🎯Basically, countries want to keep their data safe from future quantum computers by using strong security designs.
What Changed
Across Europe, the conversation about privacy and cybersecurity is evolving. It's no longer just about following GDPR rules. Now, organizations are focusing on digital sovereignty as a key priority. This shift is driven by geopolitical factors, regulatory caution, and a desire for certainty in how their data is managed. European organizations are increasingly demanding assurance that their encryption and data are secure from external influences.
This new climate has three main expectations: alignment with European regulations, customer control over data, and assurance that no hidden access points exist in their systems. Solutions that cannot clearly communicate these principles are likely to face resistance from organizations that prioritize sovereignty.
Why Architecture Matters More Than Ever
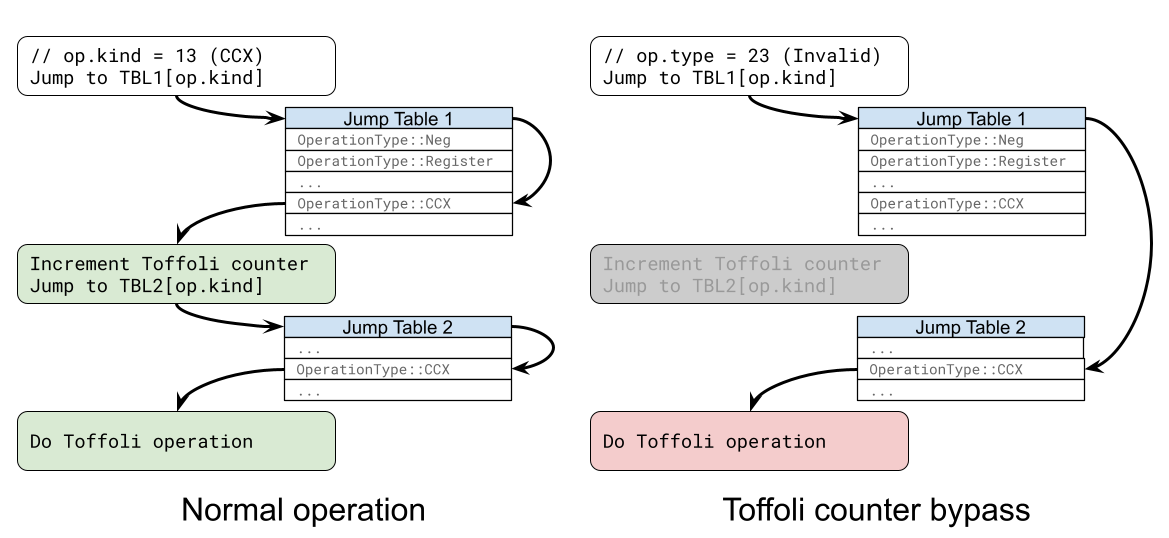
The traditional approach to encryption has been to set it up and forget about it. However, with the rise of quantum computing and AI-driven cyber operations, this approach is no longer viable. Attackers are using Harvest Now, Decrypt Later (HNDL) tactics, collecting encrypted data now with plans to decrypt it later as quantum technology advances.
As a result, the focus has shifted from merely asking if a solution is quantum-safe to questioning who controls the cryptographic system. The answer lies in robust architectural design. By securing the network layer and separating key management from data handling, organizations can enhance their security without compromising customer data.
European Regulatory Alignment and EUCC
European regulators expect that any cryptographic solution aligns with EU-recognized certification pathways. The EU Cybersecurity Certification (EUCC) is a key standard that demonstrates a solution's commitment to European regulations. This certification provides independent assurance that the architecture meets security standards recognized across EU member states.
Additionally, compliance with internationally recognized standards, like FIPS 140-3, further validates the architecture's security. This combination of local and international standards signals transparency and a commitment to high security, which is crucial for organizations operating in Europe.
Sovereignty Through Crypto-Agility
Another important aspect of the current privacy climate is the recognition that cryptographic solutions must be adaptable. As standards evolve, organizations need to be able to update their algorithms without overhauling their entire infrastructure. Crypto-agility allows for centralized updates to cryptographic methods without disrupting operations.
This flexibility is vital for sectors like critical infrastructure and regulated industries. By ensuring that cryptographic management is separate from applications, organizations can maintain control and adapt to new regulations without sacrificing security or operational integrity. In this way, sovereignty is achieved not through isolation, but through well-designed architectural integrity.
🔒 Pro insight: The emphasis on architectural integrity reflects a growing recognition that cybersecurity must evolve alongside emerging quantum threats.