🎯Basically, routers need better security to prevent hackers from getting in.
What Happened
In recent years, network edge devices like routers, firewalls, and VPN concentrators have become the primary targets for cyberattacks. Research indicates that threat actors are now focusing more on these devices than on traditional endpoints like PCs. This shift is particularly concerning for Dutch enterprises, where many business-grade routers have been deployed in home offices with minimal security oversight.
Why Routers Have Become the Weakest Link
Routers often remain untouched for long periods. Many devices are left with default settings and lack automatic updates, making them vulnerable to exploitation. This trend is alarming, especially as hybrid working environments have proliferated since 2020, increasing the risk of attacks on these critical devices.
10 Hardening Steps for 2026
Security teams should implement the following hardening measures as a baseline:
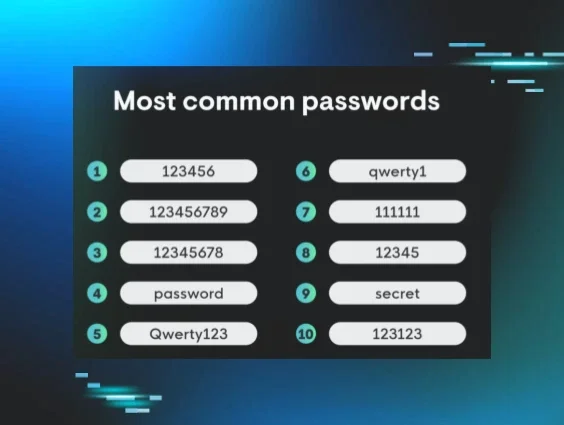
- Audit and replace all default credentials: Ensure every device has unique, complex credentials.
- Disable unused remote management interfaces: Limit remote access to approved IP ranges or use a VPN.
- Segment networks using VLANs: This helps contain breaches and limits lateral movement.
- Implement automated firmware monitoring: Stay ahead of vulnerabilities by automating firmware checks.
- Disable UPnP and legacy protocols: Turn off unnecessary services to reduce exposure.
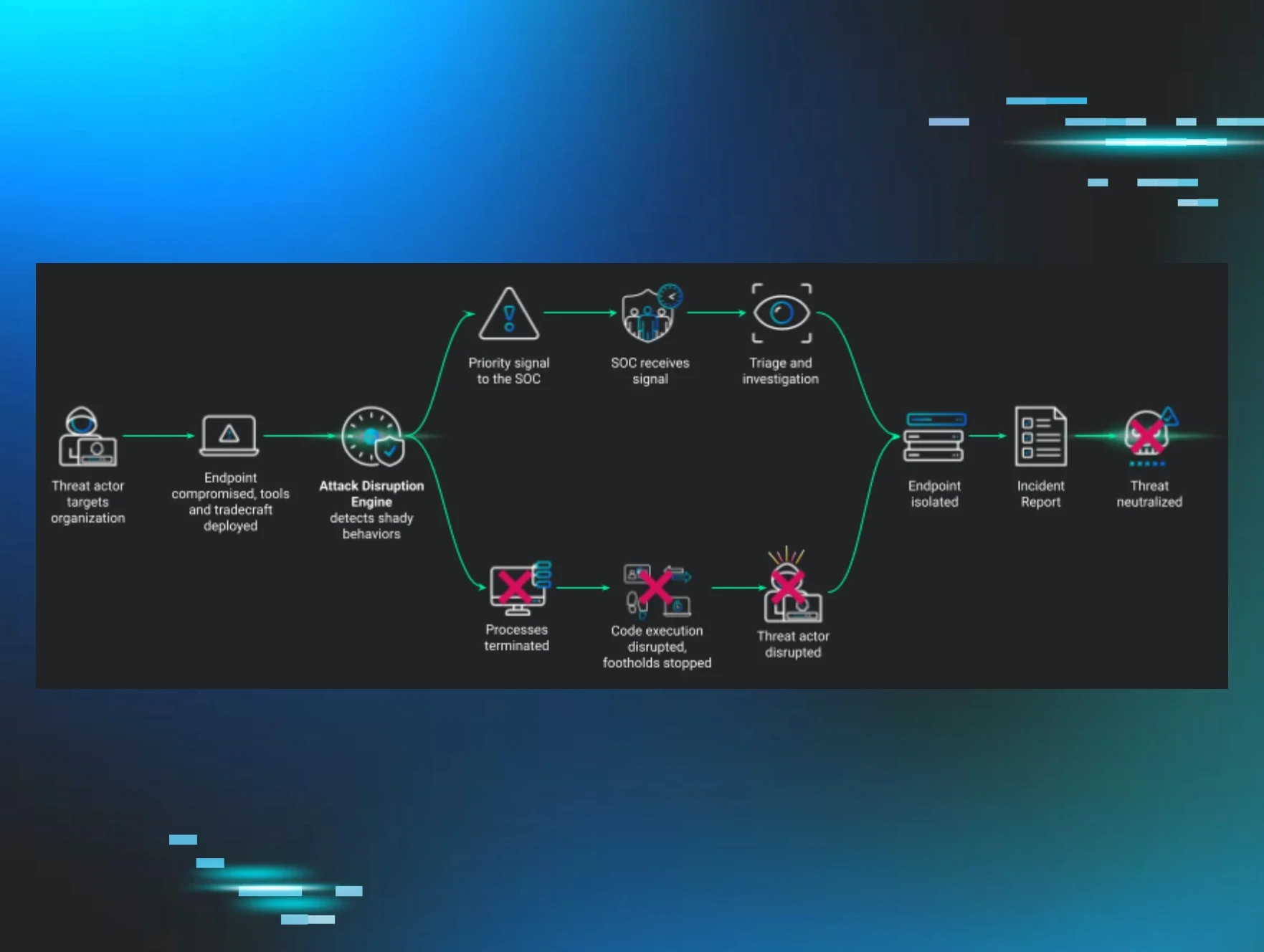
- Enable logging and forward to a SIEM: Collect router telemetry for better anomaly detection.
- Apply access control lists at the device level: Limit management interface access to specific IP addresses.
- Conduct quarterly configuration reviews: Regularly check configurations against a known baseline.
- Test for known CVEs during patch cycles: Include routers in vulnerability scans regularly.
- Align hardening procedures with NIS2 obligations: Ensure compliance with European network security regulations.
The Human Factor in Network Security
Technical controls are only part of the solution. Often, router vulnerabilities persist due to a lack of clear ownership or awareness of security practices. In many organizations, IT responsibilities are spread thin, leading to gaps in security oversight.
Building a Sustainable Hardening Programme
A one-time hardening effort is not enough. Organizations should treat router security as an ongoing discipline. Key elements include:
- Maintaining an updated device inventory.
- Documenting changes in router configurations.
- Integrating firmware vulnerability alerts into patch management workflows.
- Conducting regular tabletop exercises that include network edge device scenarios.
As regulatory scrutiny increases, particularly under the NIS2 Directive, the importance of router security hardening cannot be overstated. It is now a critical component of any robust enterprise security posture as we head into 2026.
🔒 Pro insight: The shift towards targeting routers highlights the need for proactive security measures, especially in hybrid work environments.