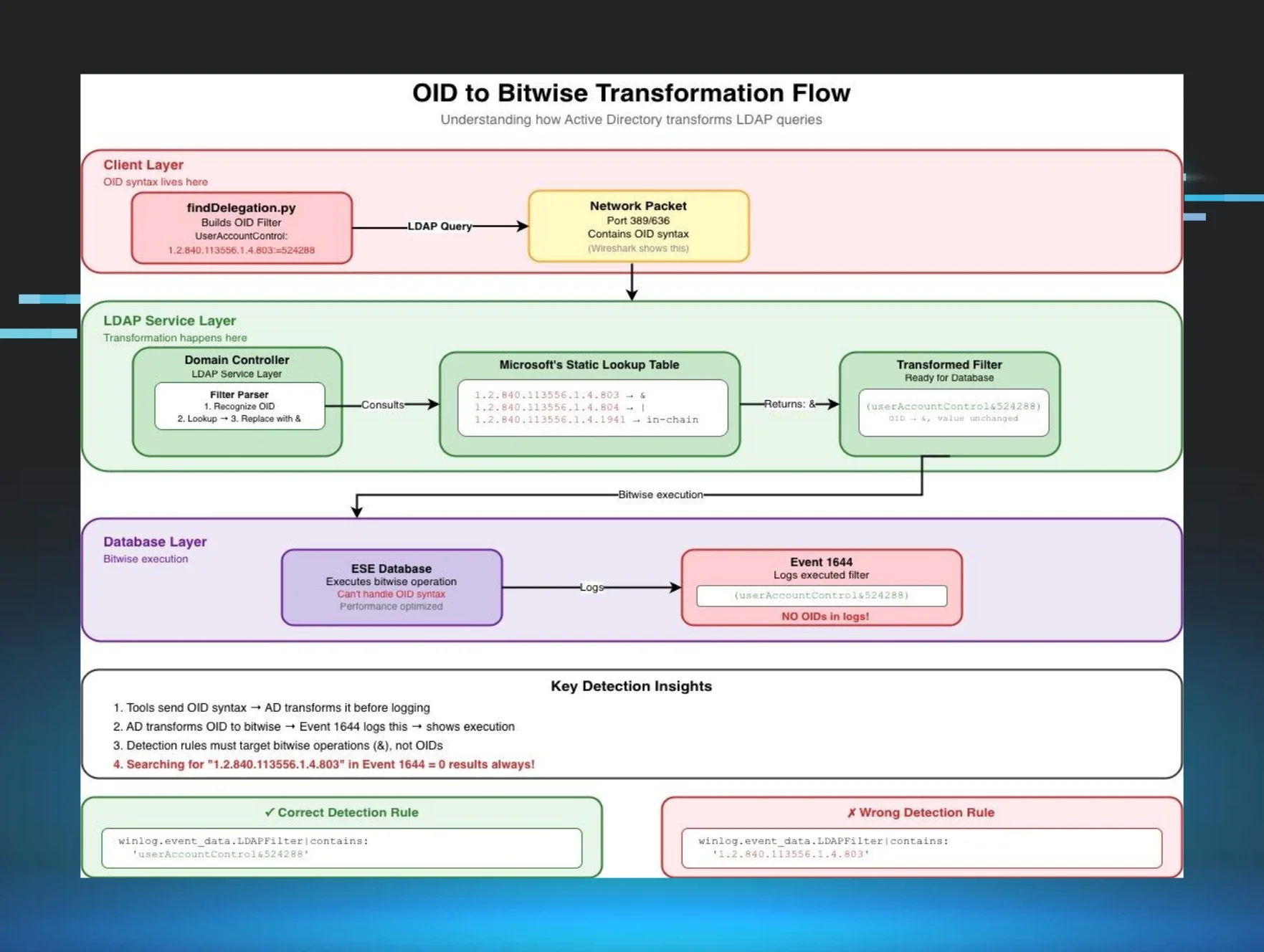
Have you ever set up a system that works perfectly in testing, only to have it fall flat in the real world? This is happening with LDAP detection rules, specifically with Event 1644, where whitespace variations are causing significant issues. These rules might seem effective during lab tests, but when deployed in production, they often fail to trigger alerts as expected.
The problem arises from how different systems interpret whitespace. In a lab environment, you might have controlled inputs, but in production, the data can come from various sources, leading to unexpected whitespace characters. This inconsistency can break the logic of your Sigma rules, rendering them ineffective when you need them most.
Why Should You Care
Imagine relying on a security system that fails to detect a threat because of something as simple as extra spaces in the data. This could leave your organization vulnerable to attacks, as malicious activities might go unnoticed. If your company relies on LDAP for authentication or directory services, this issue is even more critical.
Think of it like trying to read a sentence with random spaces inserted — it becomes confusing and may lead to misunderstanding the message. In the same way, your detection rules can misinterpret important security events, putting your data and systems at risk. You need to ensure your detection rules are robust enough to handle real-world data variations.
What's Being Done
Experts are actively working on solutions to address the LDAP whitespace problem. Here are some immediate steps you can take:
- Review your Sigma rules and ensure they account for whitespace variations.
- Test your detection rules in a production-like environment to identify potential failures.
- Update your systems to handle different whitespace characters effectively.
Security professionals are closely monitoring this situation, as more organizations face similar challenges with their detection rules. Keeping your systems updated and vigilant will be crucial as you navigate these complexities.