🎯Basically, attackers often exploit poorly configured VPNs to gain unauthorized access to networks.
What Happened
VPN misconfigurations are a significant vulnerability in many organizations, leading to 70% of cyber intrusions. As cybercrime continues to grow, attackers are increasingly targeting these overlooked areas. The Huntress Security Operations Center (SOC) has observed that many breaches start with attackers logging in through compromised VPN credentials.
Who's Affected
Organizations of all sizes are at risk, especially those with small IT teams or limited resources. Industries like healthcare, law, and local businesses often lack the robust security measures needed to protect against these vulnerabilities. The average security team is small, with many organizations relying on just a few individuals to manage cybersecurity.
What Data Was Exposed
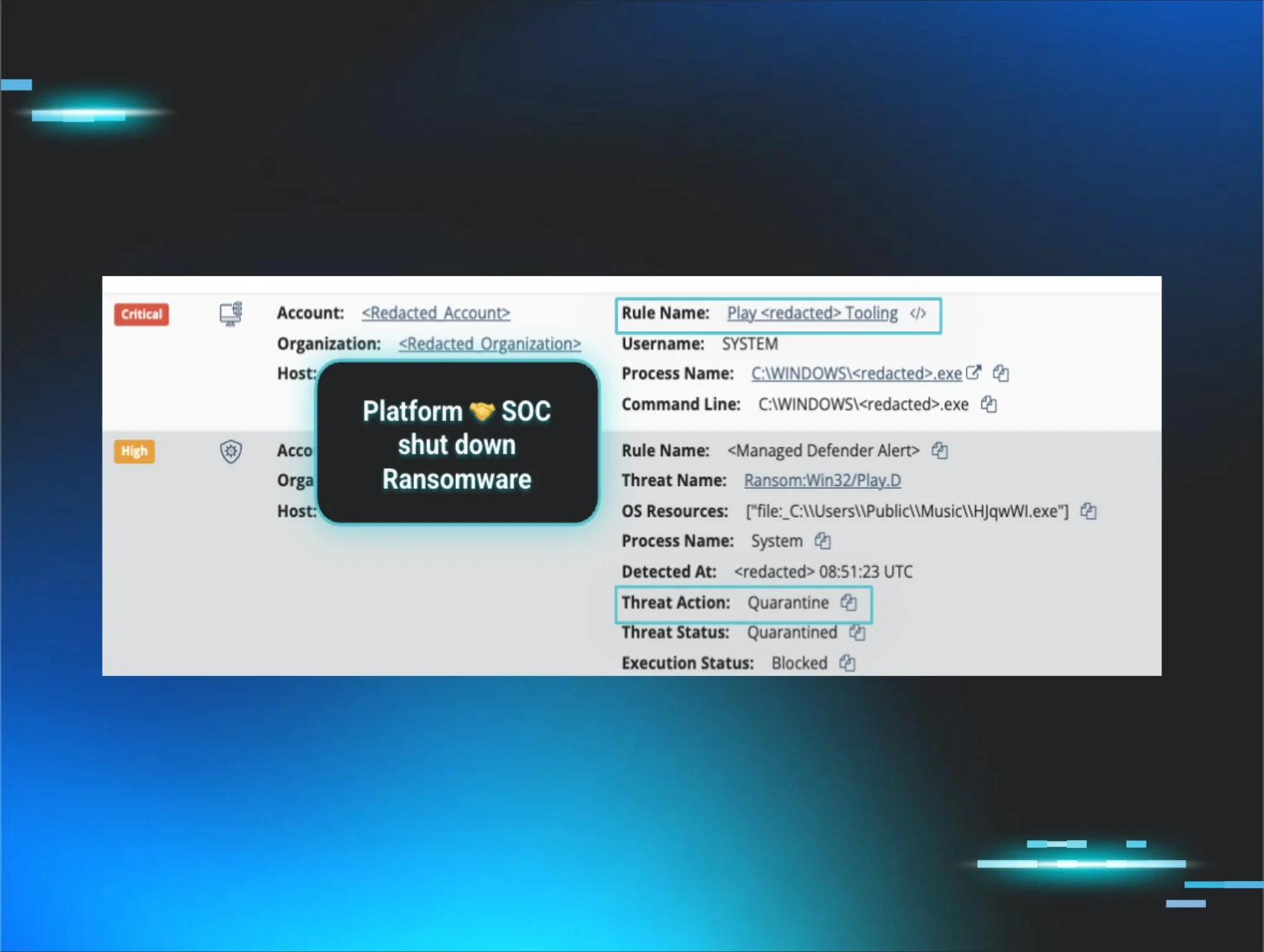
While the specific data exposed varies by incident, attackers often gain access to sensitive information, including personal and financial data. In some cases, they can escalate their access to critical systems, leading to potential ransomware deployment.
What You Should Do
To mitigate these risks, organizations should take immediate action: By prioritizing these actions, organizations can significantly reduce their vulnerability to cyber intrusions through VPN misconfigurations.
Containment
- 1.Implement Multi-Factor Authentication (MFA): This is the most effective step to prevent unauthorized VPN access.
- 2.Audit Privileged Accounts: Review and remove unnecessary admin rights to limit access.
- 3.Disable Legacy Accounts: Old accounts can be easy targets for attackers.
Remediation
- 4.Centralize Logging: Ensure all VPN activity is logged to aid in investigations.
- 5.Monitor for Anomalies: Set up alerts for unusual login attempts to catch intrusions early.
🔒 Pro insight: The reliance on VPNs without proper security measures creates a critical attack vector that adversaries are increasingly exploiting.





