🎯Basically, the book explains how understanding people can improve security measures.
What Happened
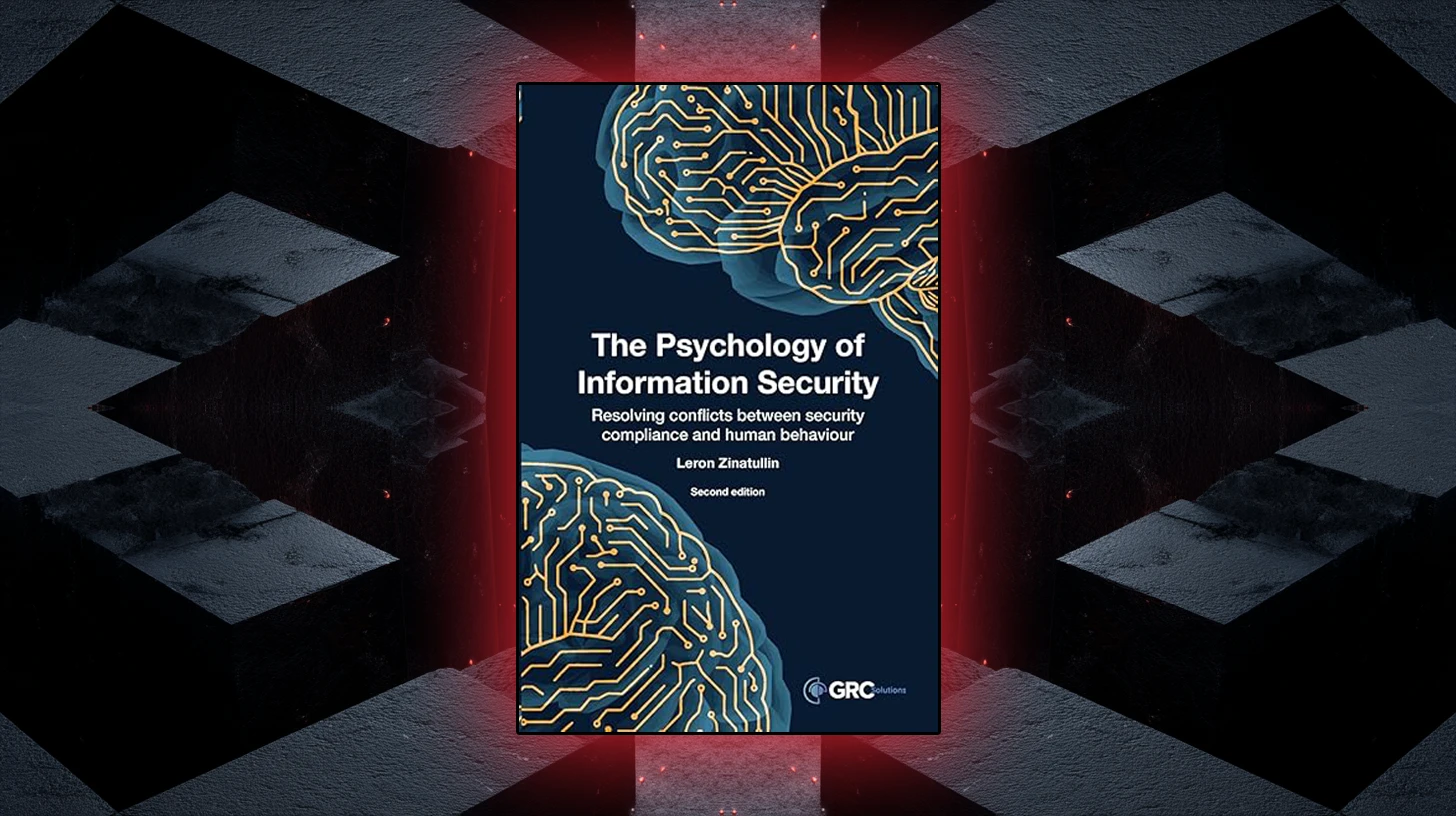
Leron Zinatullin’s second edition of The Psychology of Information Security delves into the crucial relationship between human behavior and security controls. The book argues that security measures often fail when they overlook the people who must implement them. By integrating insights from organizational psychology and usability research, Zinatullin provides a roadmap for creating more effective security policies.
Key Concepts
The book is divided into two main sections. The first half focuses on foundational topics such as risk management, communication, and decision-making psychology. Zinatullin emphasizes the importance of understanding stakeholder influence and change management in crafting security policies. The second half applies these principles to practical aspects like usability, culture, and behavioral change.
One of the standout chapters discusses the FBI's Crisis Negotiation Unit’s behavioral change stairway model. This model illustrates that successful influence requires building rapport and listening before attempting to change behavior.
Practical Insights
Chapter 9 is particularly instructive, as Zinatullin uses fictional employee personas to demonstrate how poorly designed security controls can create new risks. He highlights five ISO 27001 malware-protection controls, showing that a lack of consideration for employee workflows can lead to compliance challenges.
In Chapter 11, the author identifies three key reasons for non-compliance among employees: 1) a lack of clear motivation to comply, 2) high compliance costs, and 3) structural impossibilities due to inadequate tools. This insight is critical for security professionals aiming to enhance compliance.
Behavioral Change Models
Zinatullin introduces the COM-B model, which stands for Capability, Opportunity, and Motivation. This model serves as a diagnostic tool to identify the right interventions for compliance gaps. Additionally, he discusses the Fogg Behavior Model, which adds a prompt as a necessary element for behavior change.
The chapter on nudges and boosting explains how altering choice architecture can lead to quick results, while boosting focuses on enhancing decision-making skills for long-term change. Zinatullin argues that improving a single security habit can lead to broader positive behavioral shifts across an organization.
Conclusion
The Psychology of Information Security is a valuable resource for security professionals, particularly those working across organizational boundaries. It provides a solid foundation in behavioral science as it relates to security, making it a useful tool for those looking to advocate for people-centered policy design. However, readers seeking technical guidance on security controls may need to look elsewhere.
🔒 Pro insight: Zinatullin’s focus on behavioral science highlights a critical gap in traditional security approaches, emphasizing the need for user-centric policy design.