🎯Basically, SmokedMeat shows how attackers can exploit weaknesses in software development processes.
What It Does
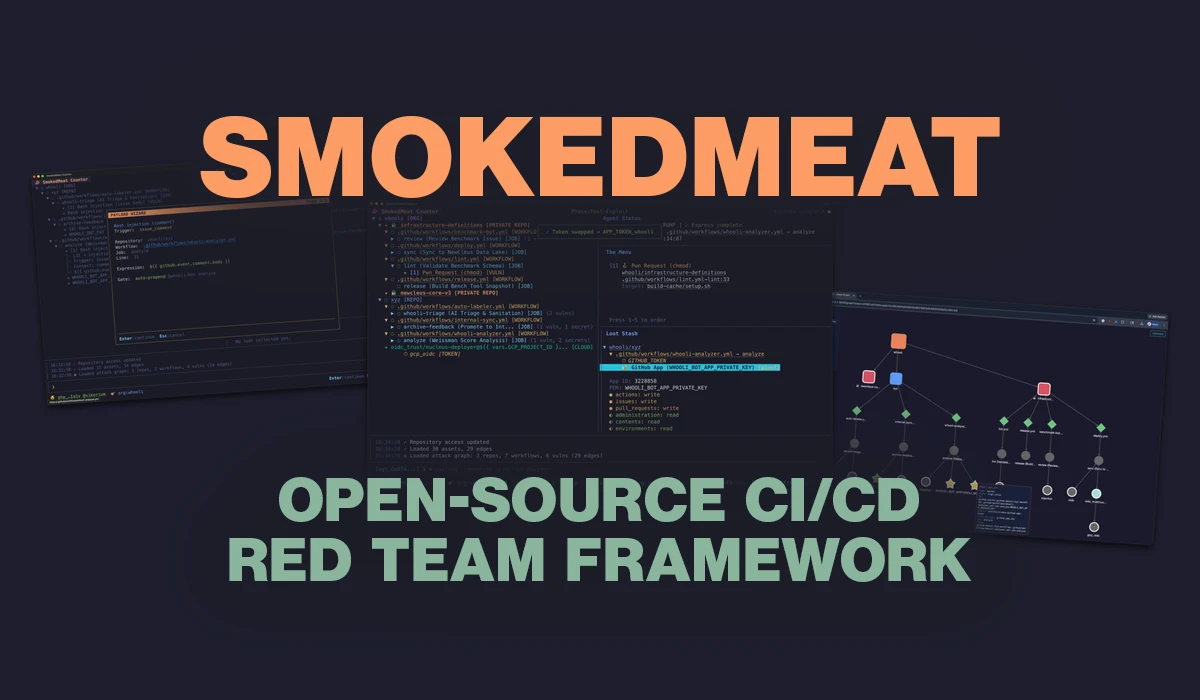
SmokedMeat, created by Boost Security, is an open-source framework designed to demonstrate attack scenarios within Continuous Integration/Continuous Deployment (CI/CD) pipelines. This innovative tool allows engineering and security teams to see firsthand how an attacker might exploit vulnerabilities in their specific environment.
Starting with a flagged pipeline vulnerability, SmokedMeat executes a live demonstration against a team's infrastructure. It deploys a payload, compromises the runner, and even harvests credentials from process memory. From there, it can exchange those credentials for cloud access, expose private repositories, and help map the potential blast radius of an attack.
Zaid Al Hamami, CEO of Boost Security, emphasizes the importance of this tool: "This tool is showing what attackers can do; they can find a vulnerability in an open-source repo, craft an exploit payload, steal credentials in that repo, and use those credentials to pivot to other areas, insert malware, and infect developers working on those repos."
The TeamPCP Attack That Changed the Conversation
In March 2026, a significant coordinated campaign known as TeamPCP compromised multiple tools, including Trivy and Checkmarx, alongside numerous npm packages. This attack utilized techniques that Boost Labs had previously documented. Notably, Boost's open-source scanner, Poutine, had flagged vulnerabilities in Trivy’s pipeline months before the attack occurred, but those vulnerabilities remained unpatched.
Al Hamami described this incident as the largest cascade supply chain attack to date, highlighting the urgency of addressing vulnerabilities in CI/CD environments.
The Backlog Problem
Boost Labs has been documenting CI/CD attack techniques for years, illustrating how attackers navigate build pipelines, steal credentials, and pivot into cloud environments. A static scan result that flags a potential workflow injection does not effectively convey the rapid exploitation that can occur. Without concrete demonstrations, remediation efforts often fall to the wayside.
SmokedMeat aims to bridge this gap by running attack scenarios against actual infrastructure. This gives security teams and engineering leaders a clear view of what exploitation looks like in their own environments, ultimately leading to more prioritized remediation efforts.
Availability
SmokedMeat is available for free on GitHub, making it accessible for teams looking to enhance their security posture in CI/CD processes. As the landscape of cybersecurity continues to evolve, tools like SmokedMeat are essential for understanding and mitigating risks in software development workflows.
🔒 Pro insight: SmokedMeat's approach to simulating CI/CD attacks can significantly enhance vulnerability awareness and prioritize remediation efforts effectively.




