🎯NIST is changing how it tracks software vulnerabilities because there are too many to handle. Now, they will only focus on the most serious issues, which means some less critical problems might not get the attention they need.
What Happened
The National Institute of Standards and Technology (NIST) has announced a significant change in its approach to analyzing vulnerabilities. Overwhelmed by a surge in reported flaws, NIST will now prioritize its efforts on vulnerabilities that are critical to federal systems and those actively exploited in the wild. This decision comes as the agency grapples with a backlog and increasing submissions, which have surged by 263% from 2020 to 2025. In fact, submissions during the first three months of 2026 are nearly one-third higher than the same period last year, prompting NIST to adjust its strategy.
Who's Affected
This change will impact not only NIST and its operations but also the broader cybersecurity community, including researchers, threat hunters, and organizations that rely on the National Vulnerability Database (NVD) for vulnerability assessments. Companies and security professionals will need to adjust their focus based on the new criteria set by NIST. The agency's decision to limit the enrichment of CVEs means that vulnerabilities deemed less critical may not receive the same level of attention or resources, potentially leading to gaps in security awareness for some organizations.
What Data Was Exposed
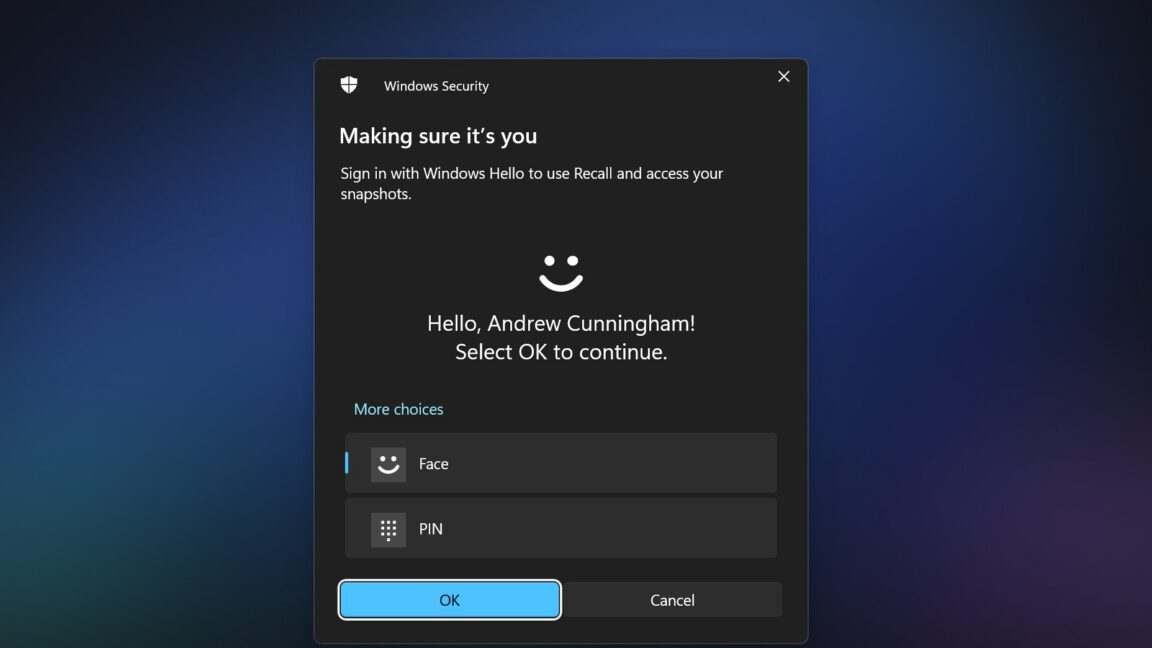
While NIST will still list all CVEs in the NVD, only those that meet the new criteria will be enriched with additional details. This includes descriptions, severity scores, and other pertinent information. NIST has stated that it will now only enrich vulnerabilities that appear in a federal catalog of exploited vulnerabilities organized by the Cybersecurity and Infrastructure Security Agency (CISA). Bugs added to this catalog will be enriched within one day of notice from CISA.
What You Should Do
Organizations should stay informed about NIST's new prioritization strategy. Here are some steps to consider:
Containment
- 1.Review your vulnerability management processes to align with NIST’s new focus areas.
- 2.Monitor the NVD regularly for updates on critical vulnerabilities that may affect your systems.
Remediation
The Implications
NIST's decision reflects a necessary shift to manage the overwhelming influx of vulnerability reports. By narrowing its focus, the agency aims to stabilize the NVD program and ensure it remains a reliable resource for cybersecurity information. However, this may also lead to a reliance on private companies and other organizations for vulnerability assessments, which could change the landscape of cybersecurity research and defense strategies. Furthermore, NIST has acknowledged that even bugs that don’t meet the new criteria “may have a significant impact on affected systems,” indicating that the new rules may not catch every potentially high-impact CVE.
Backlog and Funding Issues
NIST has faced significant challenges in managing its backlog of CVE submissions, with reports indicating that 90% of submissions were not enriched due to staff cutbacks and funding issues. The agency has pledged to clear this backlog but admitted that it would be impossible to enrich the thousands of records left from those funding challenges. As a result, backlogged CVEs with an NVD publish date earlier than March 1, 2026, will be moved into a “Not Scheduled” category, with only those meeting the new criteria being prioritized for enrichment.
Expert Opinions
Cybersecurity experts have expressed concern over NIST's new approach. Trey Ford from Bugcrowd highlighted that the research community has long understood that centralizing vulnerability triage at such a volume is unfeasible. He emphasized that remediation priorities should be driven by real-world exploitability rather than database metadata, necessitating continuous input from human researchers actively engaged in live environments. The changes at NIST signal a critical juncture in how vulnerabilities are managed and assessed in the cybersecurity landscape.
NIST's decision to limit CVE enrichment reflects the growing pressure on cybersecurity resources, highlighting the need for organizations to adapt their vulnerability management strategies accordingly.