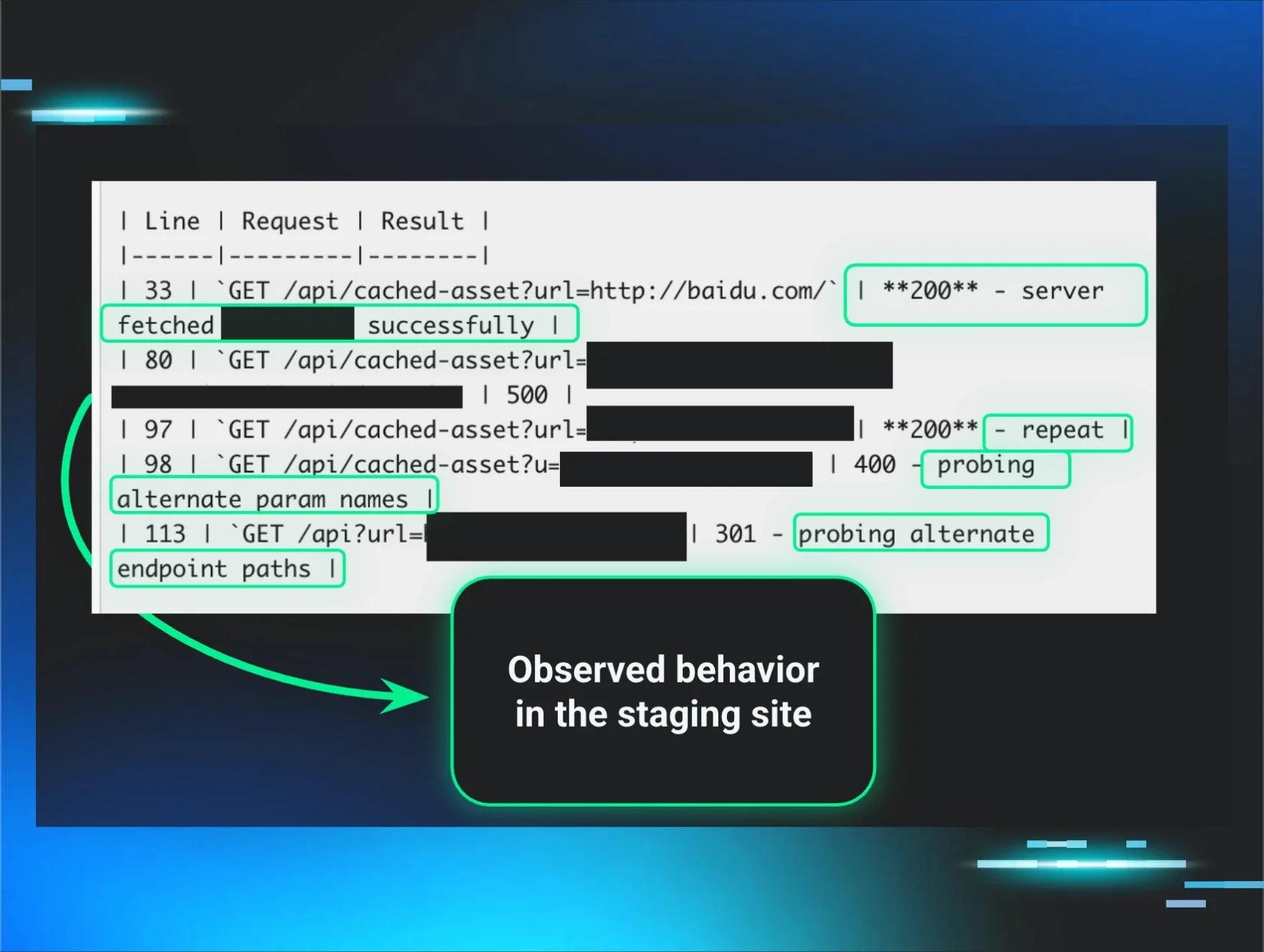
🎯Basically, attackers are trying to find proxy servers using specific URL patterns.
The Threat
Recent activity in our honeypots has highlighted a growing trend in scans targeting proxy servers. Attackers often use specific URL patterns to exploit vulnerabilities. The common approach is to manipulate the host header or incorporate the hostname in the URL. This weekend, we observed a notable shift in the scanning patterns.
Who's Behind It
While the exact identities of the attackers remain unknown, the techniques employed are typical of cybercriminals seeking to exploit proxy servers. These scans are often automated, utilizing bots to probe various IP addresses for weaknesses. The goal is usually to find a way to redirect traffic or access sensitive data through these proxies.
Tactics & Techniques
The attackers frequently use common URL prefixes, such as "/proxy/", to trigger the proxy server's response. This tactic is effective because many systems are configured to handle such requests. By crafting requests that exploit these configurations, attackers can potentially gain unauthorized access or manipulate data flows.
Defensive Measures
To protect against these types of scans, organizations should implement several key strategies: By staying vigilant and proactive, organizations can better defend against these evolving threats.
Do Now
- 1.Regularly monitor logs for unusual patterns or requests.
- 2.Employ intrusion detection systems to identify and block suspicious activity.
Do Next
- 3.Ensure that proxy servers are properly configured to reject unauthorized requests.
- 4.Educate staff about the risks associated with proxy exploitation and the importance of maintaining secure configurations.
🔒 Pro insight: The shift in scanning patterns suggests attackers are adapting their tactics, emphasizing the need for continuous monitoring and proactive defense strategies.