🎯Basically, your security systems might be missing important threats because they rely on one source of information.
What Happened
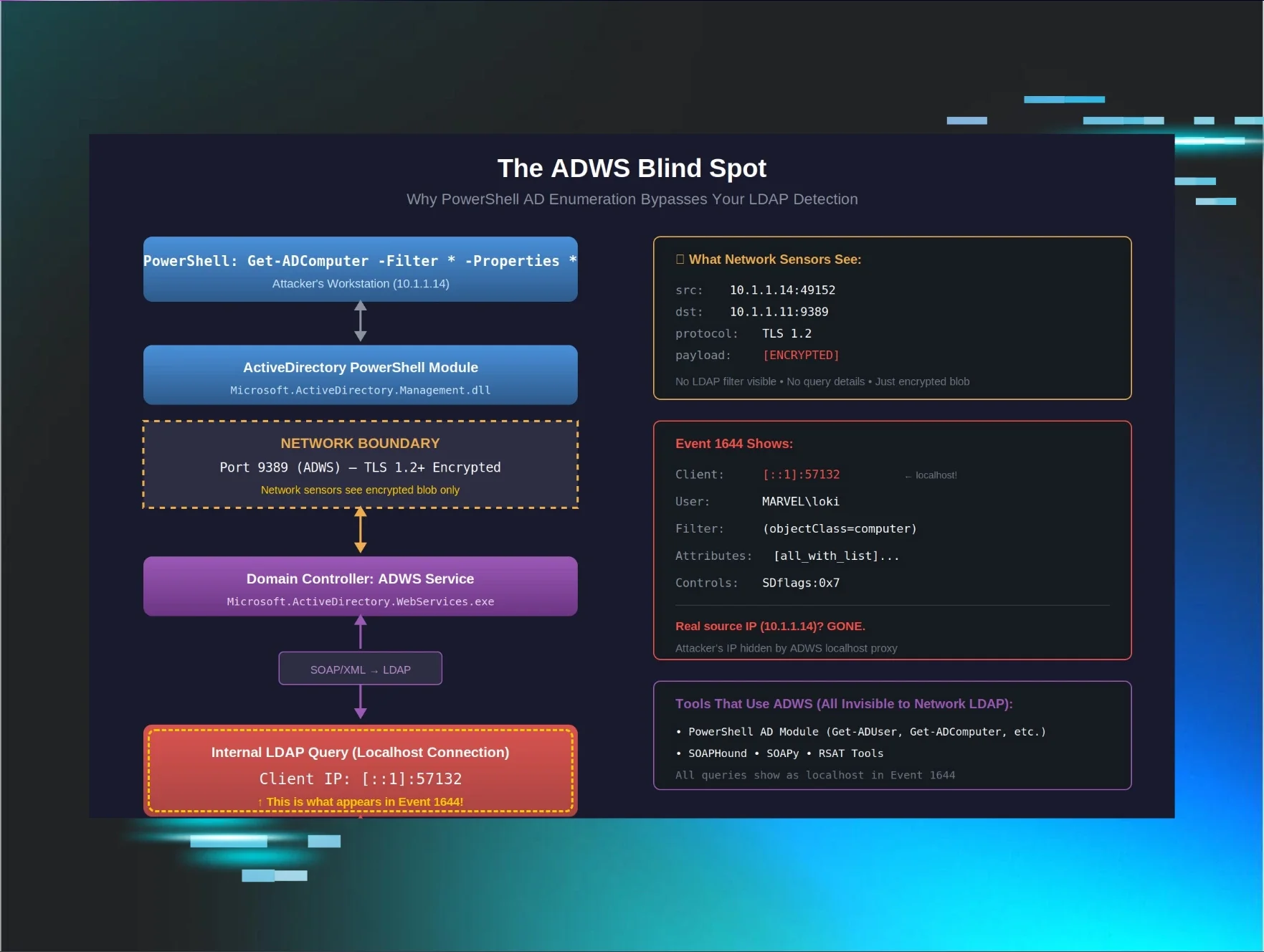
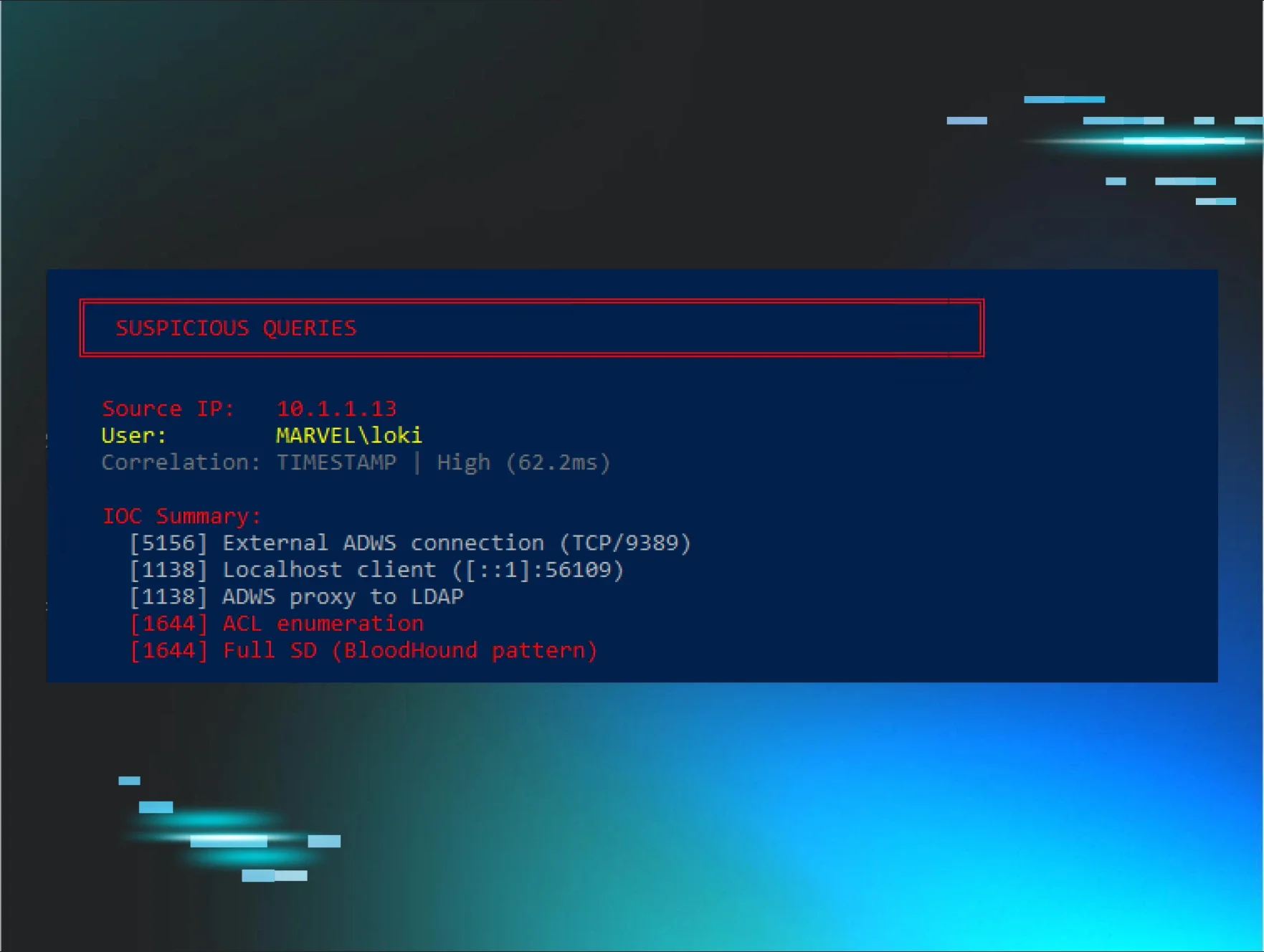
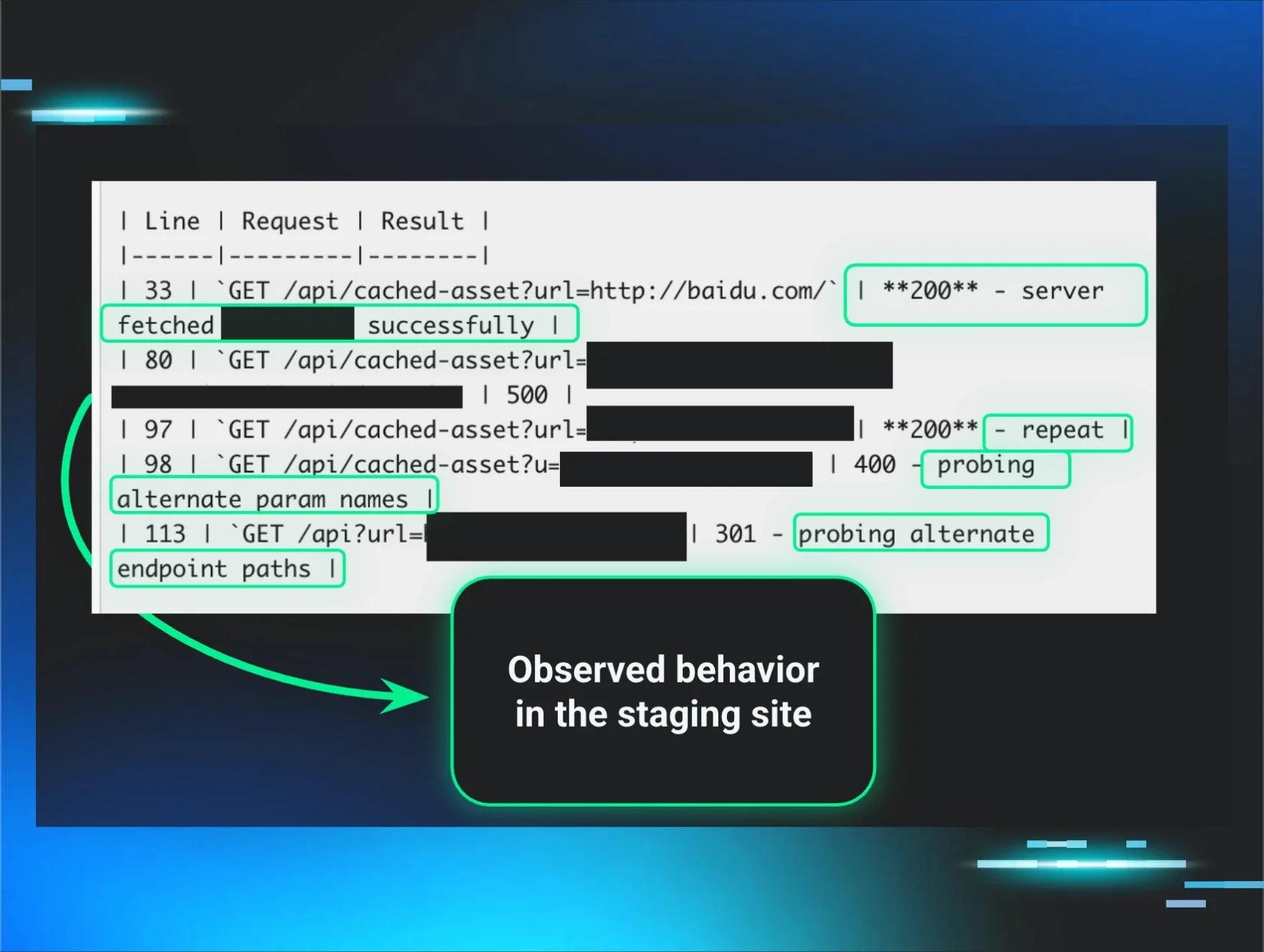
In the world of cybersecurity, telemetry is crucial for detecting and responding to threats. However, many organizations are relying on a single source of telemetry data, which can lead to significant blind spots. This reliance creates a dangerous situation where critical threats might go unnoticed, putting your entire system at risk.
During my years in Incident Response, I’ve seen firsthand how this single-source problem manifests. When organizations depend solely on one type of data, they miss out on a broader perspective. It’s like trying to drive a car while only looking through the rearview mirror — you might see some things, but you’re bound to miss what’s right in front of you.
The uncomfortable truth is that many security teams are not fully aware of the limitations of their telemetry systems. This lack of awareness can lead to inadequate responses during security incidents, leaving organizations vulnerable to attacks.
Why Should You Care
You might think, “This doesn’t affect me,” but consider how much you rely on technology every day. Your bank account, personal information, and even your job could be at stake if your organization isn’t properly monitoring for threats. If your security team is only looking at one source of data, they may not catch a breach until it’s too late.
Imagine you’re at a party, and you only listen to one friend’s account of the event. You might miss important details from others that could change your understanding of what’s happening. In cybersecurity, missing data can lead to catastrophic outcomes. It’s essential for your organization to gather insights from multiple sources to ensure a comprehensive view of potential threats.
What's Being Done
Cybersecurity experts are beginning to recognize the importance of diversifying telemetry sources. Organizations are encouraged to adopt a multi-faceted approach to data collection. Here are some immediate actions you can take:
- Integrate multiple telemetry sources to gain a holistic view of your environment.
- Conduct regular tabletop exercises to identify gaps in your detection capabilities.
- Educate your security team about the limitations of relying on a single data source.
Experts are watching to see how organizations adapt to these challenges. The next steps will likely involve implementing advanced analytics and machine learning to enhance detection capabilities across diverse data sets.
🔒 Pro insight: Organizations must prioritize multi-source telemetry to enhance detection capabilities and minimize blind spots in threat response.